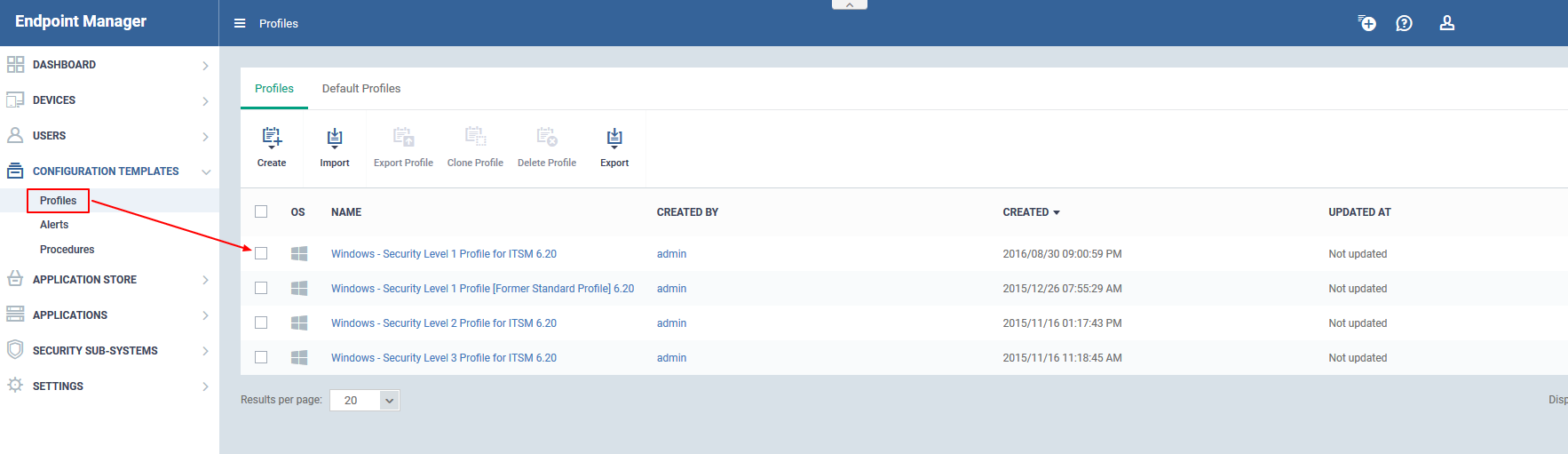
Endpoint Manager new profiles are optimized for security and usability. The profiles are based on three levels of security as follows:
-
‘Windows - Security Level 1 Profile’ (replaces 'Optimum Windows Profile’)
-
‘Windows - Security Level 1 Profile [Former Standard Profile]’ (replaces ‘Standard Windows’ profile)
-
‘Windows - Security Level 2 Profile' (replaces ‘Hardened Windows Profile’)
-
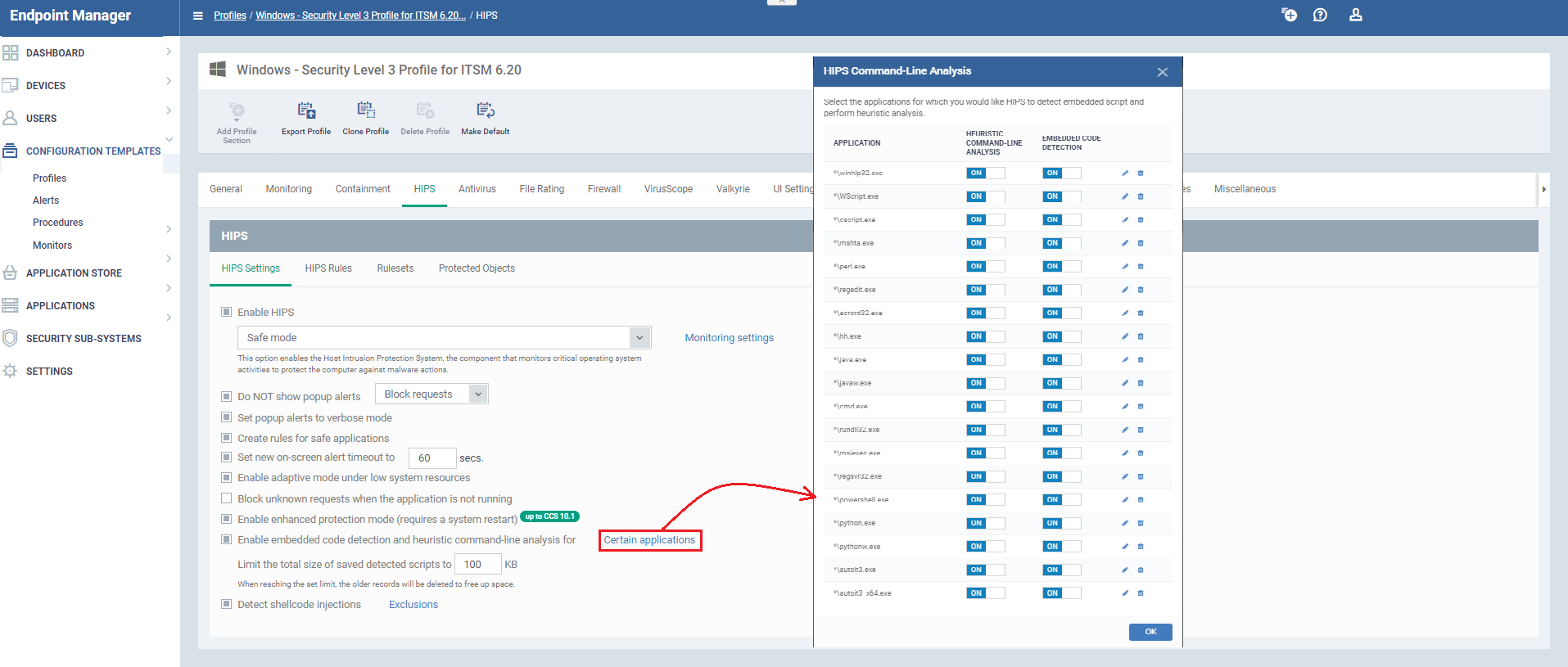
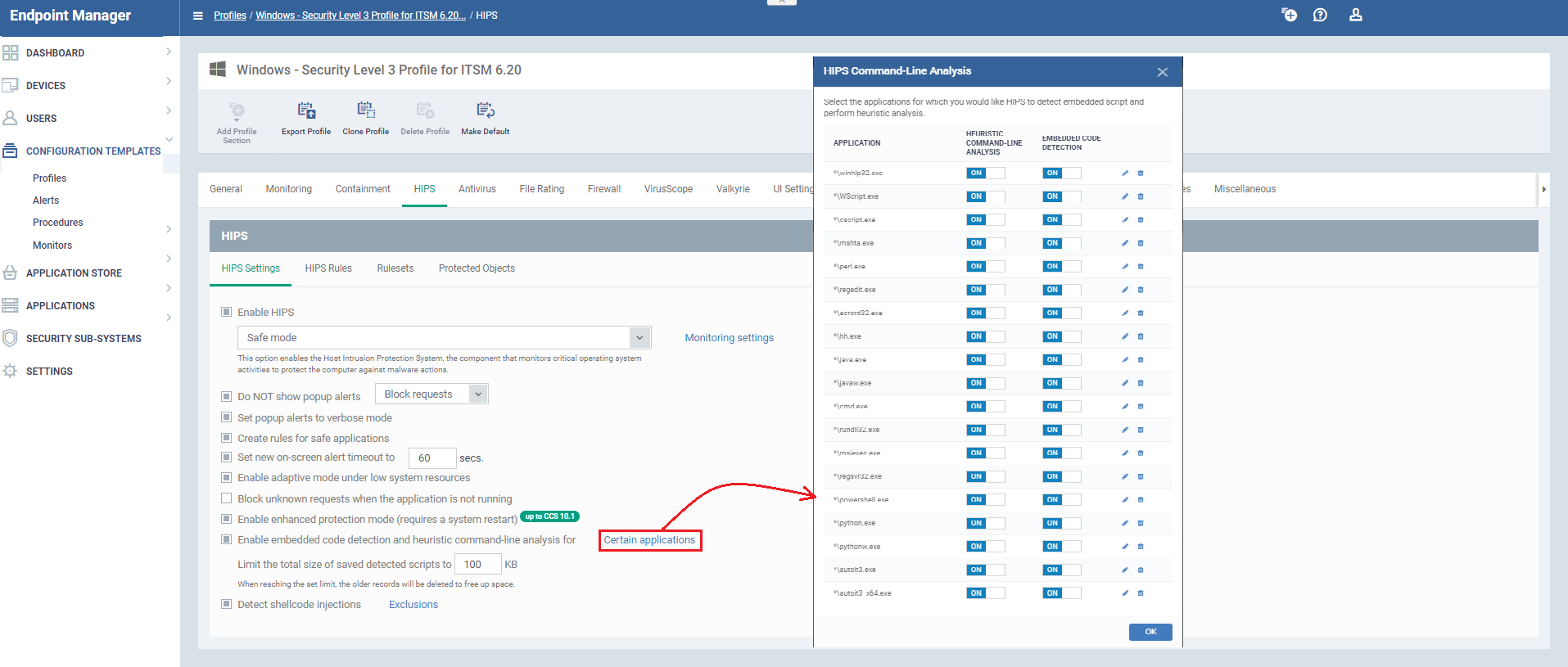
‘Windows - Security Level 3 Profile’ (new profile - max. security)
