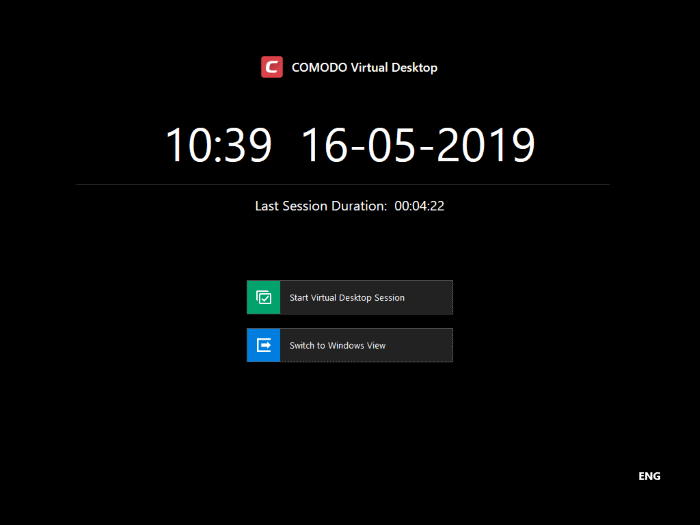
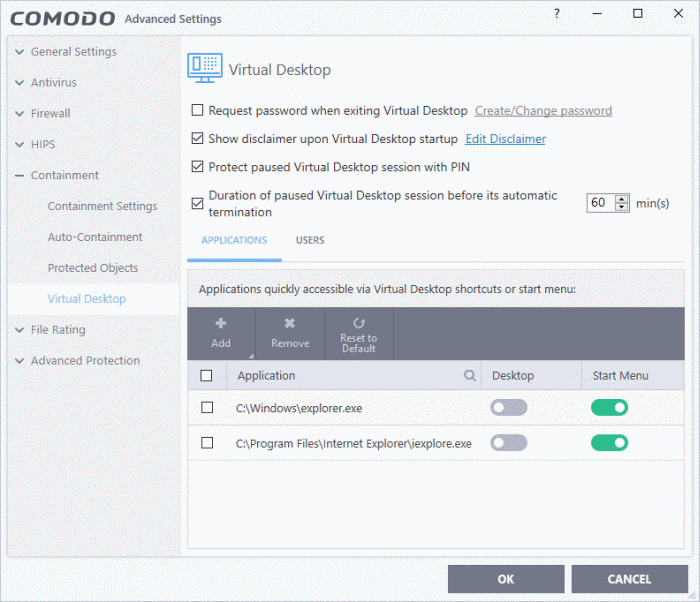
Open CCS on the endpoint > Click ‘Settings’ > ‘Containment’ > ‘Virtual Desktop’
- The virtual desktop is a sandbox environment in which users can run programs and browse the internet without fear those activities will damage the host computer.
- Applications in the virtual desktop are isolated from other processes on the host computer, write to a virtual file system, and cannot access user data. Changes made to files and settings in the virtual desktop do not affect the originals on the host system.
- Because of this, any attacks by internet-based malware cannot reach or compromise the host system. This makes the virtual desktop a highly secure environment for general workflows, and specifically for surfing the internet.
- Any files you wish to keep can be saved in the special folder called 'Shared Space'. This folder is accessible to both the localhost and the virtual desktop.
- The virtual desktop can run any Windows program, so could be used as the default login environment for employees and guests. You can set a password to lock users into the virtual desktop. Users will need to enter the password before they can exit the desktop.
- In most cases, admins should configure the behavior of the virtual desktop in an Endpoint Manager profile.
- You can also locally configure them locally in the CCS interface. Please note – the local settings will be ignored unless 'Allow user to override Virtual Desktop settings' is enabled in the device profile.
Configure virtual desktop settings in CCS
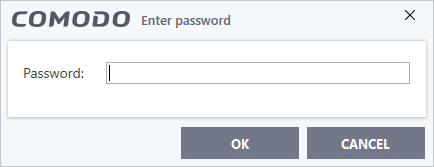
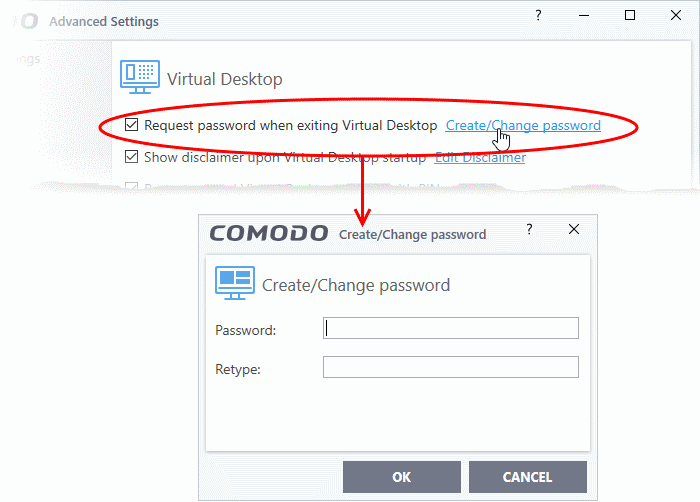
Request password when exiting Virtual Desktop - Create an 'exit' password for the virtual desktop. Users need to enter the password in order to close the virtual desktop.
