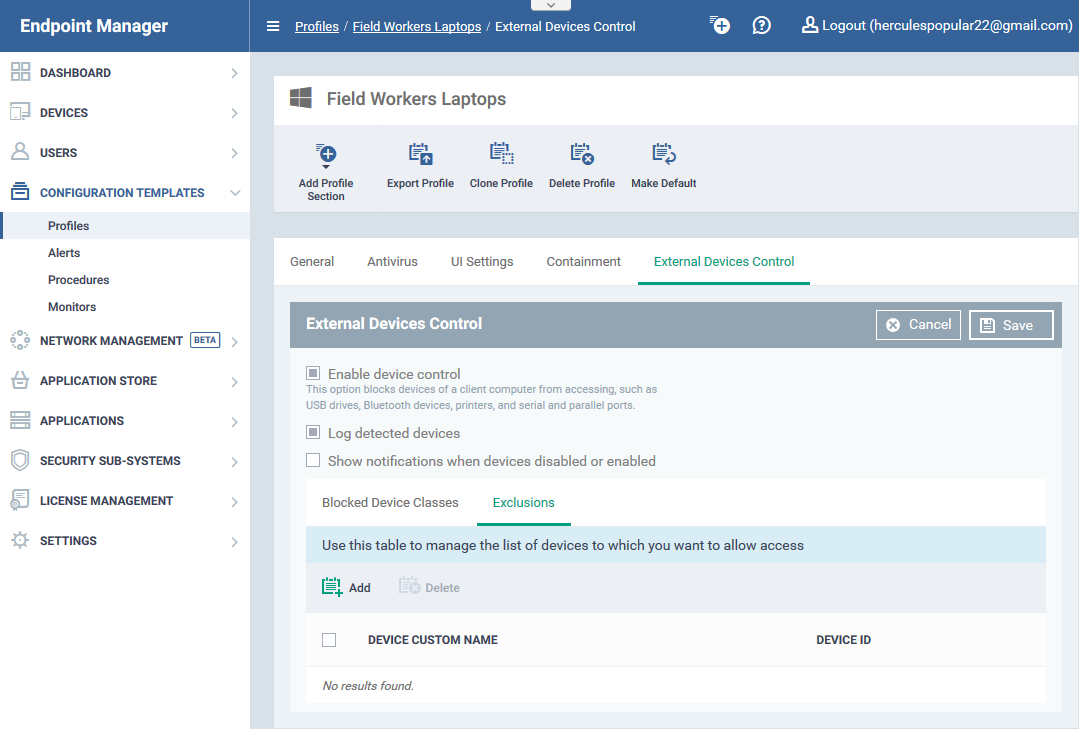
Click ‘Configuration Templates’ > ‘Profiles’ > open a Windows profile > Open/Add ‘External Device Control’
- The external device control section lets you block certain types of devices from connecting to managed endpoints.
- For example, you can block access to USB storage devices, Bluetooth devices, infrared devices, IDE ATA/ATAPI controllers.
- You can also create exceptions to allow specific devices to connect.
Process in brief
- Log into ITarian
- Click ‘Applications’ > ‘Endpoint Manager’
- Click 'Configuration Templates' > 'Profiles'
- Open the Windows profile applied to your target devices
- Open the 'External Devices Control' tab
OR
- Click 'Add Profile Section' > 'External Devices Control' (if it hasn't yet been added)
- Click ‘Edit’
- Select 'Enable device control'
- Choose banned device types in the ‘Blocked Device Classes’ tab
- Create exceptions for specific devices in the ‘Exclusions’ tab
- Click 'Save' for your settings to take effect
Process in detail
- Log into ITarian
- Click ‘Applications’ > ‘Endpoint Manager’
- Click 'Configuration Templates' > 'Profiles'
- Open the 'External Devices Control' tab
OR
- Click 'Add Profile Section' > 'External Devices Control' (if it hasn't yet been added)
The settings pane allows you to:
External device control settings
- Enable devices control – Activate or deactivate device access control
- Log detected devices – If enabled, any connection attempts by blocked device types are logged. You can view these logs at 'Security Sub-Systems' > 'Device Control’.
- Show notifications when devices disables or enabled – If enabled, an alert is shown to end-users when a device connection is blocked.
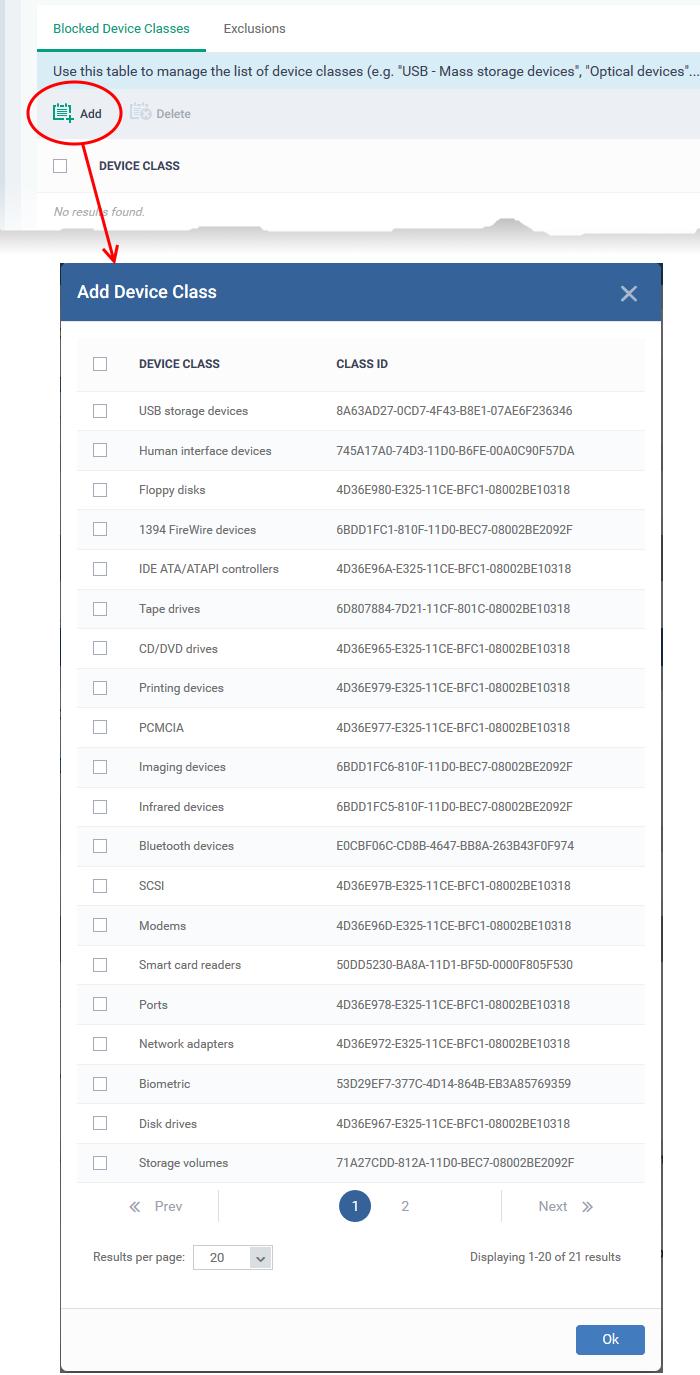
Add blocked device types
- Click the 'Blocked Device Classes' tab
- Click 'Add'
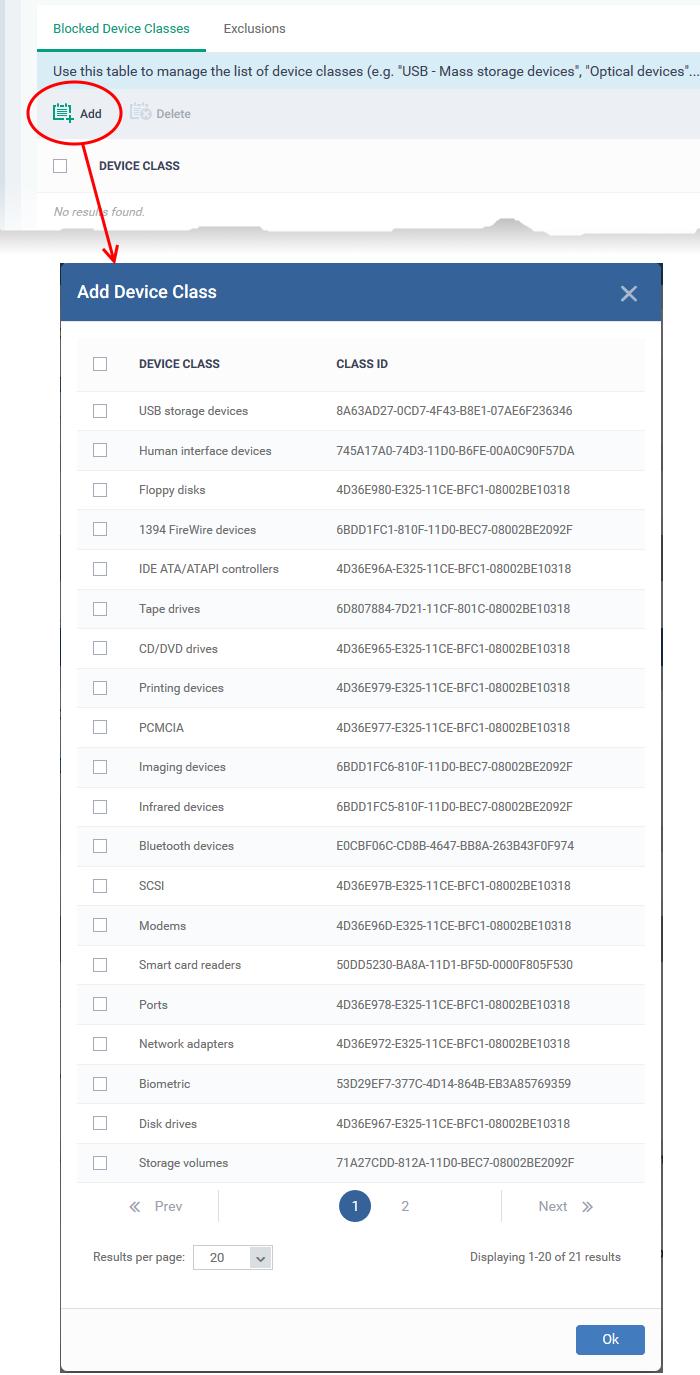
- Select the class of device you want to block then click 'Ok'.
- Repeat the process to add more device types.
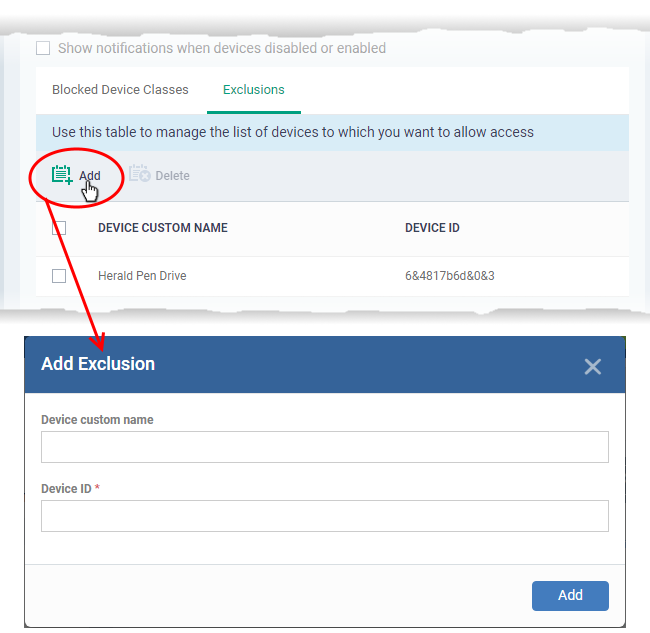
Exclusions
The exclusions tab lets you choose specific devices which are allowed to connect, even though you have banned the device class to which they belong. For example, you might ban the class ‘USB Storage devices’, but create an exception to allow your USB VPN tokens.
- Click the 'Exclusions' tab
- Click 'Add'
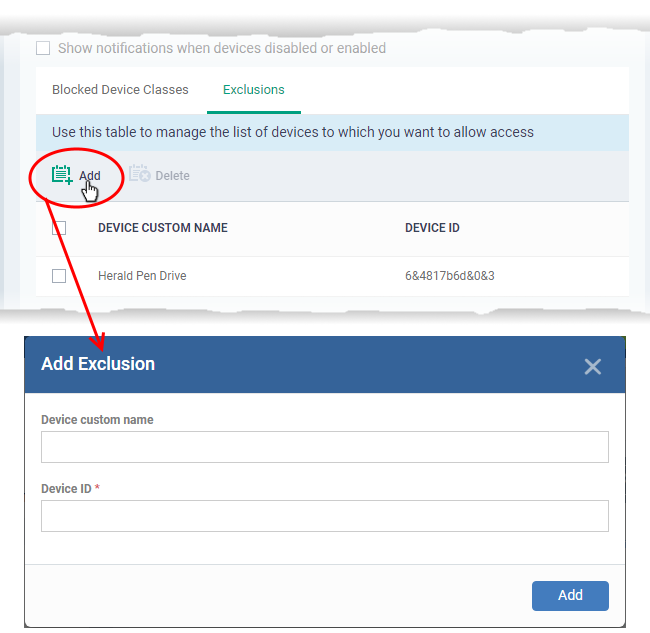
- Enter a label for the device in the 'Device Custom Name' field (optional)
- Enter the unique device identifier in the 'Device ID' field
- Example. If you want to block all USB storage devices apart from the type of SANDISK devices used by your company, you could specify a device exclusion ID of 'USBSTOR/DISK&VEN_SANDISK/4C5310'.
- You can find the ID of any connected devices at ‘Security Sub-systems’ > ‘Device Control’ > ‘Hardware Path’ column.
- You can use a wildcard character '*' if you want to cover a range of devices with similar IDs. For example, to include all USB storage devices whose IDs start with “4C5310”, you could enter:
USBSTOR/DISK&VEN_SANDISK/4C5310*
The device will be added to the exclusions list and allowed to connect to endpoints.
- Click 'Save' for your settings to take effect.