Step [1] : To view the profiles go to "Endpoint Manager"→ "CONFIGURATION TEMPLATES"→ "Profiles".
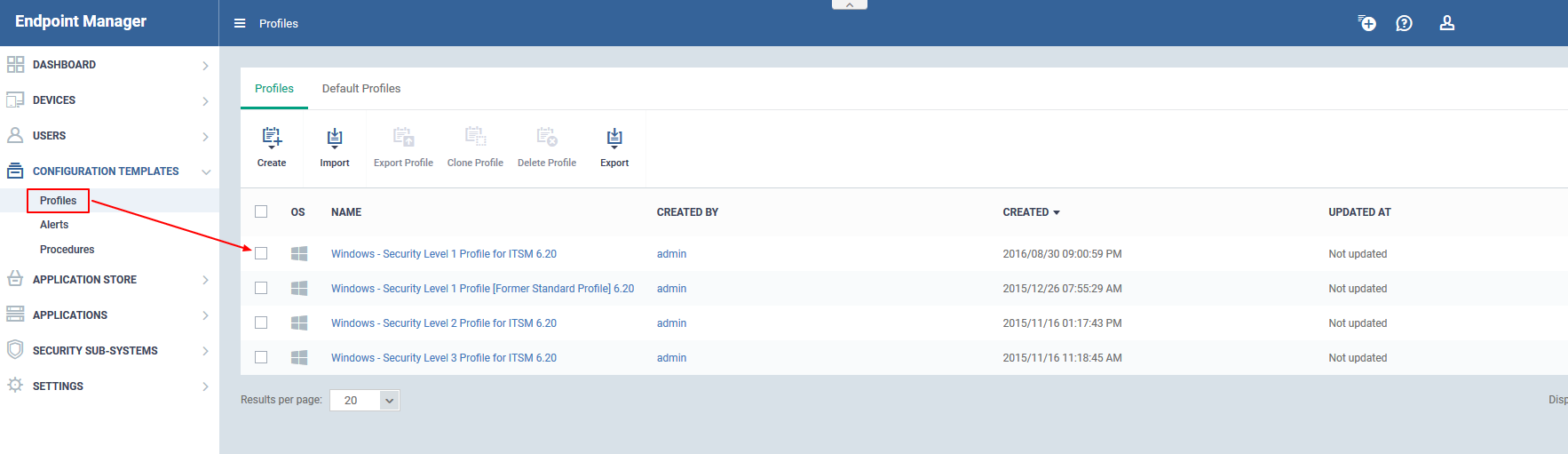
Windows - Security Level 1
Windows – Security Level 2
Windows – Security Level 3
Windows – Security Level 1 [Former Standard Profile]