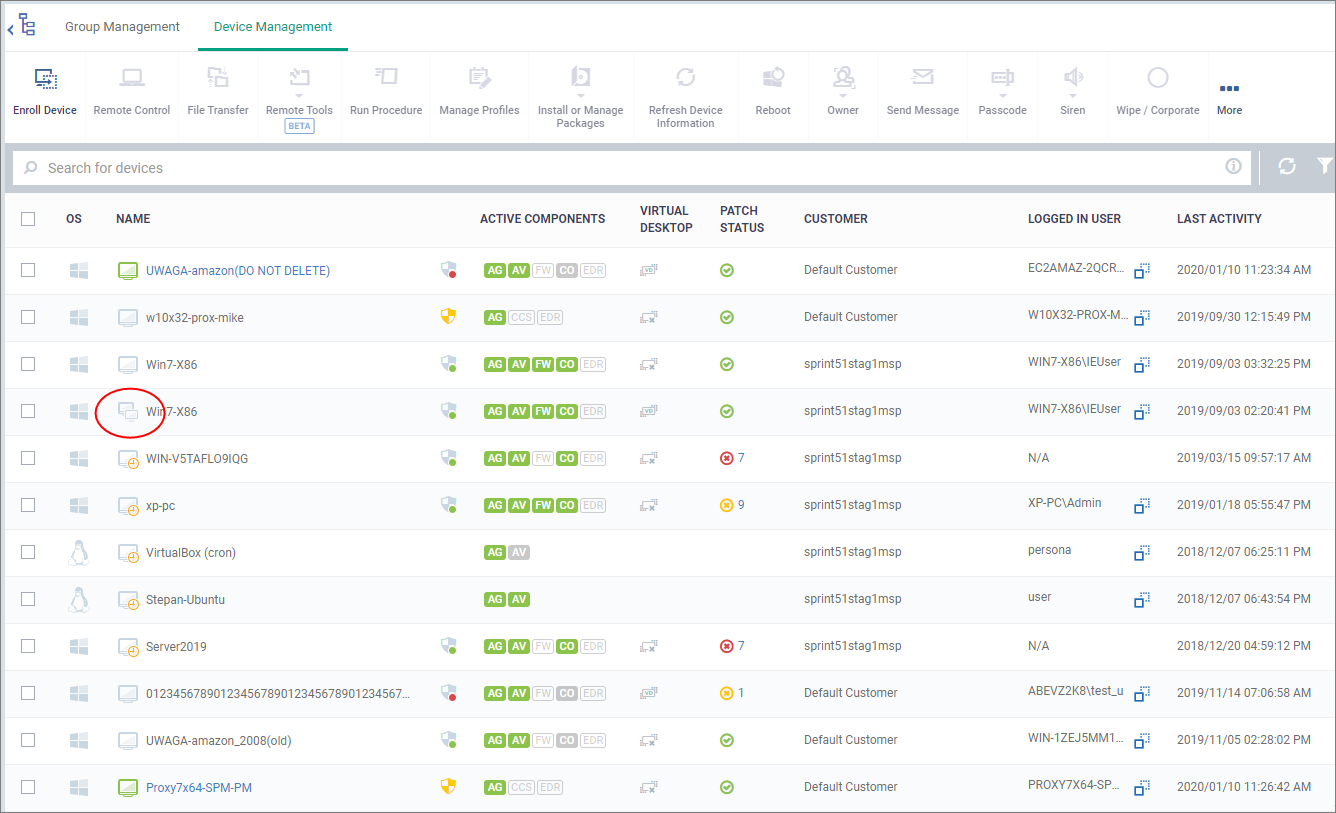
Open Endpoint Manager > click 'Devices' > 'Device List' > 'Device Management'
Endpoint Manager can detect and automatically remove inactive and duplicate devices.
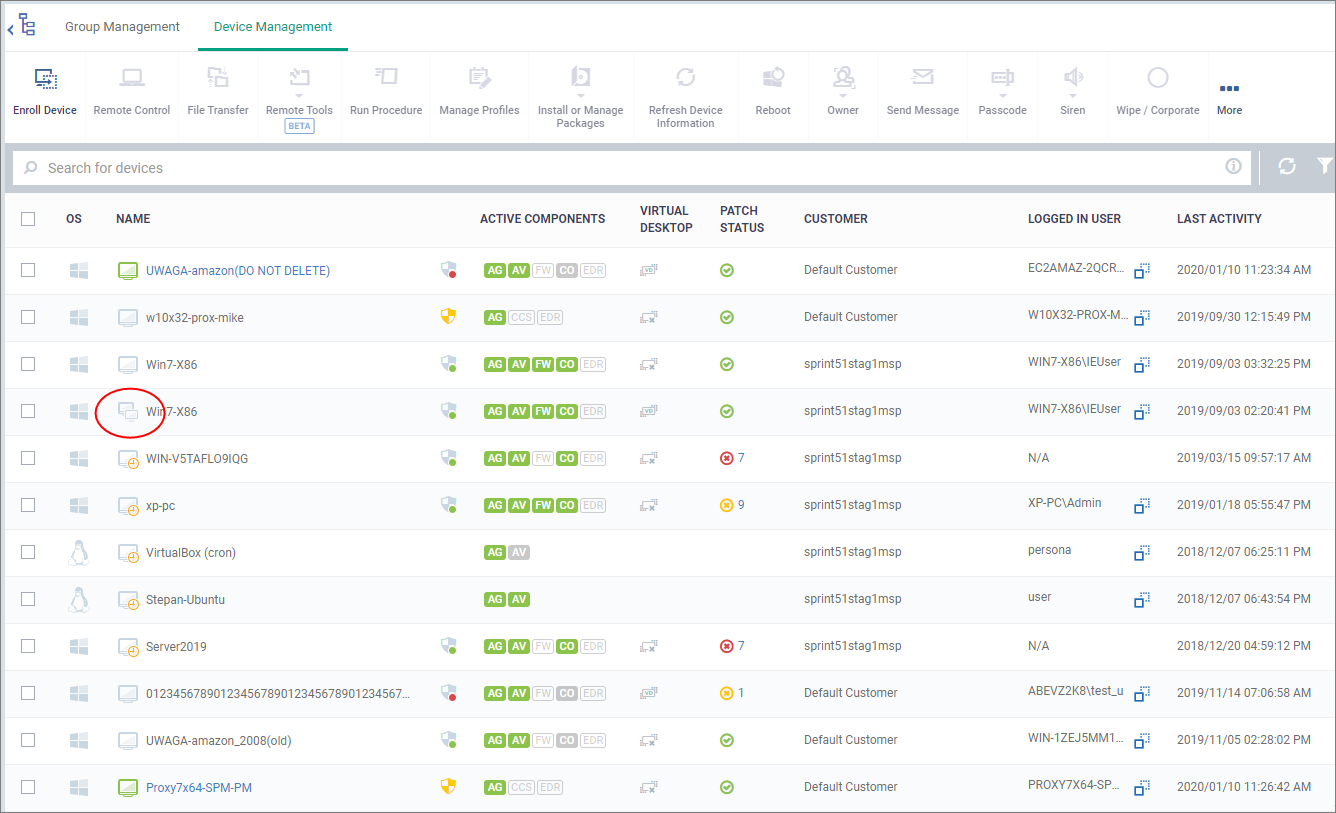
- Old devices are marked with the
 icon
icon
A device is marked as ‘old’ if it does not connect to EM for a certain length of time. You can choose this length of time, and how many days must pass before Endpoint Manager eventually removes it.
- Duplicate devices are marked with the
 icon
icon
A duplicate device is one that has the same name and / or same media access control (MAC) address as one or more other devices.
You can set EM to identify duplicate devices based on device name, MAC address or both.
You can also choose how many days must pass before Endpoint Manager removes duplicate devices.
Use the following links for more help:
View inactive or duplicate devices
- Log into ITarian
- Click ‘Applications’ > ‘Endpoint Manager’
- Click 'Devices' > 'Device List' > 'Device Management'
Old devices are marked with  icon
icon

Duplicate devices are marked with  icon
icon
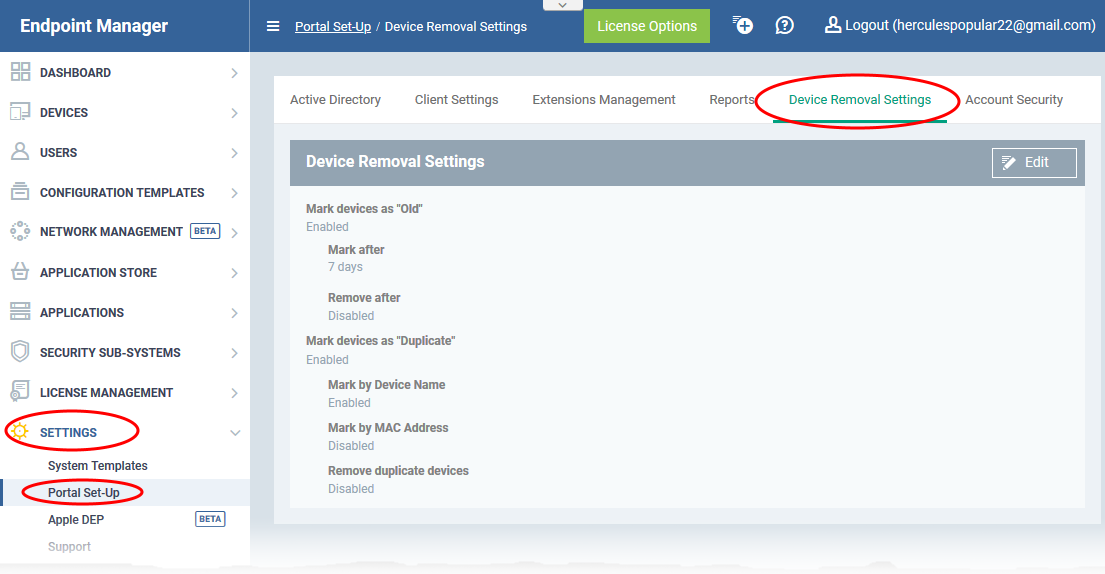
Device Removal Settings
- Click 'Settings' > 'Portal Set-up'
- Select the 'Device Removal Settings' tab:
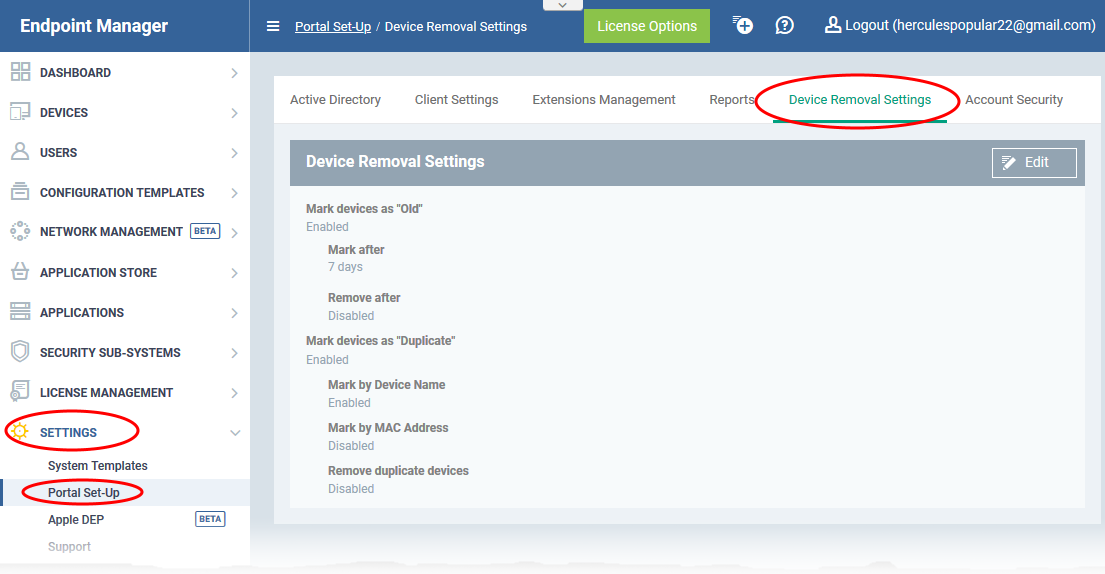
- Click 'Edit' on the right to configure the settings
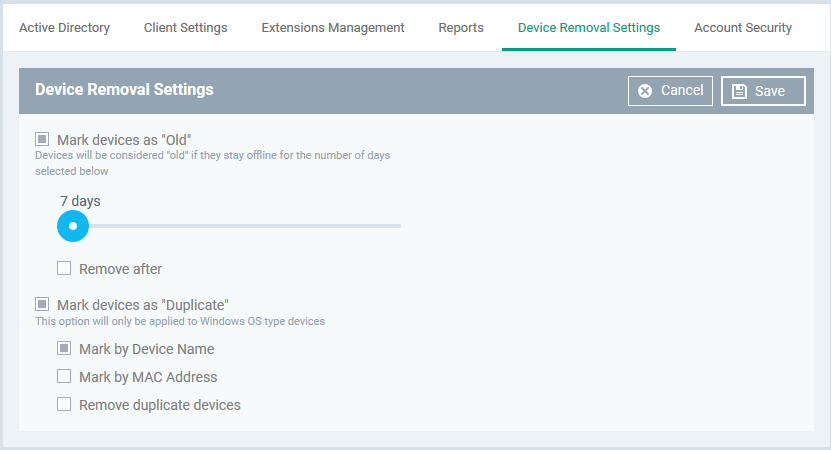
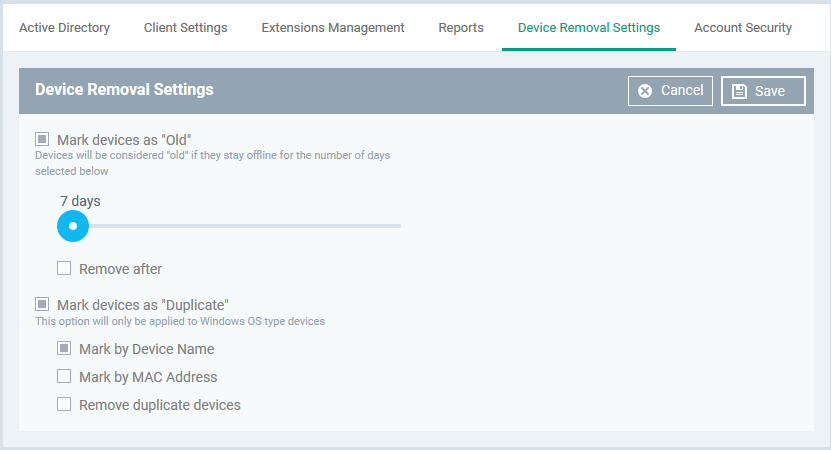
Mark devices as 'Old' - Use the slider to choose how many consecutive days of inactivity must pass before EM marks a device as 'Old'. A device is considered ‘inactive’ if it isn’t connected to Endpoint Manager.
- Remove after - Choose how many days the device should stay marked as 'Old' before EM removes it.
- If a device connects to EM within this period then it loses the 'old' status and is not removed.
- The ‘Remove after’ counter starts at the end of the ‘Mark devices as old’ period. So if you leave both at ‘90 days’, then the device will be removed after 180 days.
Mark devices as 'Duplicate' - A duplicate device is one that has the same name and / or same media access control (MAC) address as one or more other devices.
- Mark by Device Name – EM detects duplicates by their label.
- Mark by Mac Address - EM detects duplicates by their unique MAC address.
- If you select both, then EM marks duplicates only if both conditions are true.
Note - Endpoint Manager designates the most recently added device as the ‘Primary’ device in a set of duplicates. The primary device is kept/not deleted if you enable the ‘remove’ option. All other duplicates are removed.
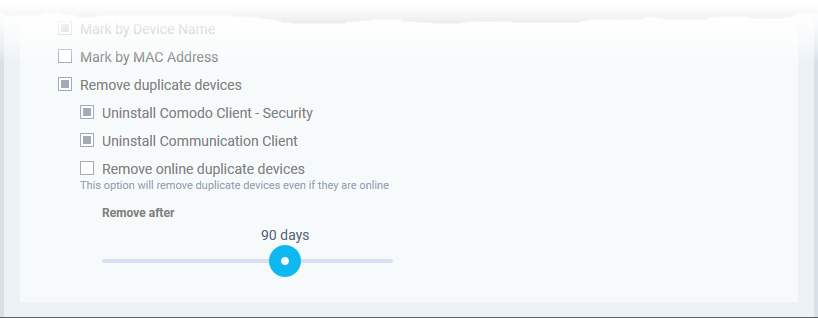
Remove duplicate devices - Use the slider at the bottom to choose how many days must pass before EM removes the device.The primary device is retained.
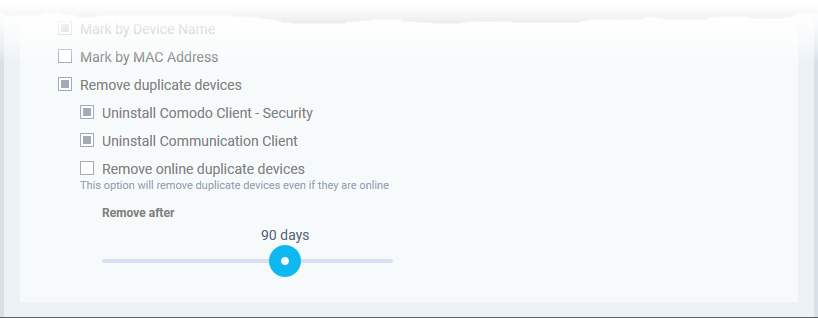
- Uninstall Comodo Client - Security - The CCS app is also uninstalled when the device is removed from EM.
- Uninstall Communication Client - The CC app is also uninstalled when the device is removed from EM.
- Remove online duplicate devices - Forcibly remove a duplicate device even it is online and connected to EM
- Remove after - Specify how many days EM should keep duplicates before removing them. The counter starts 1 day after a device is identified as a duplicate.
Click 'Save' to apply your changes
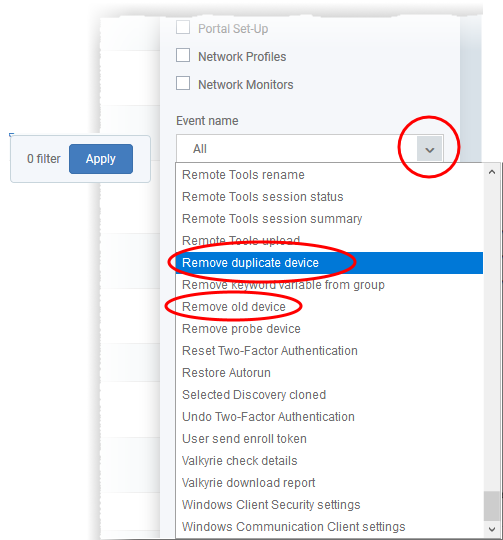
Filter logs or devices to view removed devices
Note - You must have enabled the ‘Mark and Remove’ options to use these filters
Logs:
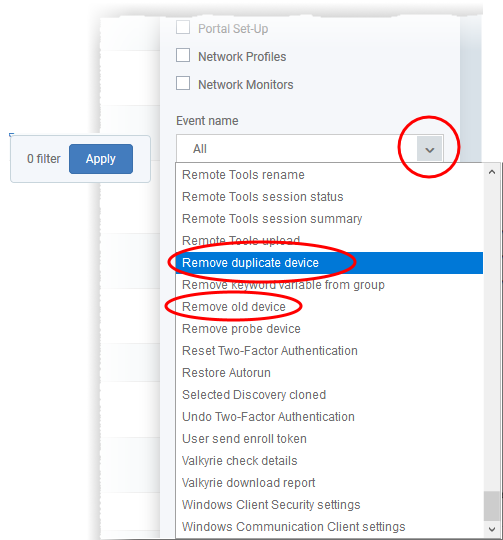
- Click 'Dashboard' > 'Audit Logs'
- Click the funnel icon on the right to open the filter menu
- Click the ‘Event Name’ drop-down
- Select ‘Remove duplicate device’ or ‘Remove old device’ as required:
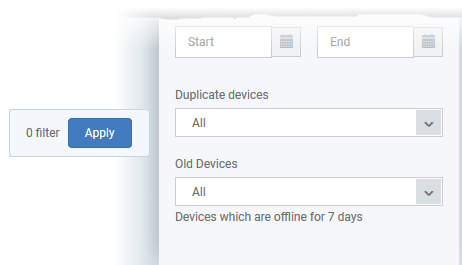
Devices
- Click 'Devices' > 'Device List'
- Click the funnel icon on the right to open the filter menu
- Scroll down to the ‘Duplicate’ and ‘Old’ menus:
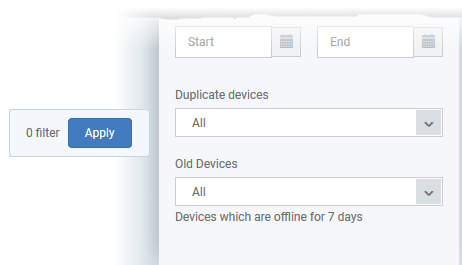
You have the following options for ‘Duplicate devices’:
- All - Shows every device added to Endpoint Manager. In other words, ‘Do not filter for duplicate devices’.
- Primary devices only - A primary device is the most recently-added device among a set of duplicates.This is the only device that is kept after a duplicate removal operation.
- Duplicate devices only - These are duplicate devices which were enrolled earlier than the primary device. These devices will be eventually deleted if you have enabled 'Remove duplicate devices'.
- Primary devices and their duplicates – Shows all duplicate devices.
Click ‘Apply’ to implement your filter.