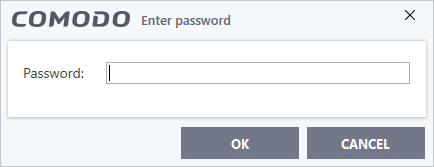
This prevents users from closing the virtual desktop and accessing the host, potentially exposing the computer to danger.
- Enable 'Request password when exiting Virtual Desktop'
- Click the 'Create/Change password' link:
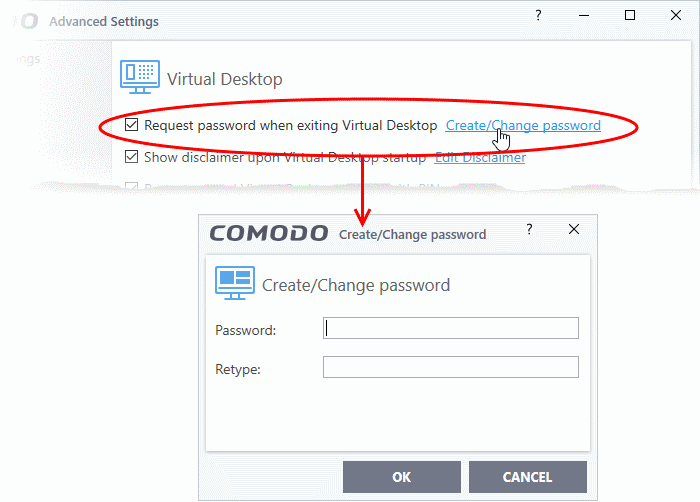
- Type a password that cannot easily be guessed.
- It should be 8-16 characters long and contain a mix of upper case letters, lower case letters, numbers, and special characters.
- Confirm the password then click 'OK'.
- The validity of the password is 90 days. You need to reset the password when it expires.
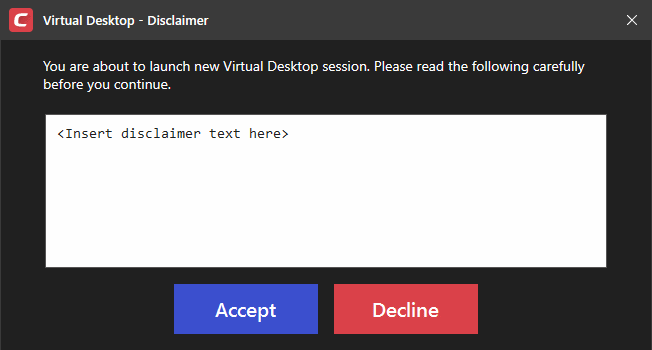
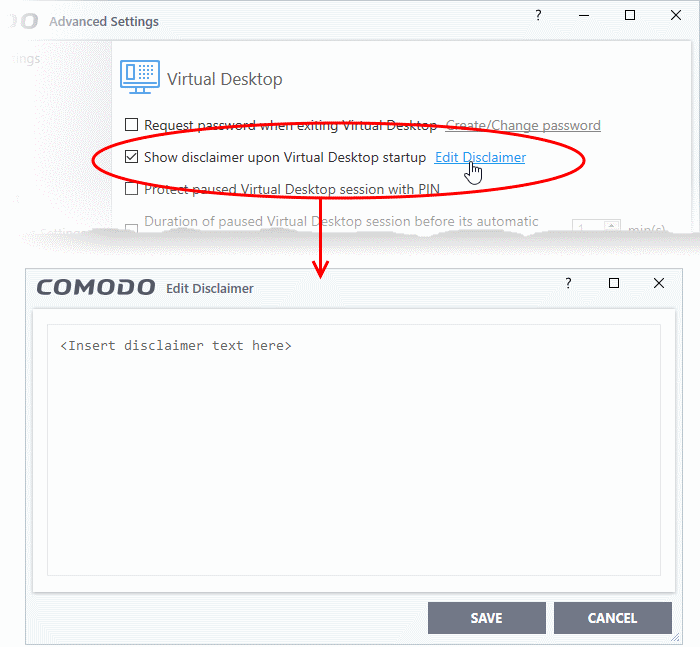
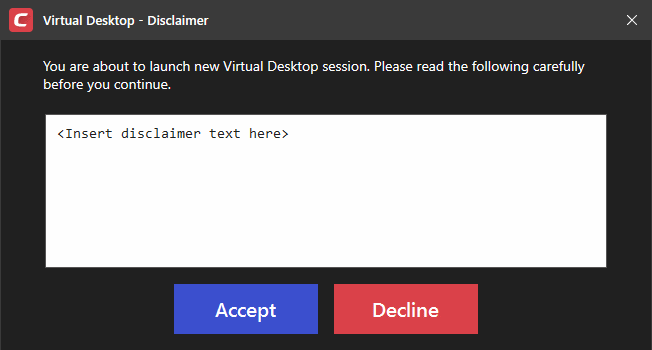
Show disclaimer upon Virtual Desktop startup - Create a legal disclaimer which is shown when the virtual desktop starts. Users must accept the disclaimer before they can access the virtual desktop.
- Enable 'Show disclaimer upon Virtual Desktop startup'
- Click the 'Edit Disclaimer' link
- Type the disclaimer message in the box
- Click 'Save':
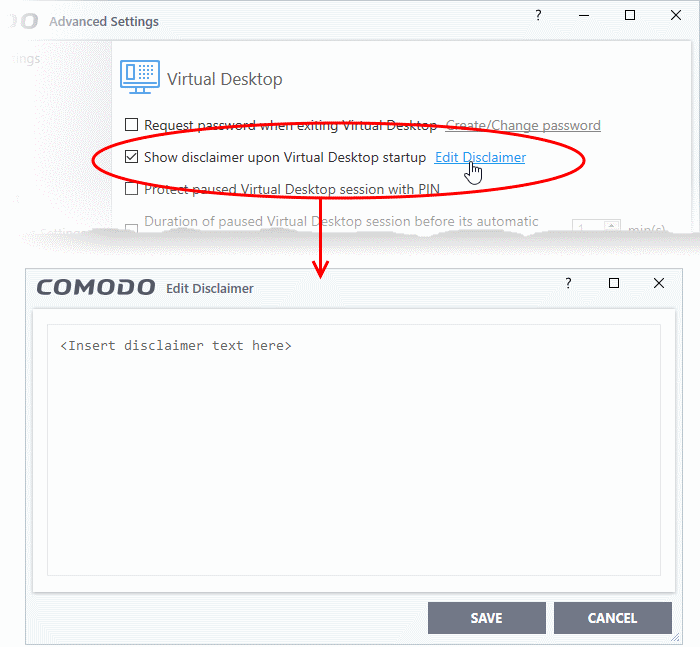
- The message is shown when the virtual desktop starts.
- Users should read the disclaimer and click 'Accept':
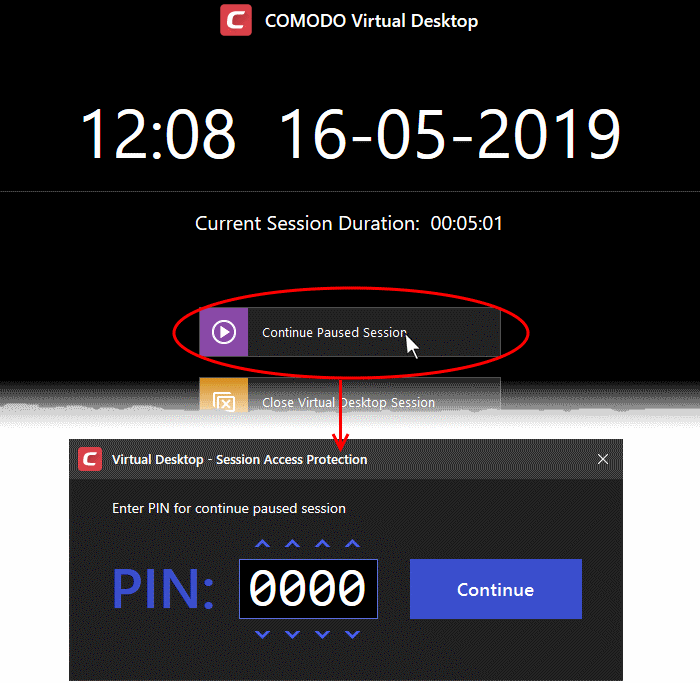
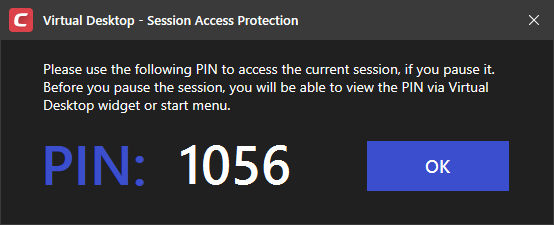
Protect paused Virtual Desktop session with a PIN - Generates a session-specific code at virtual desktop startup. This code is required to unlock a virtual desktop from a paused state.
This creates a second layer of authentication on top of the regular Windows credentials for any sensitive data in the virtual desktop. The feature is also useful on shared computers as it prevents other users from accessing the session.
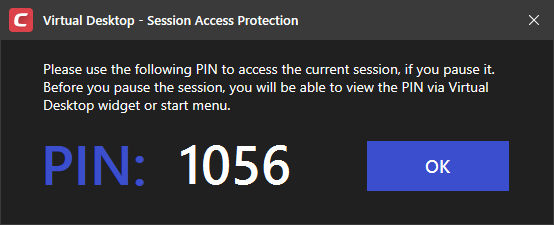
- Users need to make a note of the PIN. If they pause the virtual desktop session they will need to enter the PIN to resume.
- Users can view the PIN number at any time by clicking the button
 at the bottom-right of the virtual desktop.
at the bottom-right of the virtual desktop.
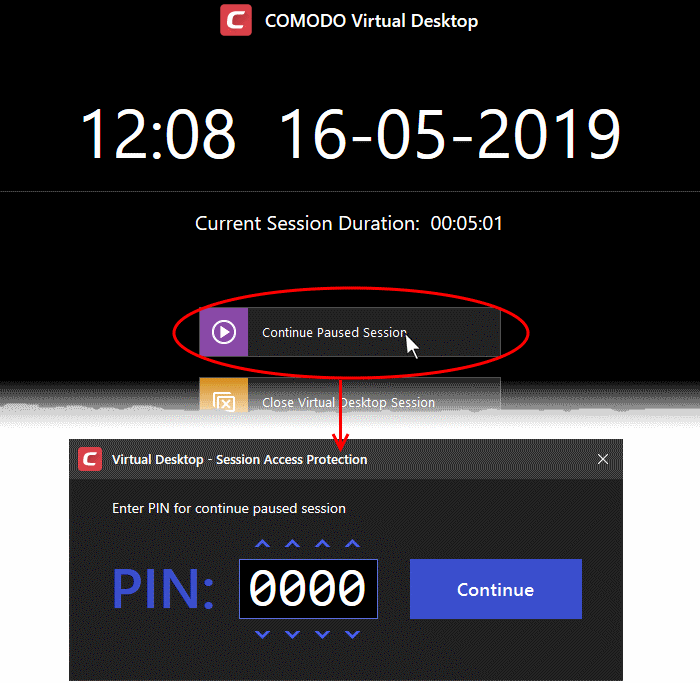
Duration of paused Virtual Desktop session before its automatic termination - Set the maximum length of time a virtual desktop session can be left in a paused state. The session gets automatically terminated when this period elapses.
Applications - Add apps to the virtual desktop
- Applications that you add to this area will appear inside the virtual desktop for users.
- This is just to present users with a useful set of popular applications. Users can start any other applications they require by simply browsing to them.
- The virtual desktop already has shortcuts for Windows Explorer and all currently installed browsers.
Add applications to the virtual desktop
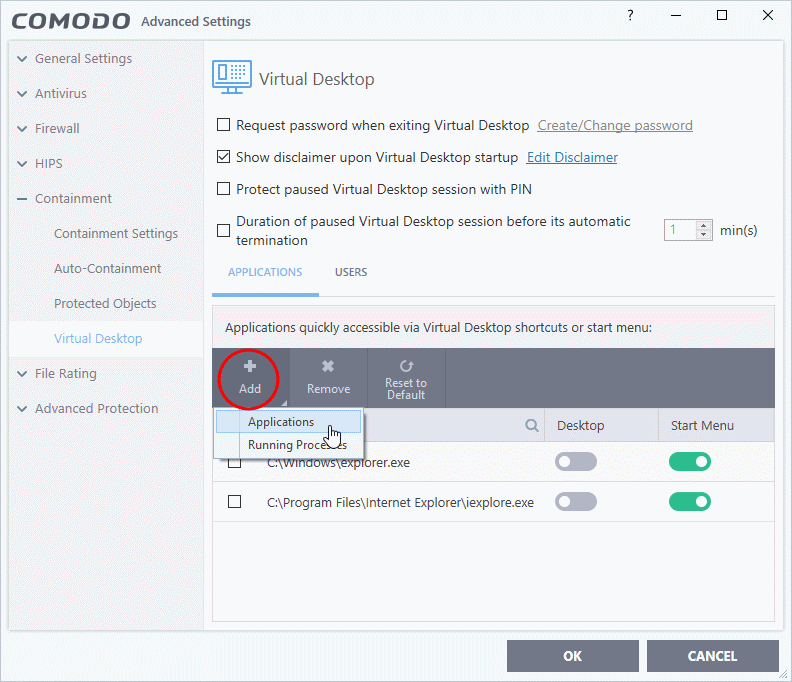
- Click 'Add' under 'Applications' in the 'Virtual Desktop' settings interface
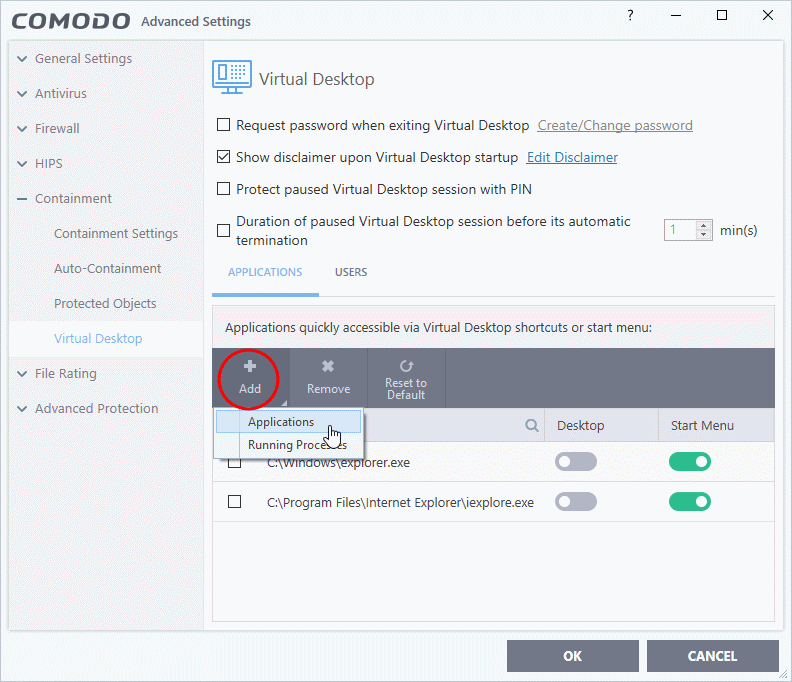
There are two ways to add applications:
- Application - Browse to the executable of the application and select 'Open'.
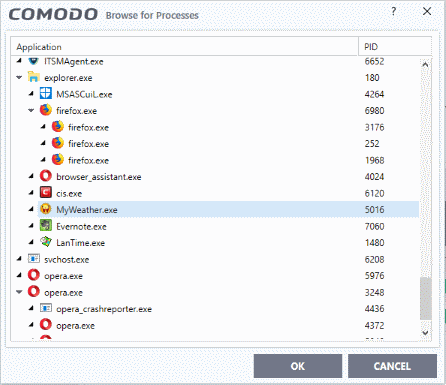
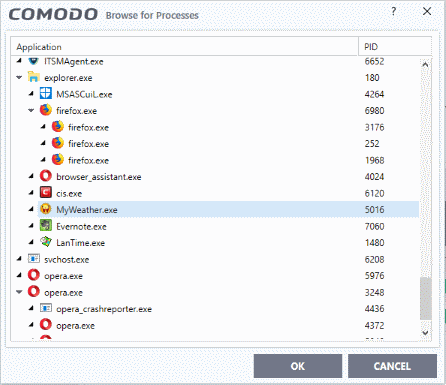
- Running Processes - Select the app from the list of currently running processes. The parent application of the process is added to the virtual desktop.
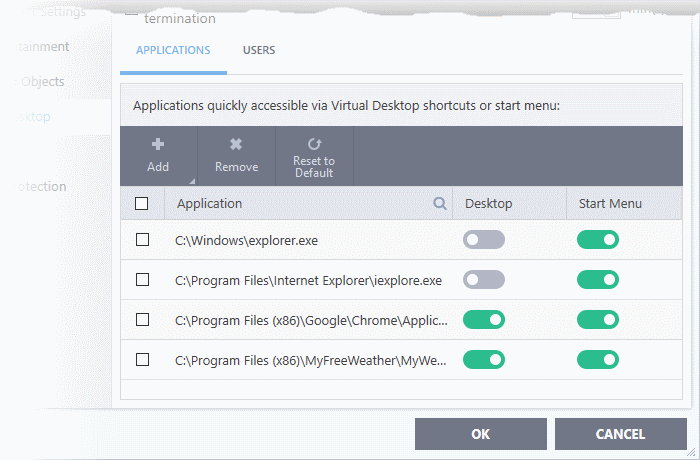
The applications will be added to the list:
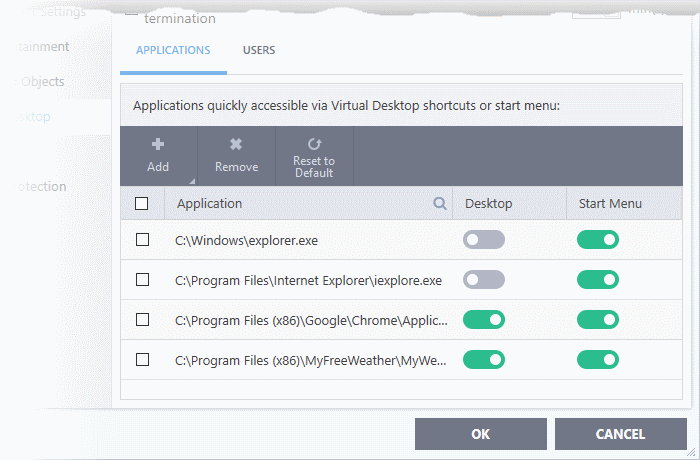
- The 'Desktop' and 'Start Menu' switches let you to enable each type of shortcut per application.
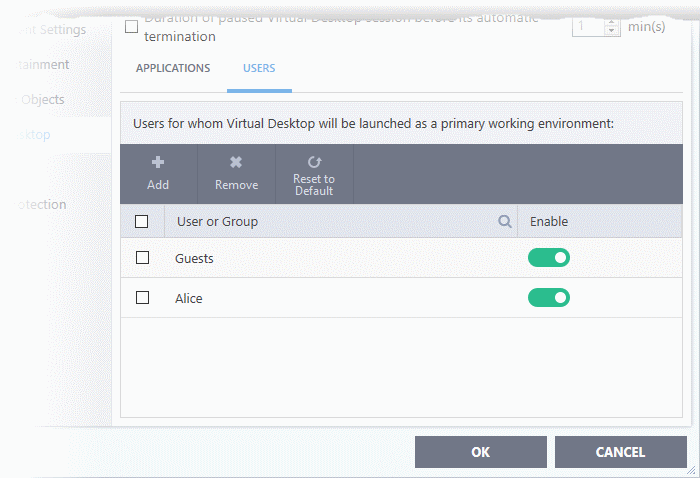
Add users who should log straight into the virtual desktop
- You can configure the virtual desktop to start automatically whenever certain users login to the system.
- This means the virtual desktop becomes the default operating environment for those users.
- You can combine this with the ‘request password...’ option to effectively lock users into the virtual desktop.
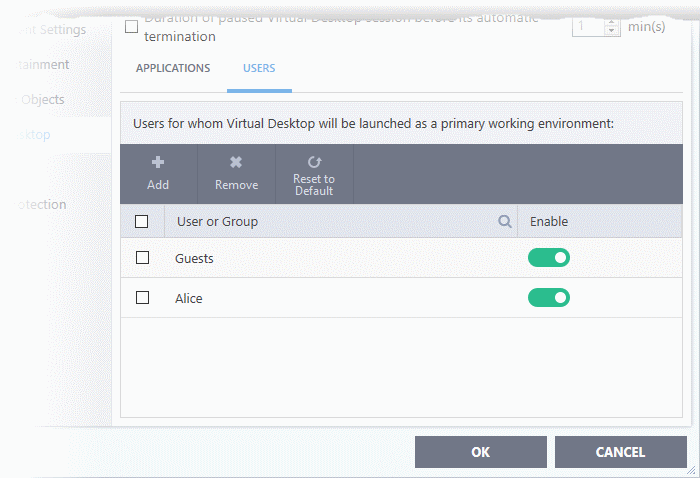
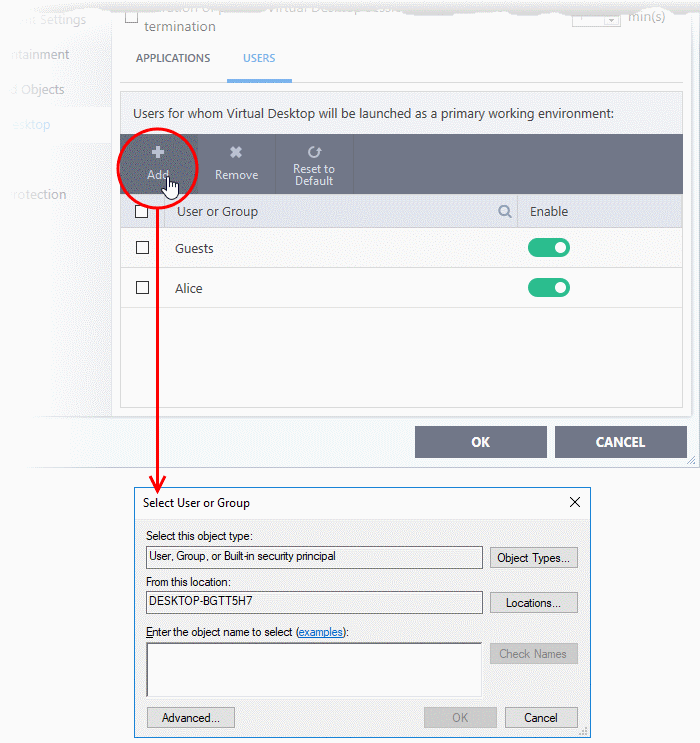
- Click the 'Users' tab
- Click 'Add'
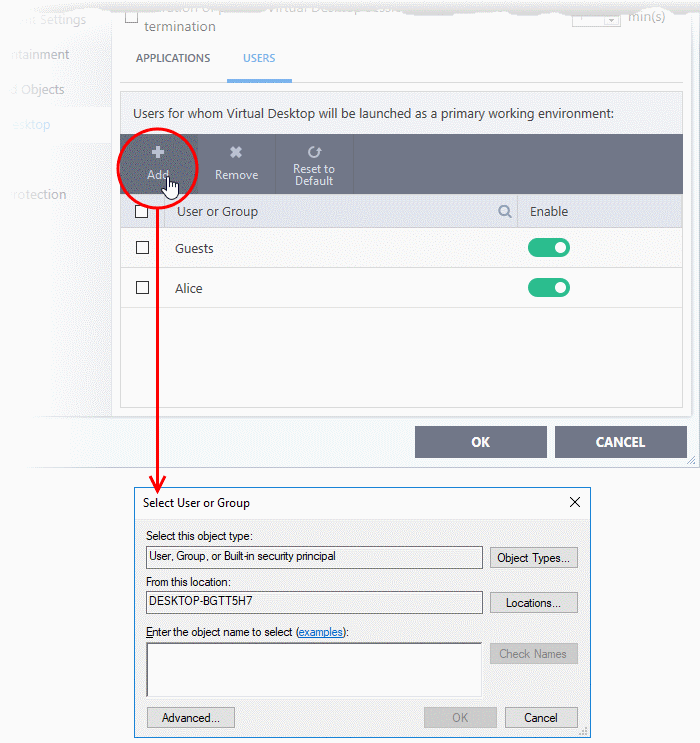
- Select the users or groups to whom you want the rule to apply.
- Type user or group names in the format <domain name>\<user/group name>, or <user/group name>@<domain name>.
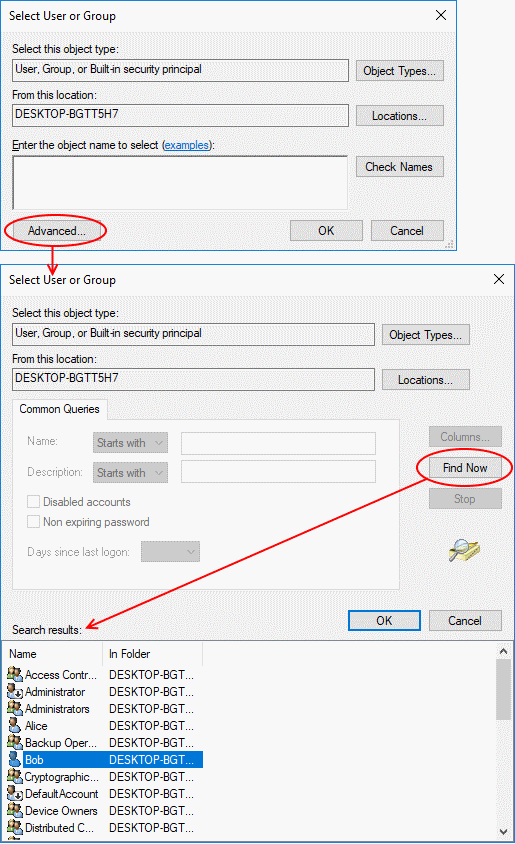
- Alternatively, click 'Advanced' then 'Find Now' to locate specific users/ groups.
- Click 'OK' to confirm.
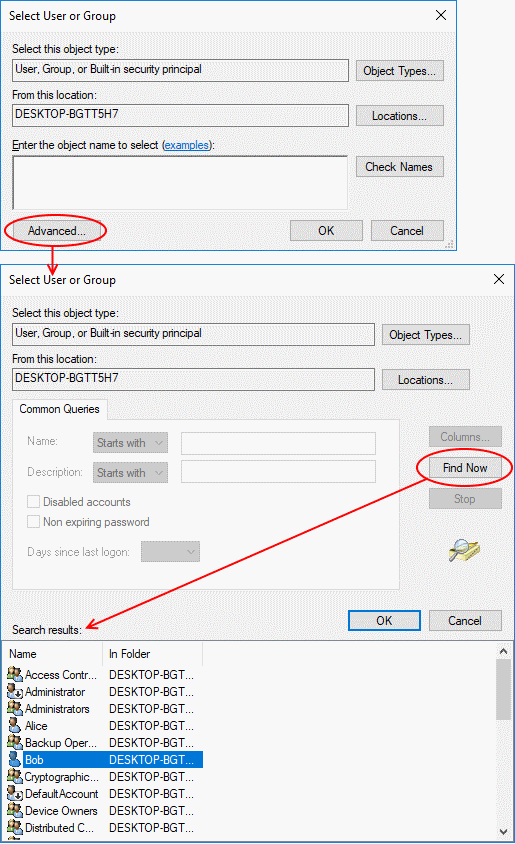
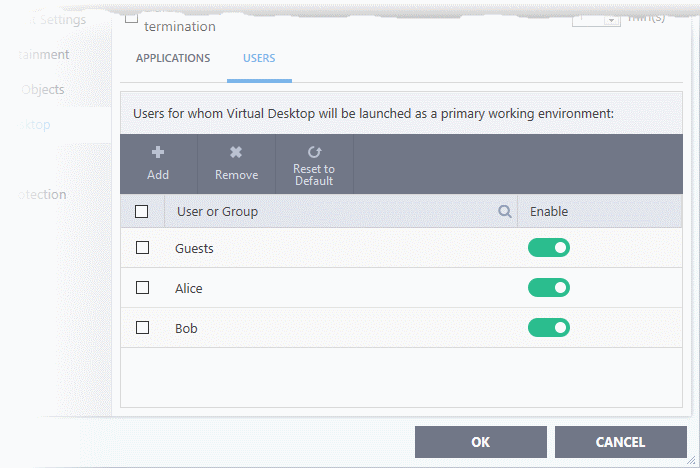
The user/user group is added to the list.
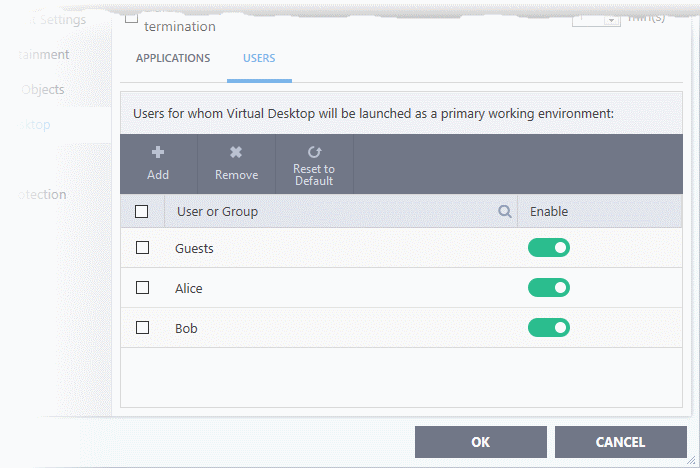
- Repeat the process to add more users.
- Click 'OK' to save your settings
- Click OK in the 'Advanced Settings' dialog for your changes to take effect
The virtual desktop will load automatically when the user signs-in to the computer.
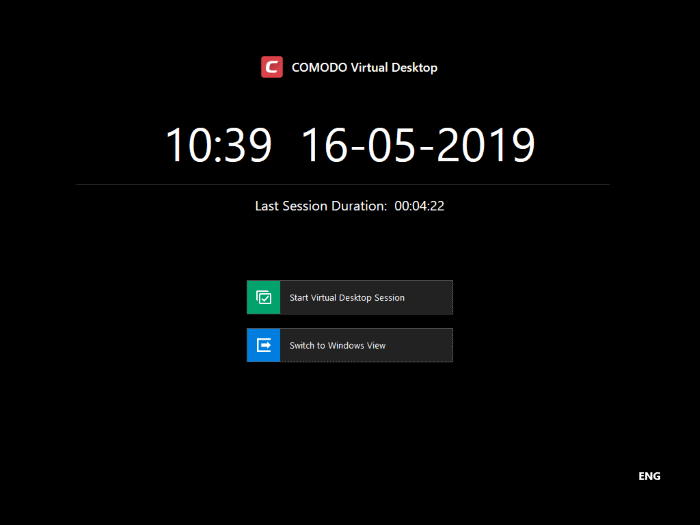
- The user can decide whether to continue with the virtual desktop or switch to the host OS.
- You must enable password protection if you want to stop users switching to the host.

 at the bottom-right of the virtual desktop.
at the bottom-right of the virtual desktop.