We have a brand new feature for Containment From now on, you will be able to view statistics of containment components for each process. By this way, you can analyze how containment protects you with statistics on Registry, COM, IMA etc. both in containment and real-time.
Note: This new feature under containment task is available only for Comodo client security version-10.2.0.6537 and above
To install Comodo Client Security(CCS) in endpoint, please refer this wiki topic: https://wiki.itarian.com/frontend/web/topic/how-to-install-comodo-client-security-on-windows-linux-and-mac-devices
To Update Comodo Client Security(CCS) in endpoint, please refer this wiki topic:https://wiki.itarian.com/frontend/web/topic/how-to-manually-run-updates-on-endpoints
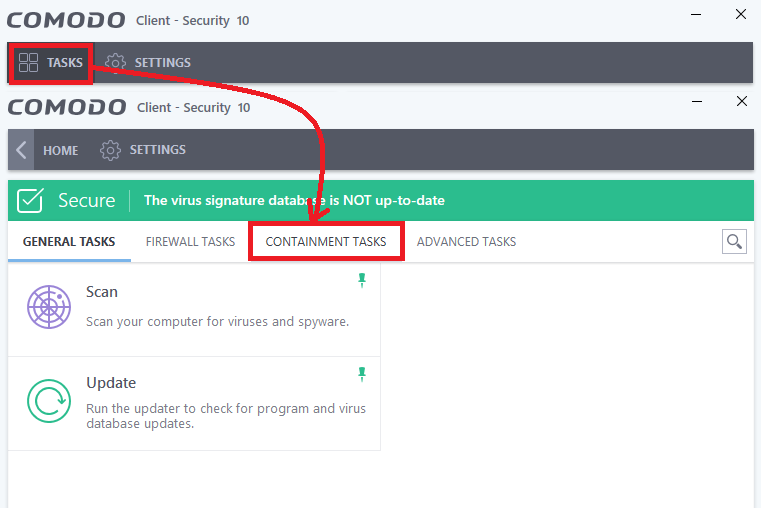
Step 1: Open Comodo Client security application from the endpoint in which it is installed. Select Tasks-> Containment Task
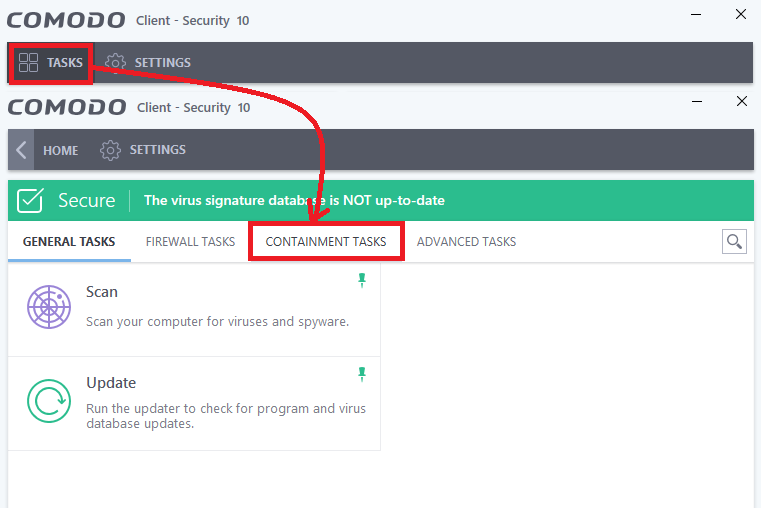
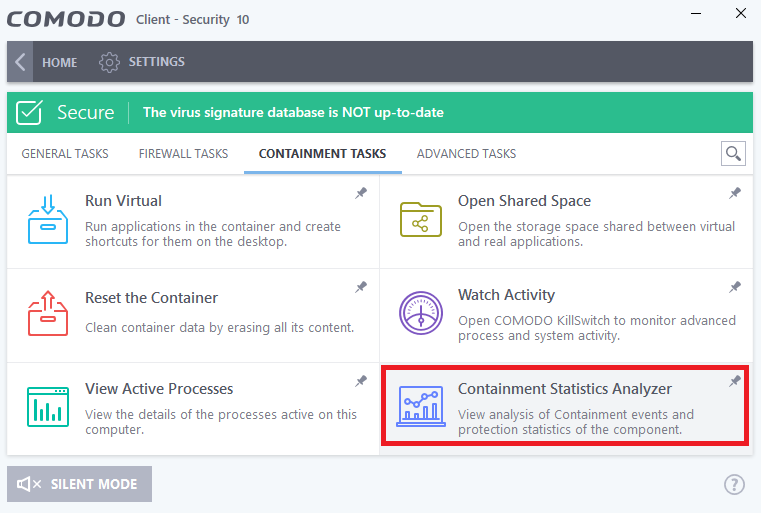
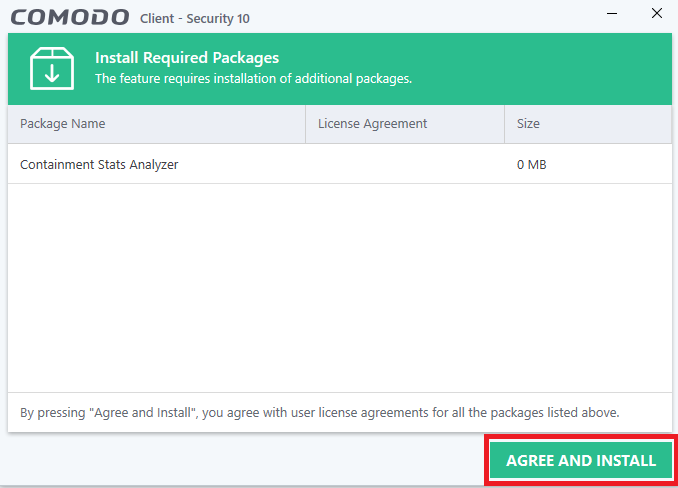
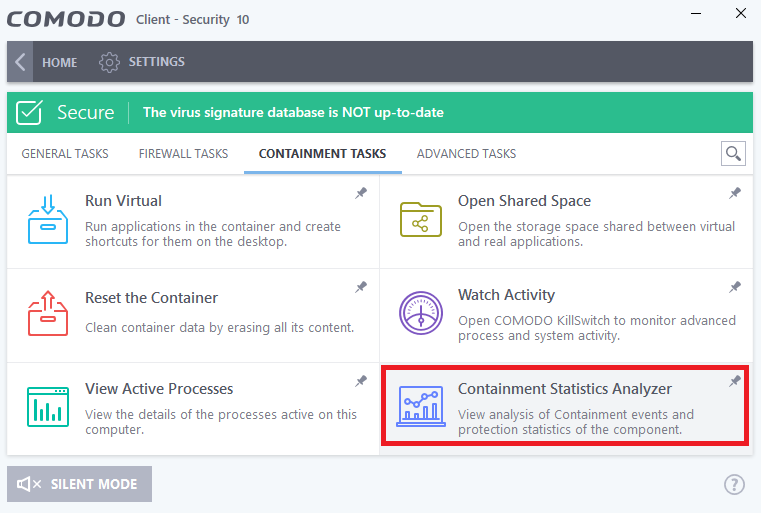
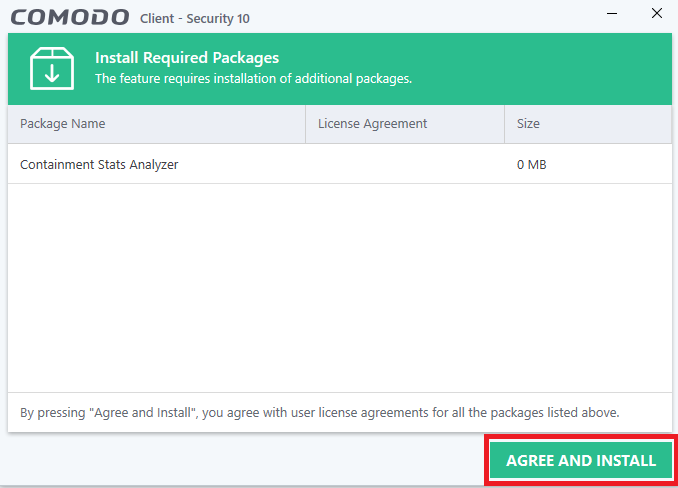
Step 2: Select the new feature Containment Statistics Analyser then a new window will be opened for installing the feature. In the new window click “Agree and install”.
