Endpoint Manager lets you manage OS updates and patches for 3rd party apps on Windows devices.
- This topic explains how to review and manage the patches of an individual device.
- Alternatively, you can manage all patches for all devices at ‘Applications’ > ‘Patch Management'.
View device patches
OS patches
Install OS patches
3rd party patches
Install 3rd party patches
Further reading
View device patches
- Login to ITarian
- Click ‘Applications’ > ‘Endpoint Manager’
- Click ‘Devices’ > ‘Device List’ > 'Device Management'
- Select a company or group to view only their devices
OR
- Select 'Show all' to view every device enrolled to Endpoint Manager
- Click the Windows device you want to check
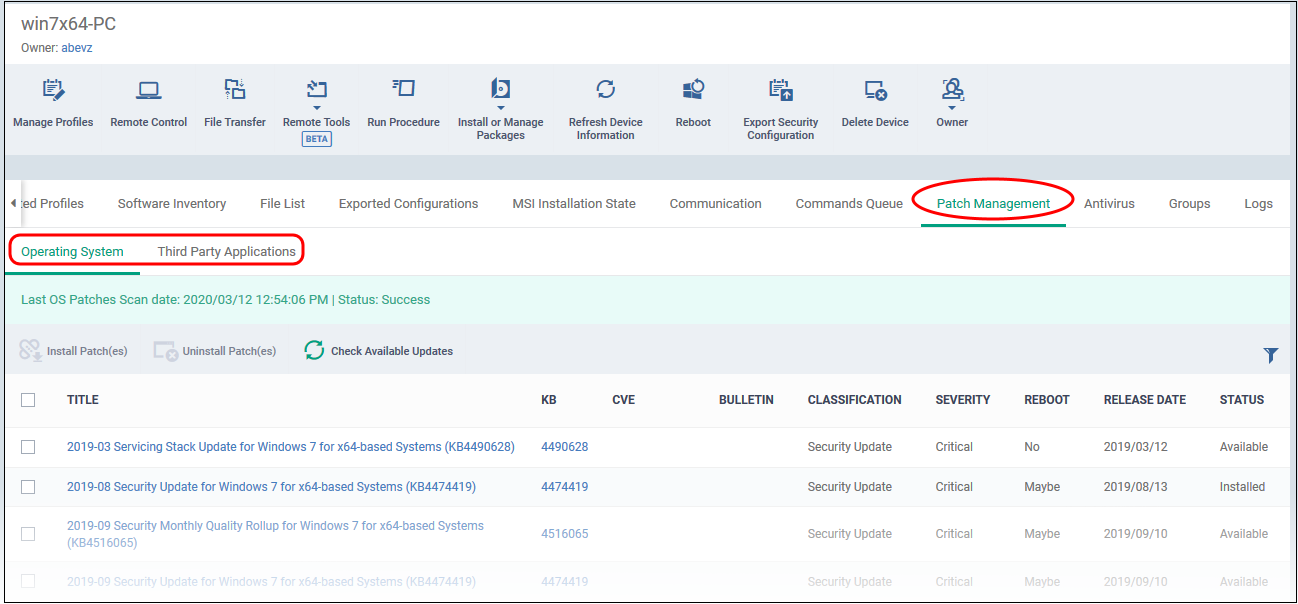
- Click the 'Patch Management' tab
There are two sub-tabs – ‘Operating Systems’ and ‘Third Party Applications’
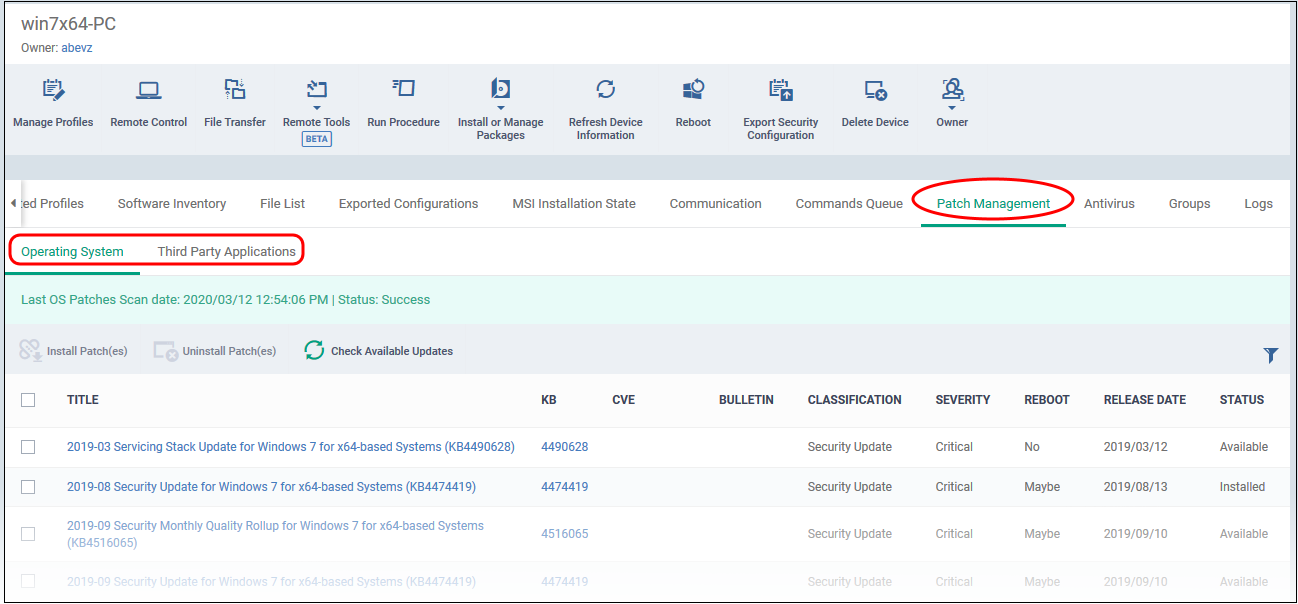
OS patches
- Click the ‘Operating System’ tab if it is not already open
The screen shows all installed OS updates, and those that are pending install. Details about the most recent OS patch scan is shown in a green bar above the table.
Column details:
Title – The name of the patch. Click the name to view patch details.
KB – The Microsoft knowledgebase article that describes the patch. Click the number to view the article.
CVE - The common vulnerabilities and exposures (CVE) entry number. Click the number to view details such as summary, vulnerability type, published date, vendor, affected devices and more.
Bulletin – The Microsoft bulletin number that contains details about the patch.
Classification – The category of the patch:
- Update - Fixes a specific, non-critical problem. This type of patch does not address security-related bugs.
- Definition update - Updates to a product's internal database. For example, an update to the virus signature database for Windows Defender.
- Critical Update - Fixes a specific, critical OS problem or a critical security-related bug
- Security update - Fixes a version specific, security related vulnerability
- Update rollup - A collection of updates, hotfixes, security updates and critical updates packaged together for easy deployment. These updates generally target a specific Windows component.
- Driver - Adds software for controlling peripherals or add-on devices that could be connected to the endpoint
- Feature pack - Adds new functionality distributed after an OS release.
- Service pack - Contains a collection of updates, hotfixes, security updates, critical updates and additional fixes.
- Tool - Installs a utility or feature for a specific task or a set of tasks.
- Upgrades - Updates the Windows OS version on the endpoint to the latest build.
Severity – The criticality of the patch. Can be ‘Critical’, ‘Important’, ‘Low’, ‘Moderate’ or ‘Unspecified’. We recommend installing all ‘Critical’ and ‘Important’ updates.
Reboot – Whether or not the endpoint requires a restart to complete the patch installation.
Release Date – The date on which the patch was made available by Microsoft
Status – Indicates whether the patch is installed, not yet installed, or installed but the endpoint needs rebooting.
Install OS patches
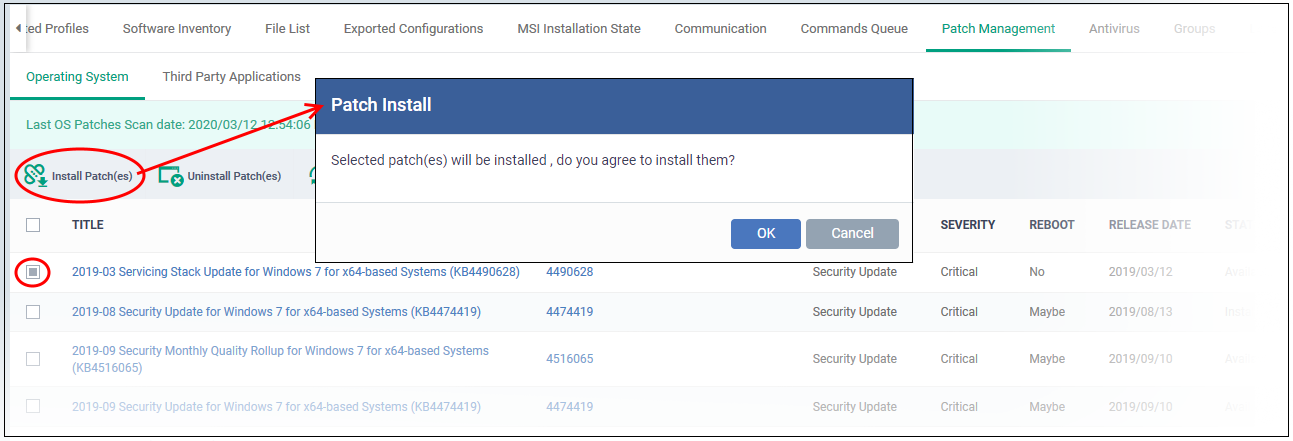
- Select patches marked as ‘Available’ in the status column
- Click ‘Install Patch(es)’ above the table:
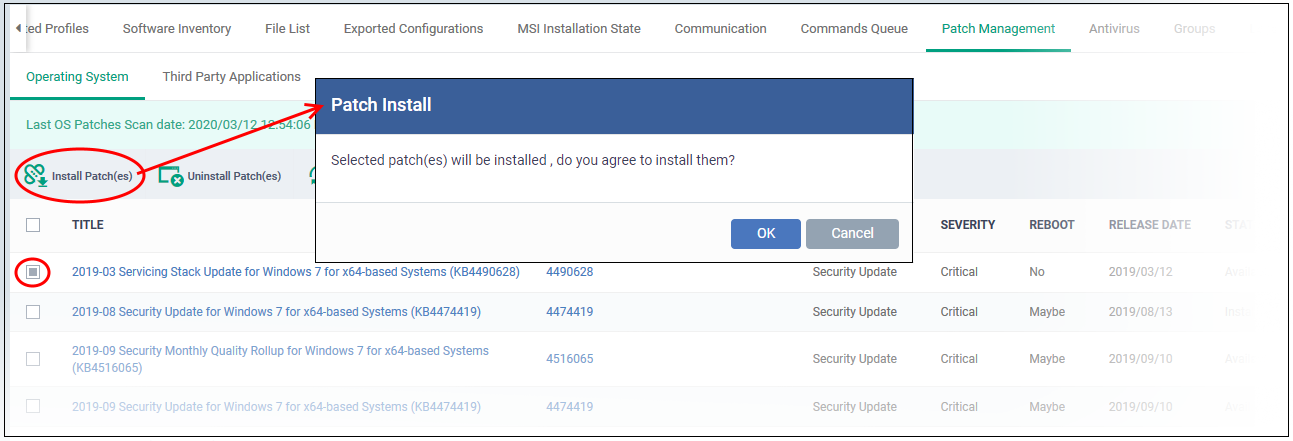
The patch command is immediately sent to the selected endpoint. Some patches may require a restart to complete the installation.
- Check the status column. Restart the endpoint if the status is ‘Reboot Pending’.
3rd party patches
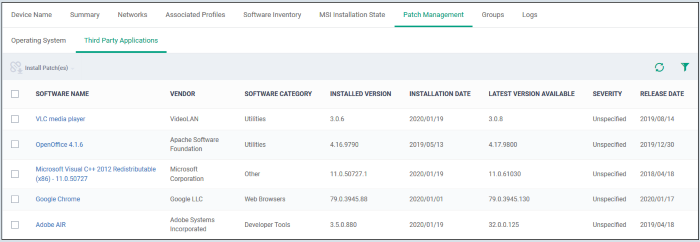
Select the ‘Third Party Applications’ tab
- The communication client on the endpoint analyzes all 3rd party applications installed on the endpoint.
- The checked locations include 'C:\Program Files\' and 'C:\Users\{user}\AppData\' folder so as to cover all applications in the endpoint, installed on locations other than their default location.
- The client reports the applications and their patch status to Endpoint Manager.
- The 'Patch Management' tab lists all available patches for applications on the endpoint.
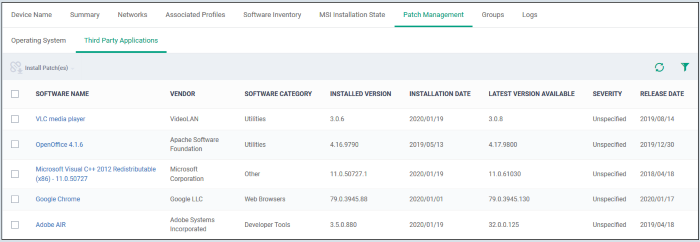
Software Name – The label of the third party application. Click the name to view patch details and a list of all devices on which it is required.
Vendor – The publisher of the application.
Software Category – The type, or genre, of application
Installed Version – The version number of the application currently available on the endpoint.
Installed Date – The date on which the application was deployed on the endpoint.
Latest Version Available – The most recent version of the application made available by the publisher.
Severity - The criticality of the patch. Can be ‘Critical’, ‘Important’, ‘Low’, ‘Moderate’ or ‘Unspecified’. We recommend installing all ‘Critical’ and ‘Important’ updates.
Release Date – The date at which the latest version was made available by the publisher.
Install third party patches
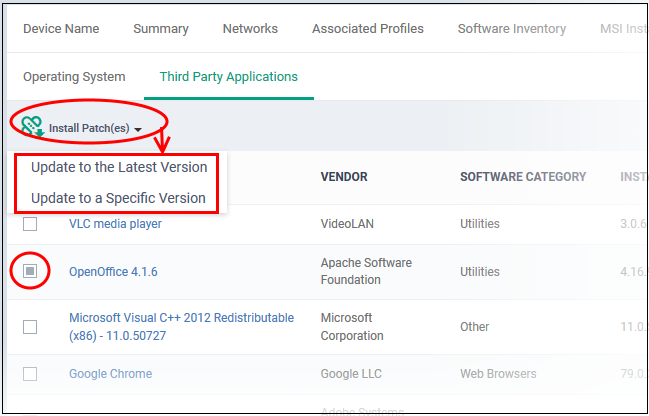
- Select the target patches then click ‘Install Patch(es)’:
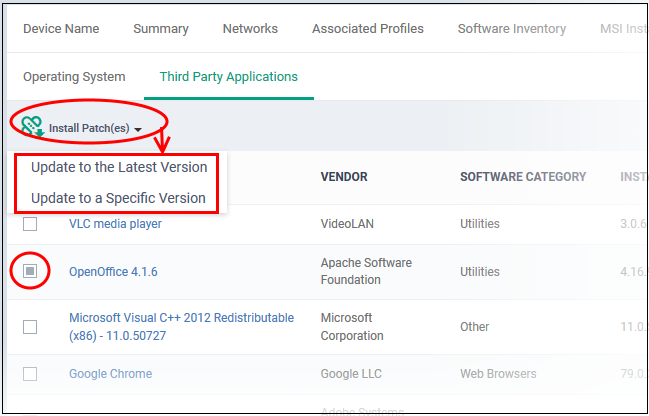
- Update to the latest version – Installs the most recent patch / update released by the publisher
- Update to a specific version – Select the version you want to install. This is only available if you select one patch to install. It is not available if you want to install multiple, different patches.
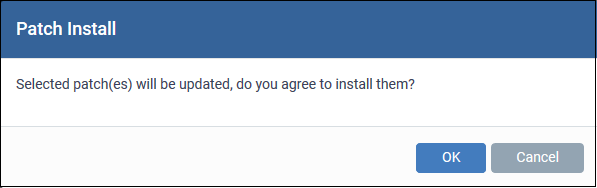
Click ‘OK’ in the confirmation dialog:
The command is immediately sent to the selected endpoint.
Further reading
Install and manage patches on Windows devices – Use the full patch manager to review and install available patches for all Windows devices.