- A file’s trust rating determines how Comodo Client Security (CCS) handles the file.
- These are the possible file ratings:
- Trusted - The file is safe and is allowed to run normally on the endpoint
- Malicious - The file is malware and is quarantined or deleted on the endpoint.
- Unrecognized - No trust rating is available for the file. Unrecognized files are automatically run in the container because there is the possibility they are malicious. Contained applications write to a virtual file system and registry, and cannot access other processes or user data. You have the option to auto-upload these files to Valkyrie for behavior testing. The tests will identify whether the file is trustworthy or malicious.
- Going one step further, a file can be rated by three sources:
- FLS rating - This is the official Comodo rating of the file. CCS gets this rating from our file-lookup server when it runs a virus scan on the file.
- Admin rating - Admins can use Endpoint Manager to apply their own rating to a file.
- Local rating - End-users (or admins) can set a file’s rating in the CCS interface.
Ratings are prioritized as follows:
1) Admin rating
2) Local rating
3) Comodo rating
There are two ways admins can set a trust rating in Endpoint Manager:
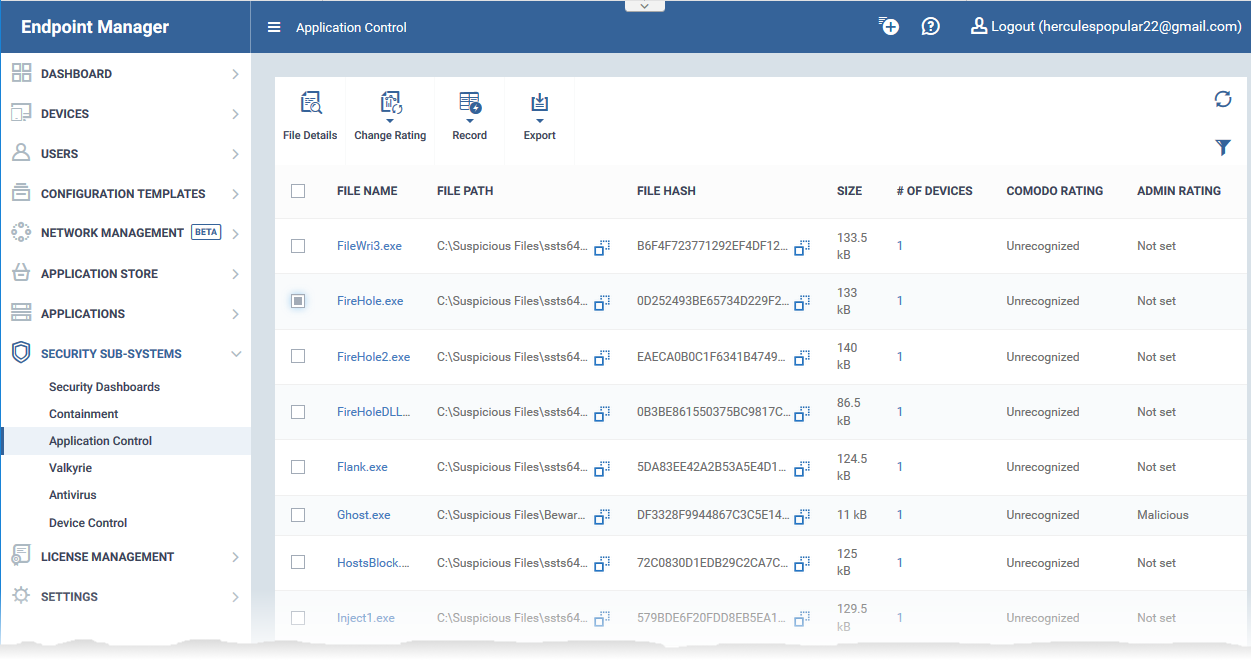
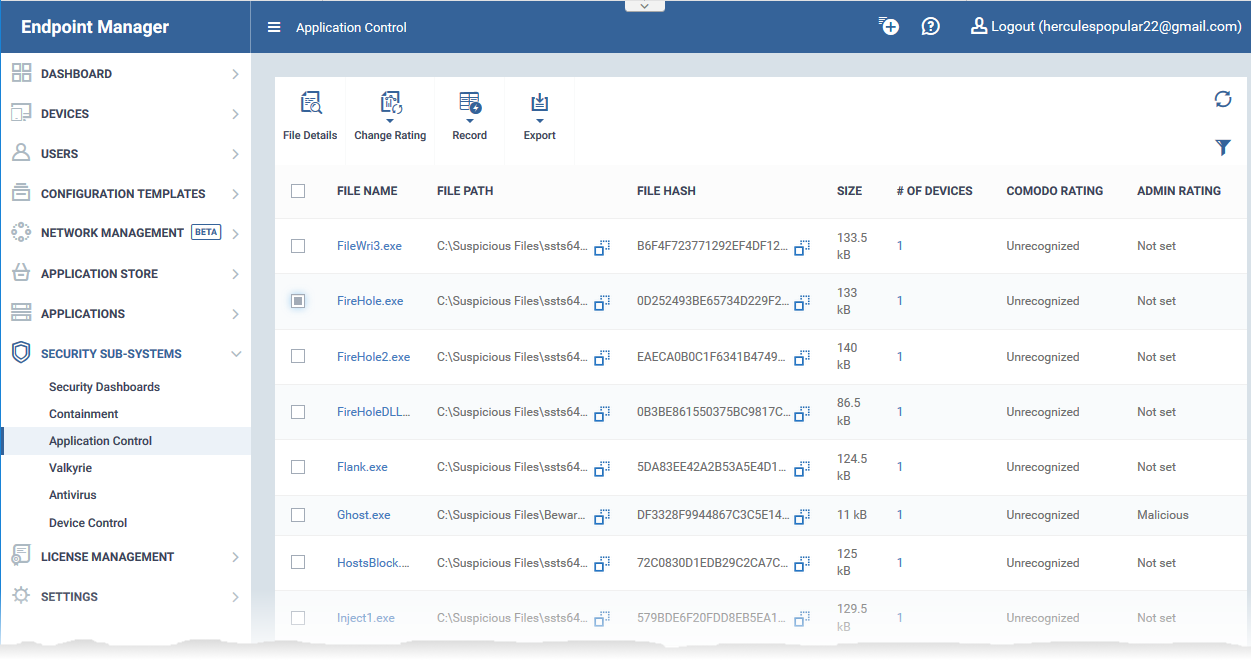
Application Control interface
- Login to ITarian
- Click 'Applications' > 'Endpoint Manager'
- Click 'Security Sub-Systems' > 'Application Control'
The interface shows a list of all files discovered from all managed endpoints with their trust ratings:
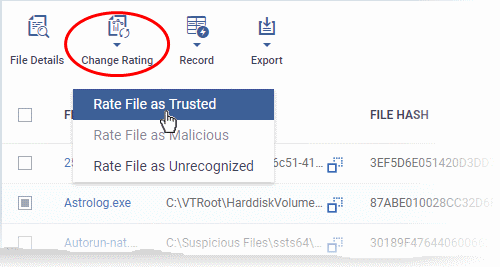
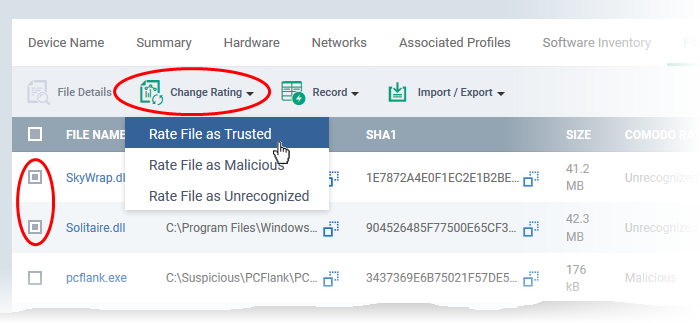
- Select the file for which you want to set a rating
- Tip – Click the funnel icon at the top right and use the filters to search for a specific item
- Click 'Change Rating'.
- Select the new rating from the options: