Remote Control lets you take-over Windows and Mac OS devices to solve issues, install third-party software and run system maintenance.
This article explains how to enable or disable remote permissions by profile or by role.
Process in brief:
Configure permissions by profile:
Configure permissions by role:
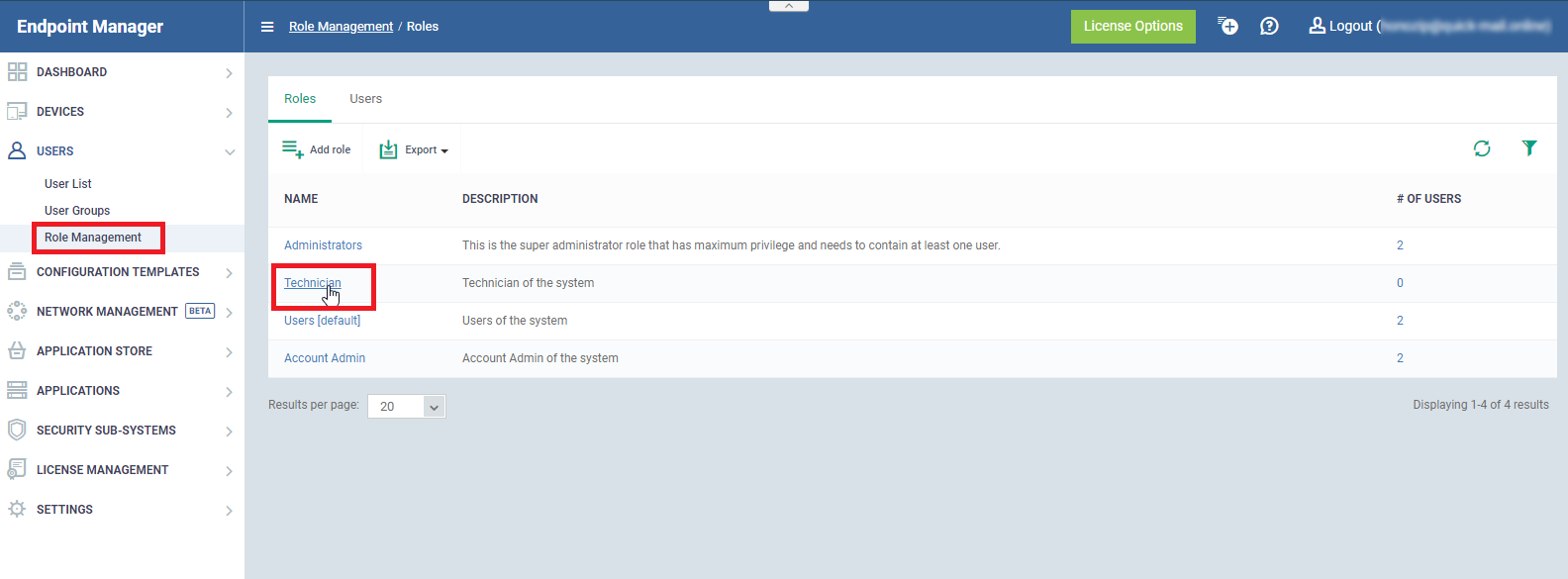
- Click ‘Users’ > ‘Role Management’ > ‘Roles’
- Click on the role you want to configure
- Open the ‘Role Permissions’ tab
- Enable or disable remote access software permission as required
- The ‘In detail’ section has a list of the permissions related to remote access
Process in detail:
Configure permissions by profile
- Login to ITarian
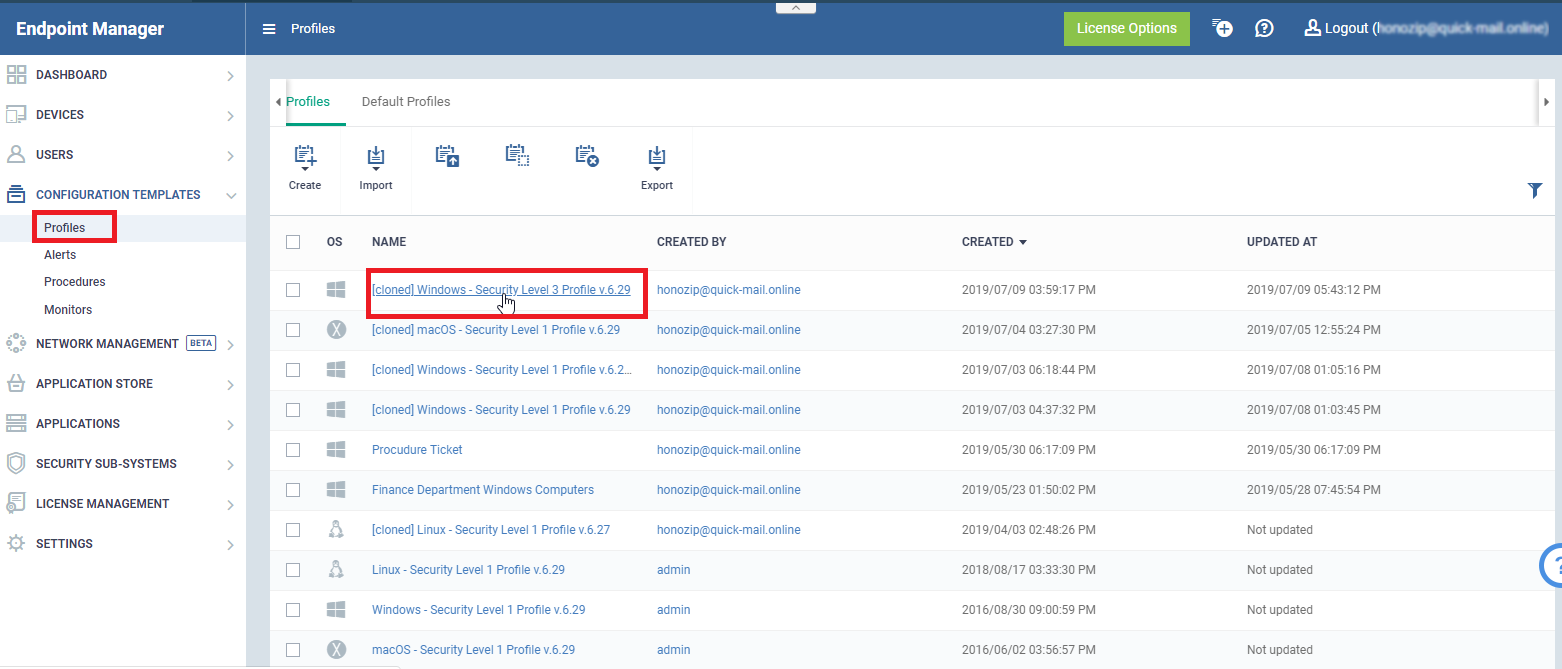
- Click ‘Applications’ > ‘Endpoint Manager’
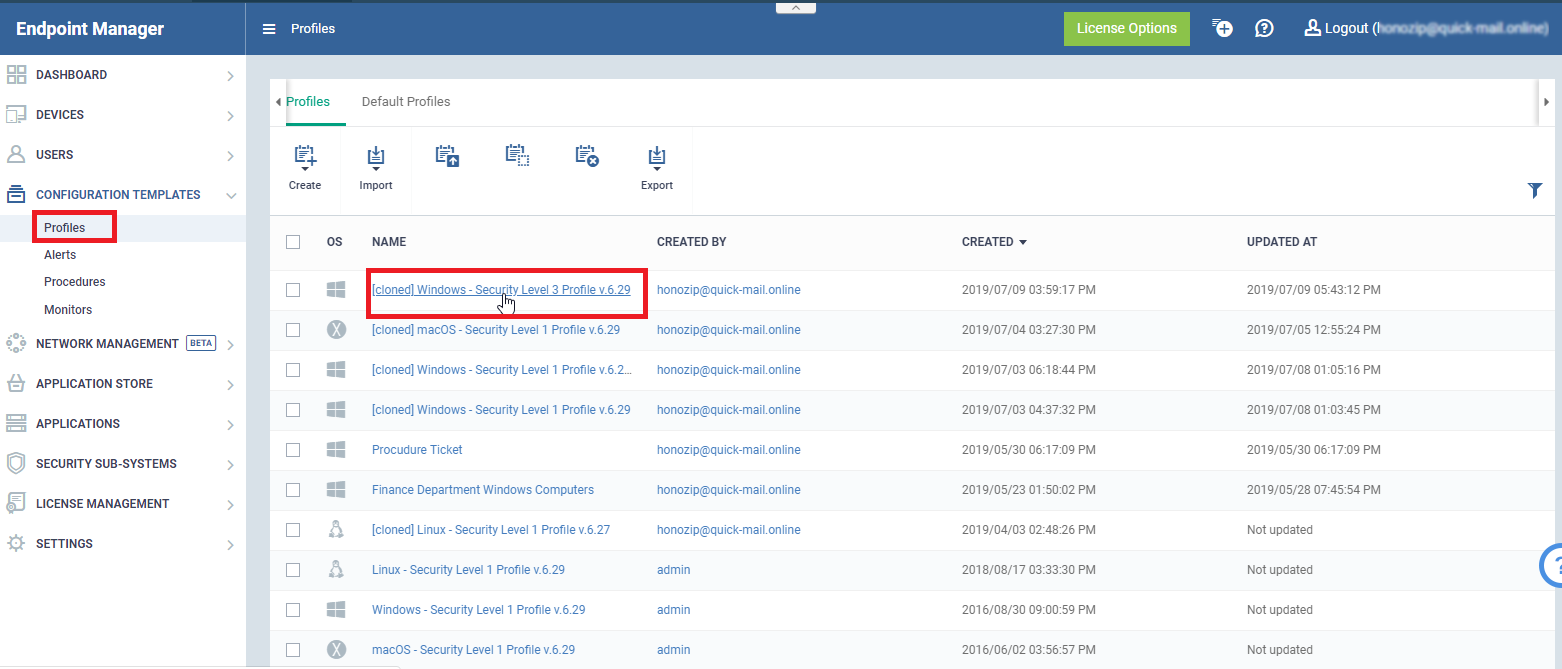
- Click ‘Configuration Templates’ > ‘Profiles'
- Click the name of the Windows or MAC profile that you want to work on
- Click 'Remote Control' tab (or click ‘Add Profile Section’ > ‘Remote Control’)
- Click ‘Edit’
- Note - ‘Device Takeover’ and ‘File Transfer’ are independent of each other. You can disable device takeover and still enable file transfer operations.
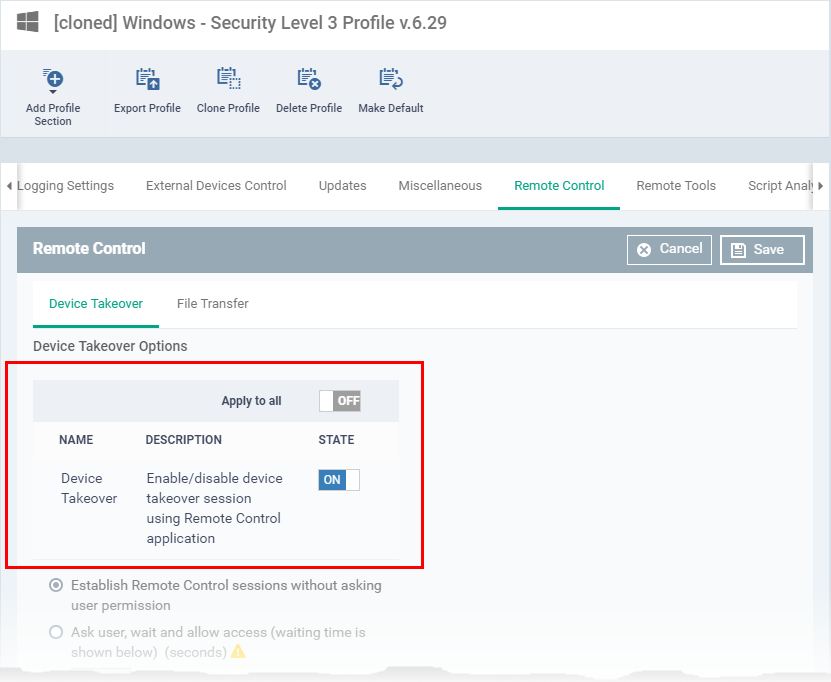
‘Device Takeover’ tab
- ‘Device Takeover’ gives you full control of the remote device like a traditional RDP connection.
- For example, you can move your mouse around the remote desktop, open programs, configure the control panel, etc.
- Use the ‘ON/OFF’ switch to allow or block remote control of devices on the profile:
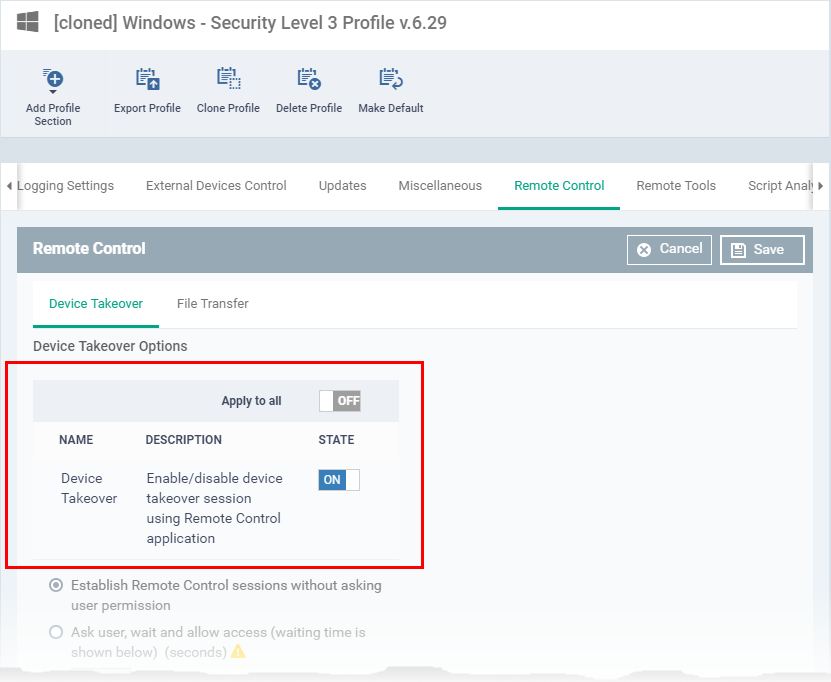
- Click ‘Save’ to apply your changes
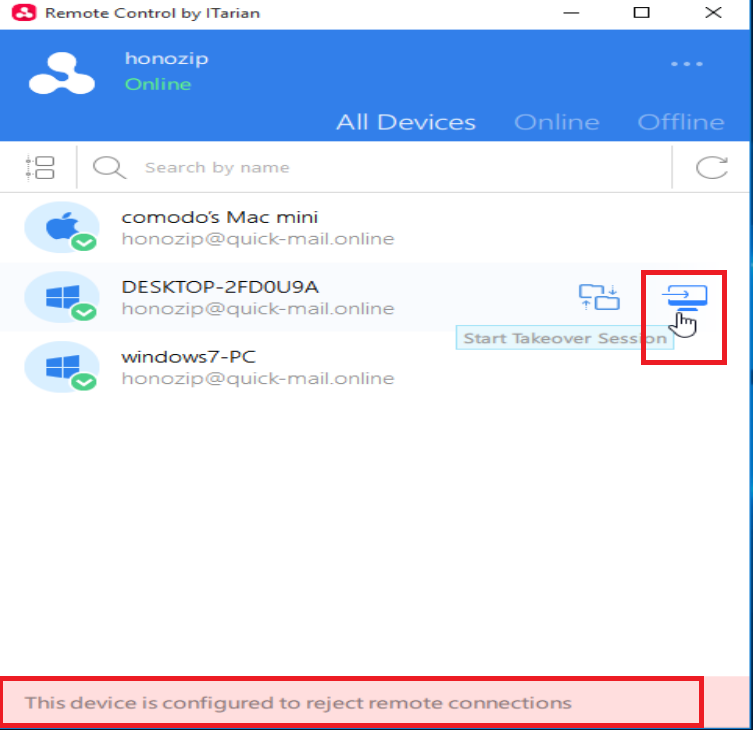
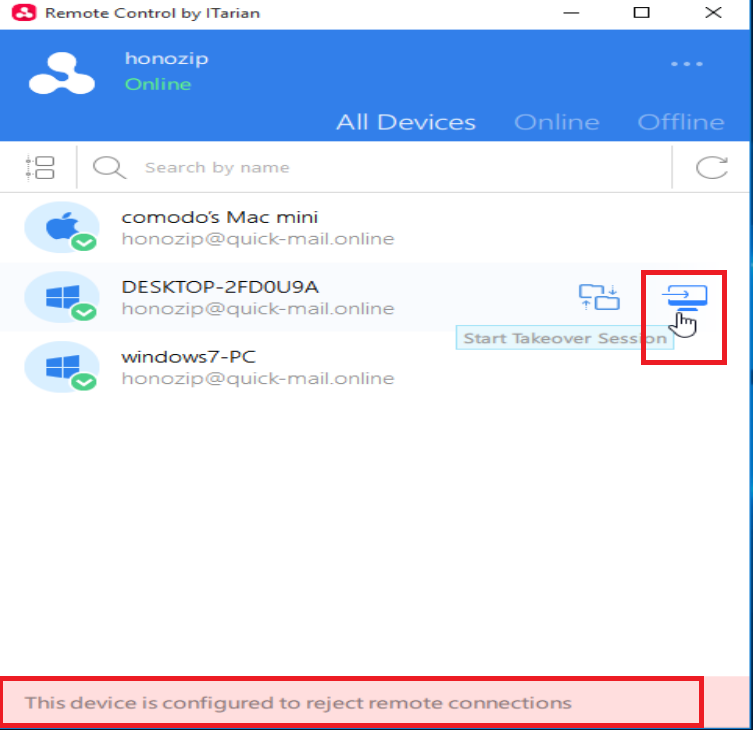
- Test the new setting:
- Click ‘Devices’ > ‘Device List’ > select an affected endpoint > Click the ‘Remote Control’ button
- You will see the following message if you attempt a takeover:
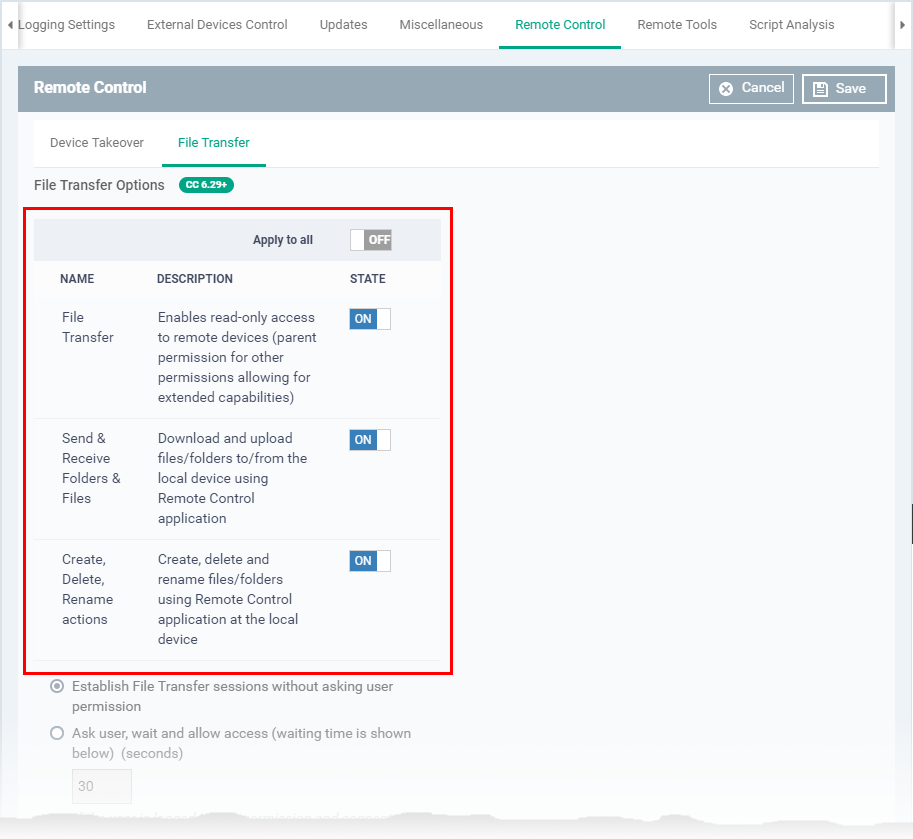
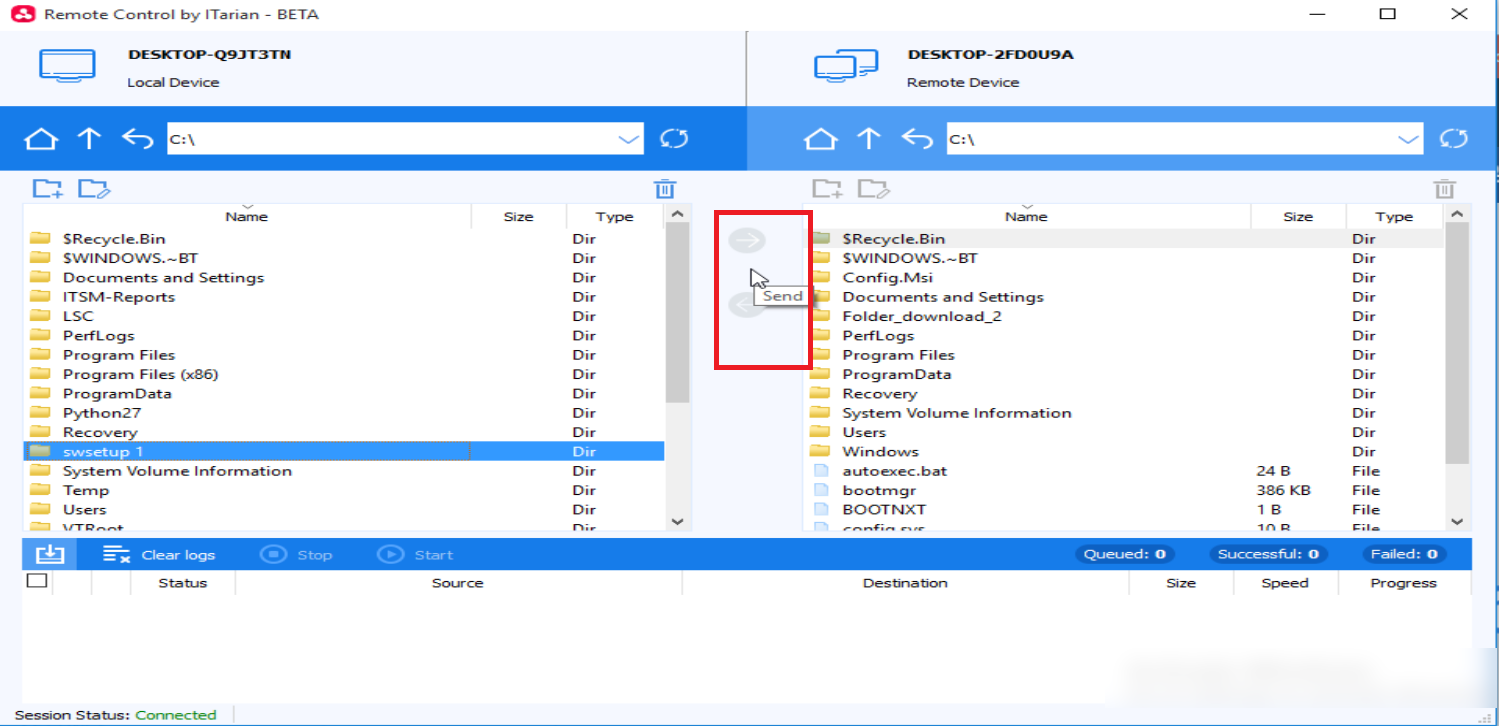
‘File Transfer’ tab – Use the ‘ON/OFF’ switches to allow or block various file activities:
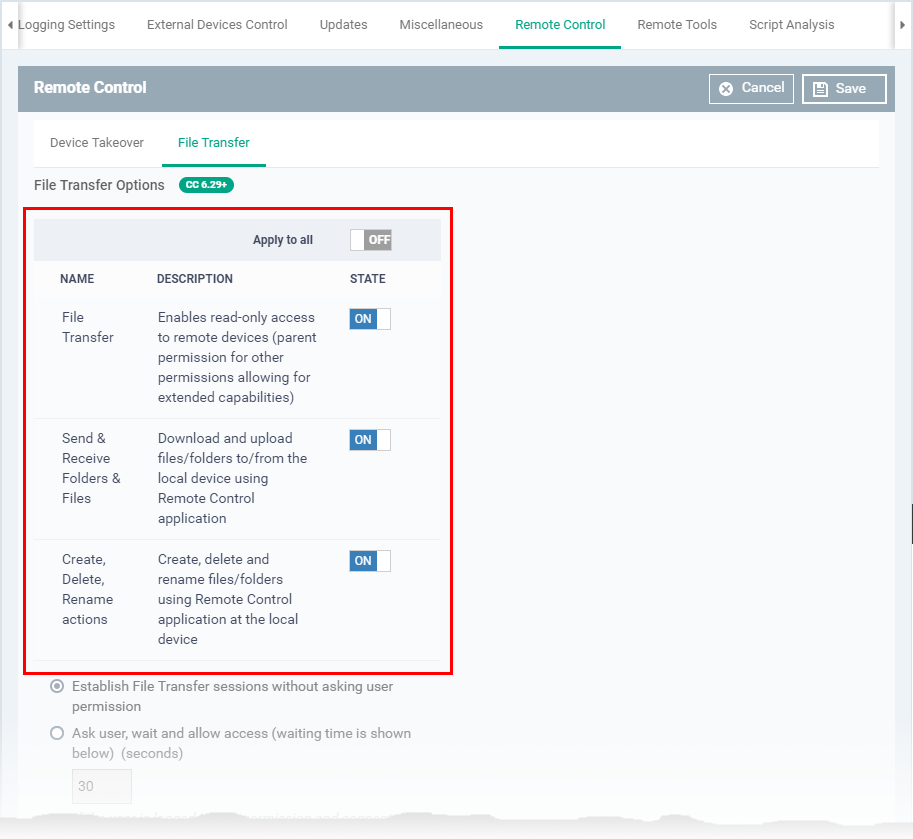
- Click ‘Save’ to apply your changes
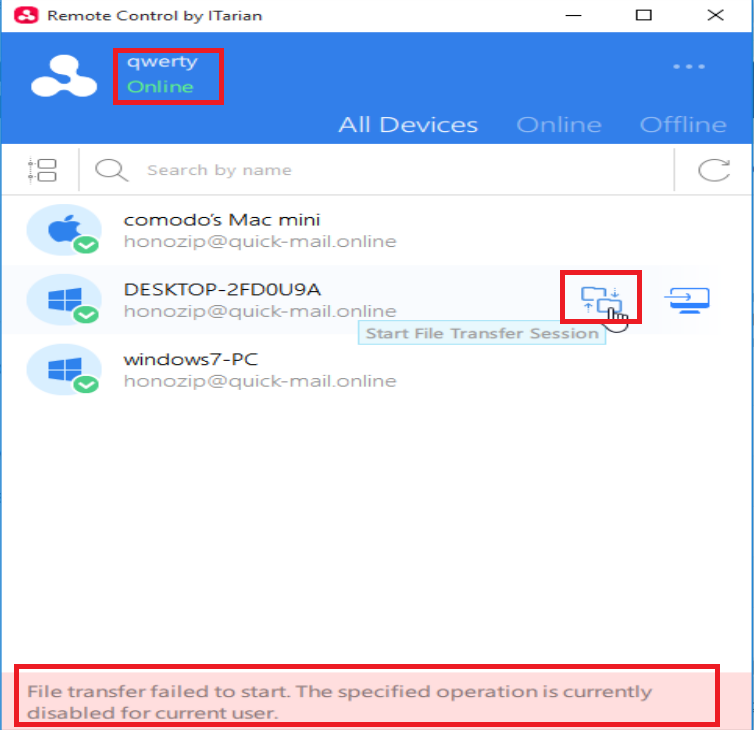
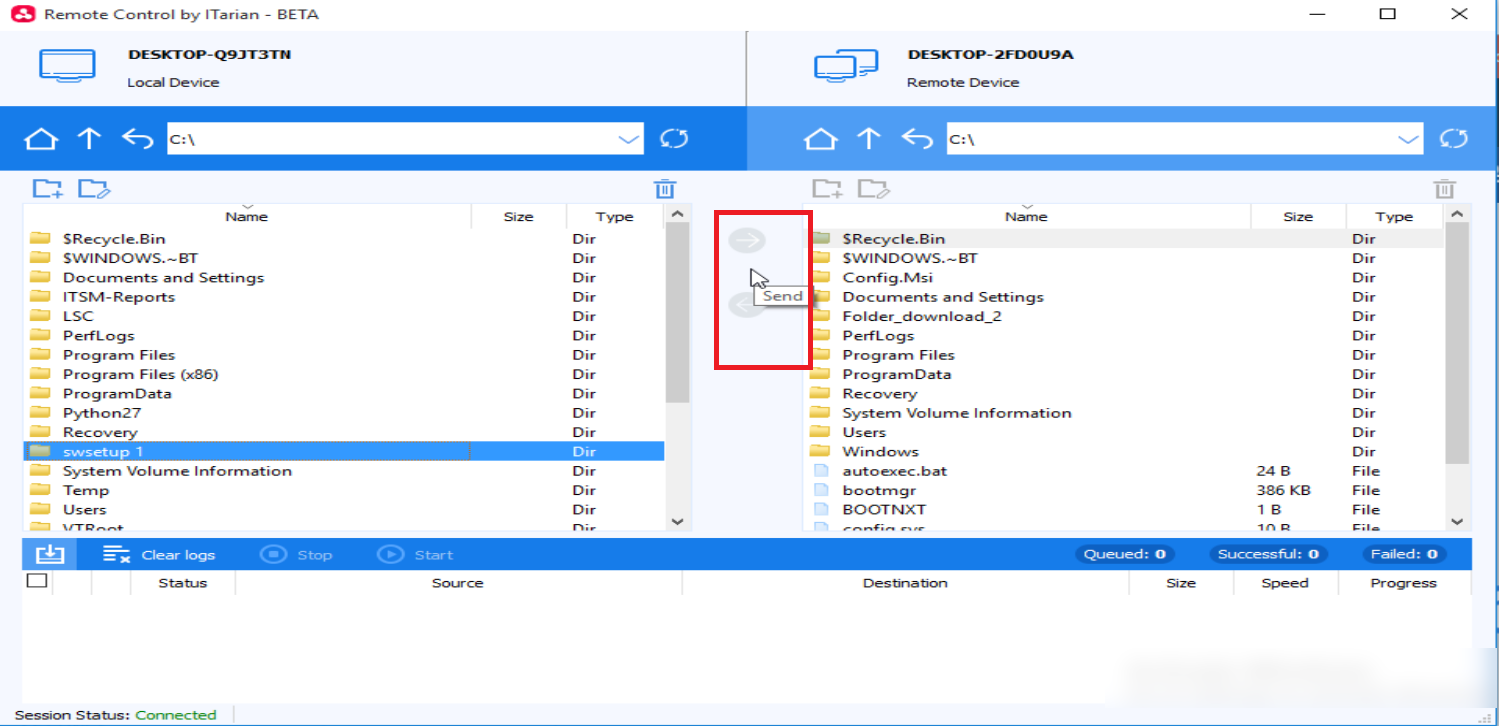
- Test the new setting:
- Click ‘Devices’ > ‘Device List’ > select an affected endpoint > Click the ‘File Transfer’ button
- Any activities you disabled are grayed out:
Configure permissions by role
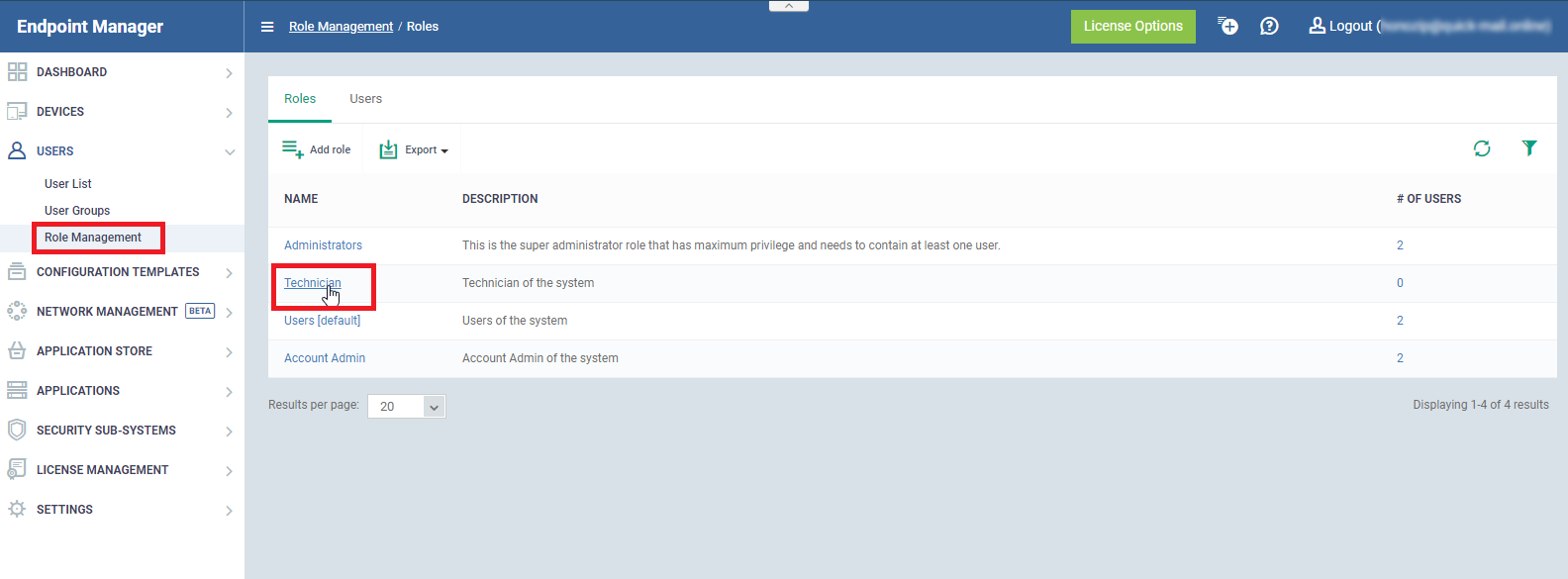
- Click ‘Users’ > ‘Role Management’
- Click the ‘Roles’ tab
- Click on the role you want to configure:
- Open the ‘Role Permissions’ tab
- Enable or disable remote access permission as required
- The following permissions relate to remote access:
|
Name
|
Determines the ability to:
|
|
inventory.devices.actions.remote_control
|
Connect to remote devices at all
|
|
inventory.devices.actions.remote_control.file_transfer
|
View files on the remote device
|
|
inventory.devices.actions.remote_control.file_transfer.crud
|
Copy / read / update /delete (CRUD) files on the remote device
|
|
inventory.devices.actions.remote_control.file_transfer.download
|
Copy files from the remote device to the local device
|
|
inventory.devices.actions.remote_control.file_transfer.upload
|
Copy files from the local device to the remote device
|
|
inventory.devices.actions.remote_control.takeover
|
Assume control of the remote device
|
- The permissions above have a parent-child relationship. You must enable the parent to configure the child.
- The hierarchy is as follows:
Inventory.devices.actions <master permission >
|
|__ inventory.devices.actions.remote_control
|
|__ inventory.devices.actions.remote_control.file_transfer
| |
| |__ inventory.devices.actions.remote_control.file_transfer.crud
| |
| |__ inventory.devices.actions.remote_control.file_transfer.download
| |
| |__ inventory.devices.actions.remote_control.file_transfer.upload
|
|__ inventory.devices.actions.remote_control.takeover
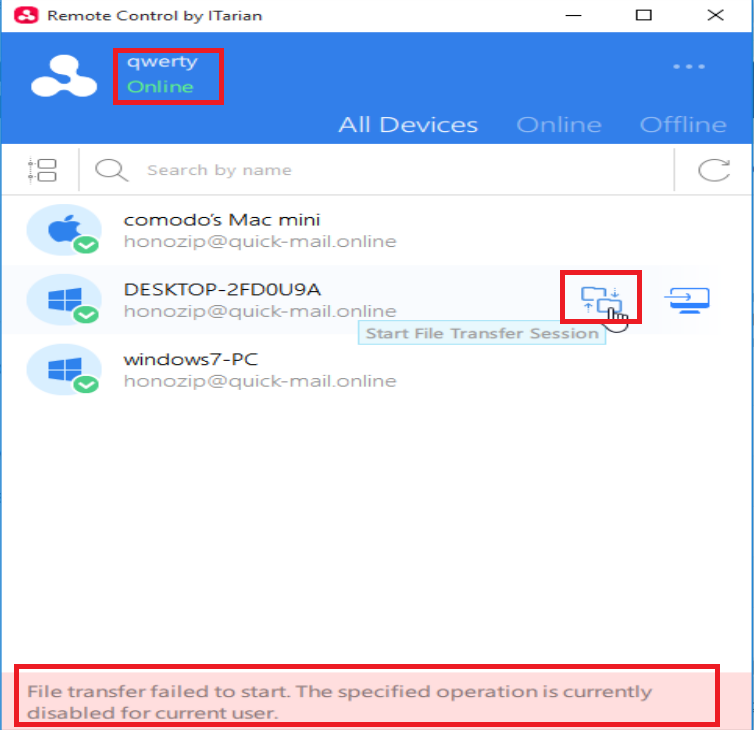
- Users with the affected role with see the following error if file transfers are disabled: