- A security profile governs a device's network access rights, security policy, antivirus scan schedule, and other system settings.
- This wiki explains some import/export options that can help simplify your work with profiles:
Import the CCS configuration from an endpoint as a profile
- This method involves exporting the local configuration of CCS on an endpoint, then importing it back to EM as a profile.
- The configuration you export from the endpoint is its currently active config. This means it also includes any changes made at the local interface.
- This is method is useful if you have an ‘ideal configuration’ running on one machine that you want to use on other machines.
There are two steps to this process:
Step 1 - Export the configuration from the selected device
- Login to ITarian
- Click 'Applications' > 'Endpoint Manager'
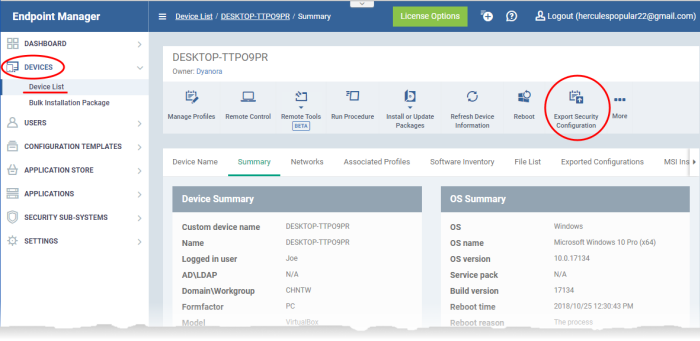
- Click 'Devices' > 'Device List' > 'Device Management'
- Click on the Windows device whose configuration you want to import
- The 'Device Details' interface opens.
- Click 'Export Security Configuration'
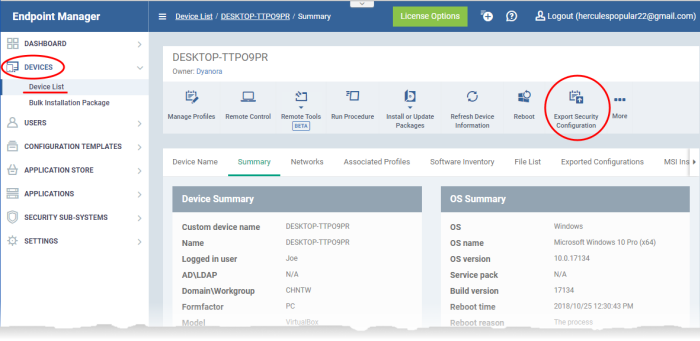
- The configuration will be exported as a .xml file and saved in Endpoint Manager.
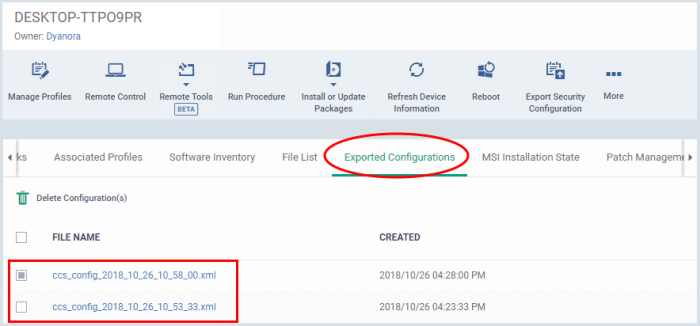
- Click the ‘Exported Configurations’ tab to see a list of all saved .xmls:
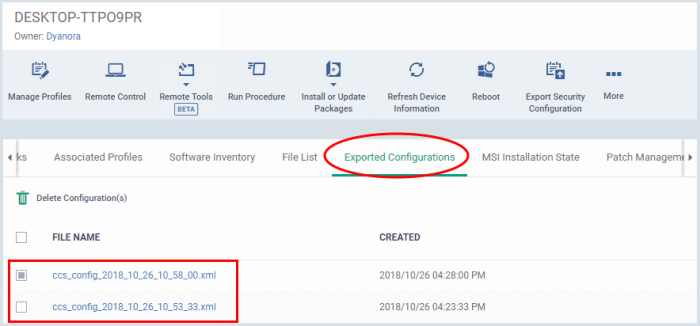
- Click the name of the file that you want to import as a profile and save it in a safe location.
Step 2 - Import the .xml file as a profile
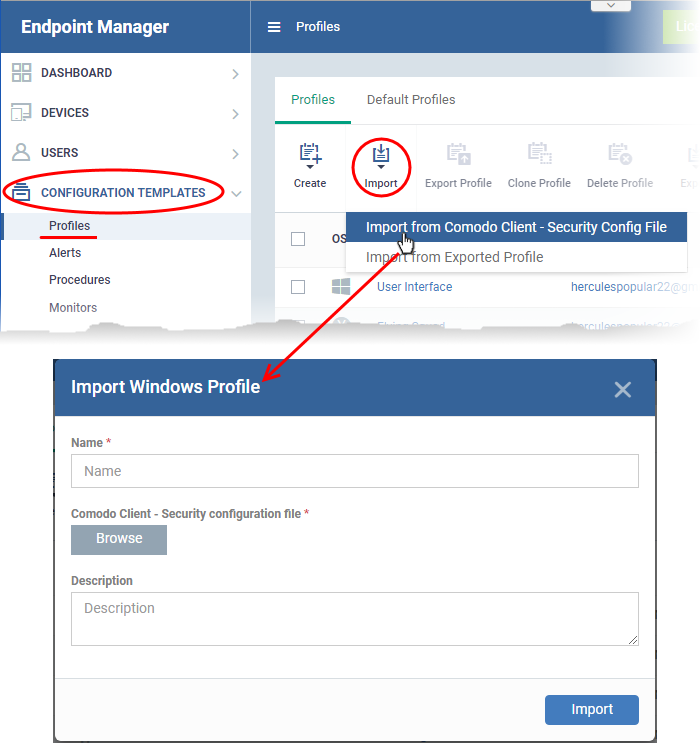
- Click 'Configuration Templates' > 'Profiles'
- Click 'Import' > 'Import from 'Comodo Client Security Config file':
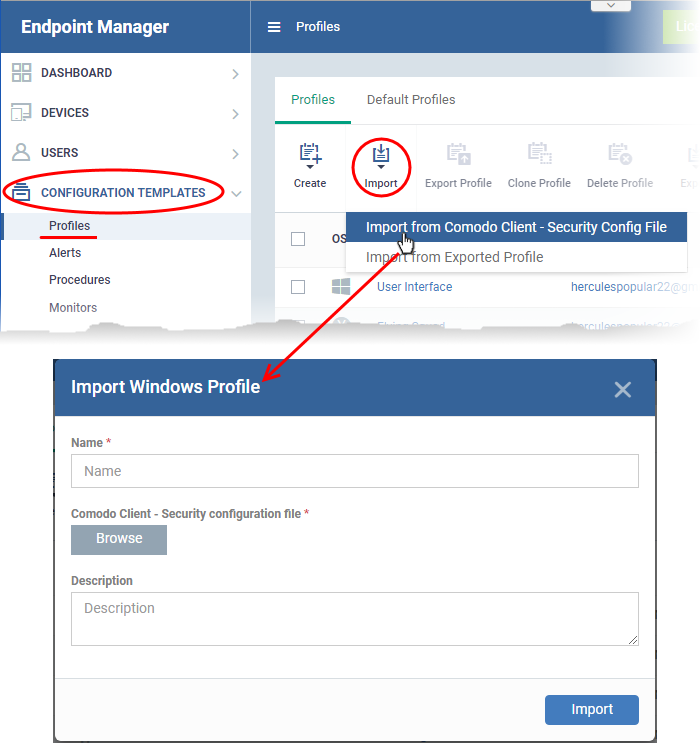
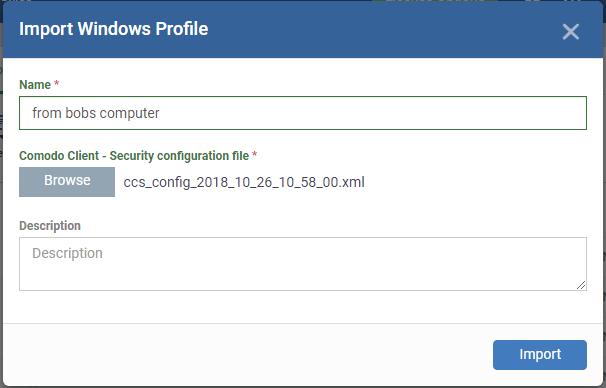
- Enter a name and description for the profile.
- Click 'Browse', navigate to the .xml file then click 'Open'.
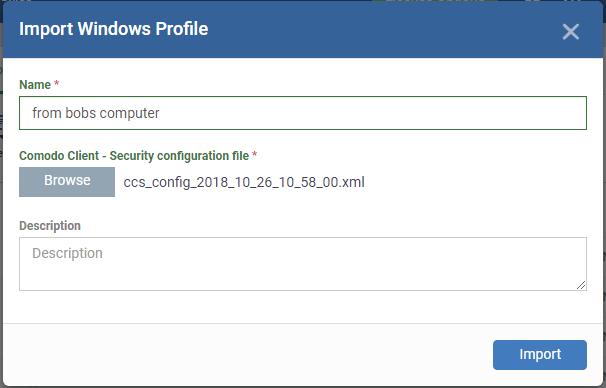
- Click the 'Import' button.
- You can now deploy the profile as required to Windows devices and device groups.
Export and Import profiles from EM
- You can export a profile to .cfg file then re-import it as a profile at a later time.
- Exporting a profile is a good way to create a backup prior to making changes to a live profile. You could export the profile, make the changes, and restore to the backup if the changes cause issues.
- Exporting is also useful if you want to import the profile into a different Endpoint Manager account.
- Also consider – As an alternative, the ‘Clone Profile’ feature lets you duplicate an existing profile. You can then keep the clone as an exact copy of the original, or make changes to it as required.
- Note - Windows profiles only. 'Monitor Settings' and 'Procedure Settings' are excluded from exported profiles. You will need to reconfigure these sections before deploying if they are required in your new profile.
Export a profile
- Login to ITarian
- Click 'Applications' > 'Endpoint Manager'
- Click 'Configuration Templates' > 'Profiles'
- Select the 'Profiles' tab.
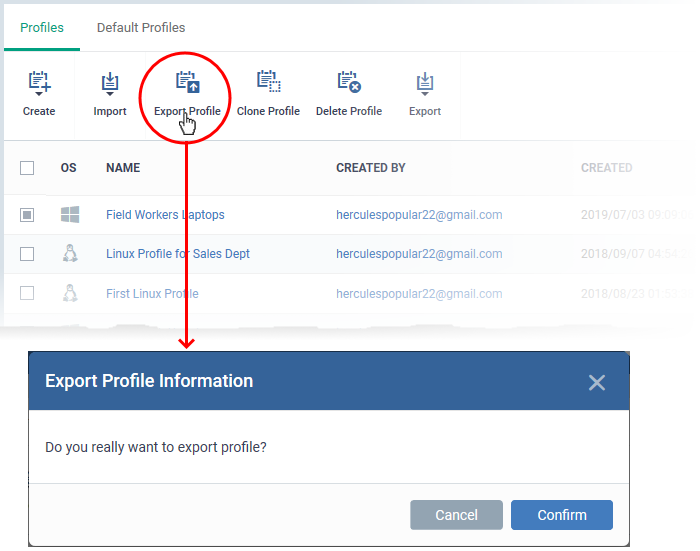
- Select the profile you want to export and click the 'Export profile' button:
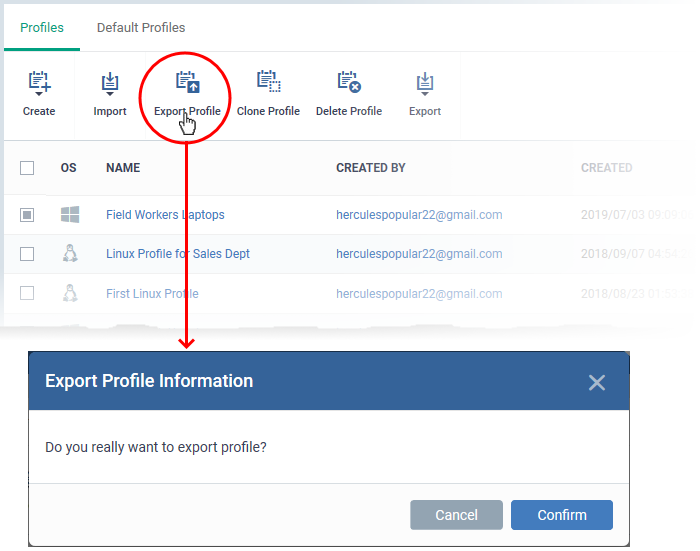
- Click 'Confirm' and save the configuration file in a safe location
Import a saved configuration as a profile
- Login to ITarian
- Click 'Applications' > 'Endpoint Manager'
- Click 'Configuration Templates' > 'Profiles'
- Select the 'Profiles' tab.
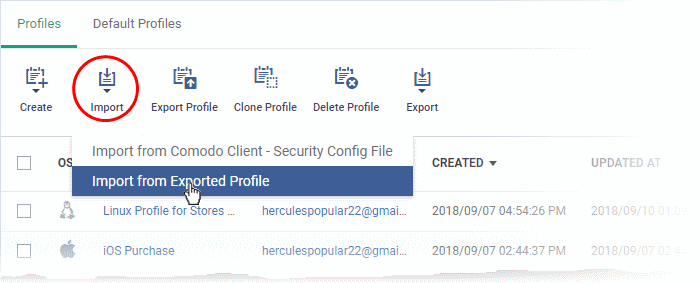
- Click 'Import' > 'Import from Exported Profile'
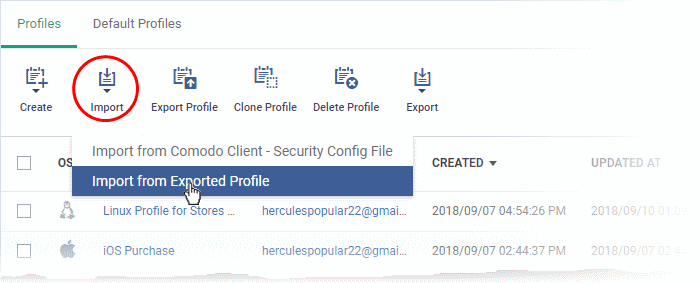
- Navigate to the .cfg file and click 'Open'.
- The profile will be listed in the interface with the prefix [Imported].
- You can edit the imported profile as required.