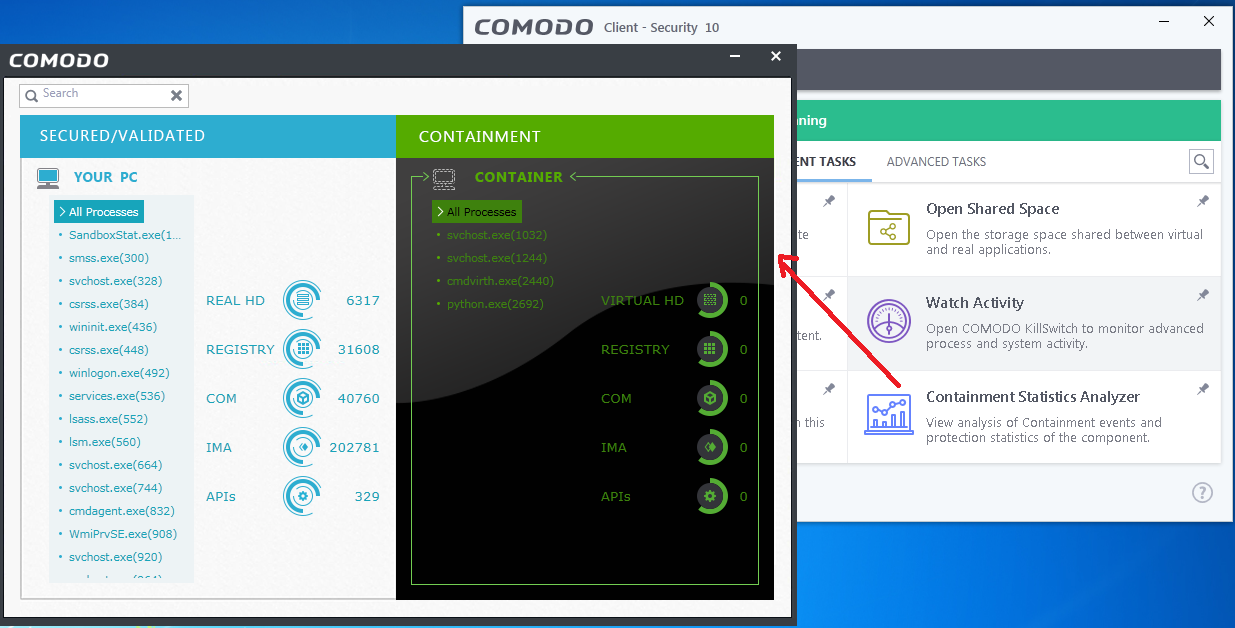
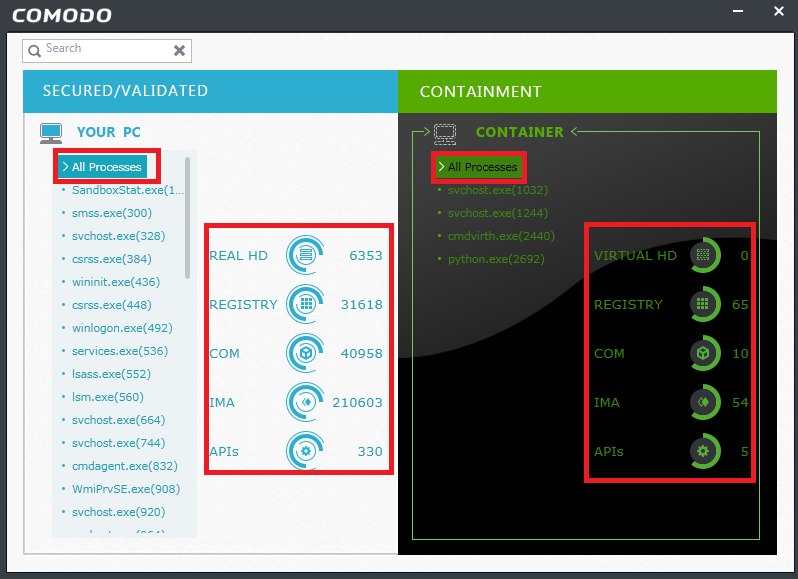
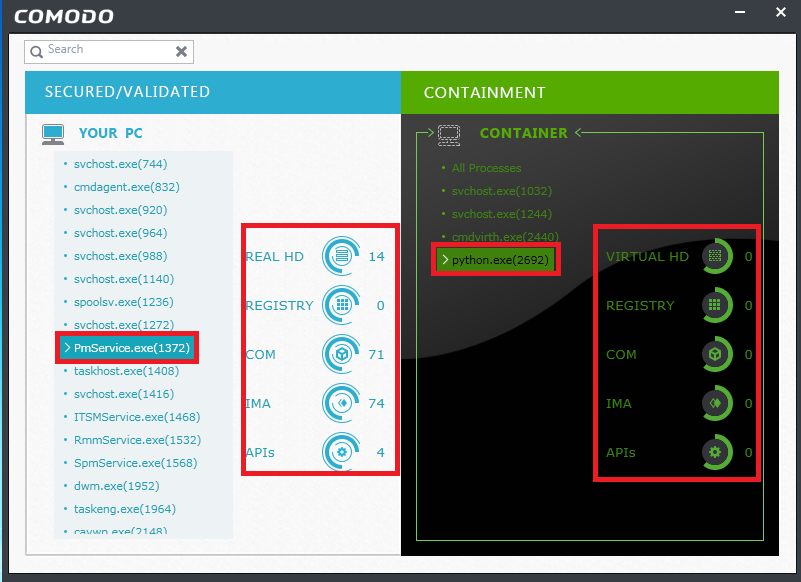
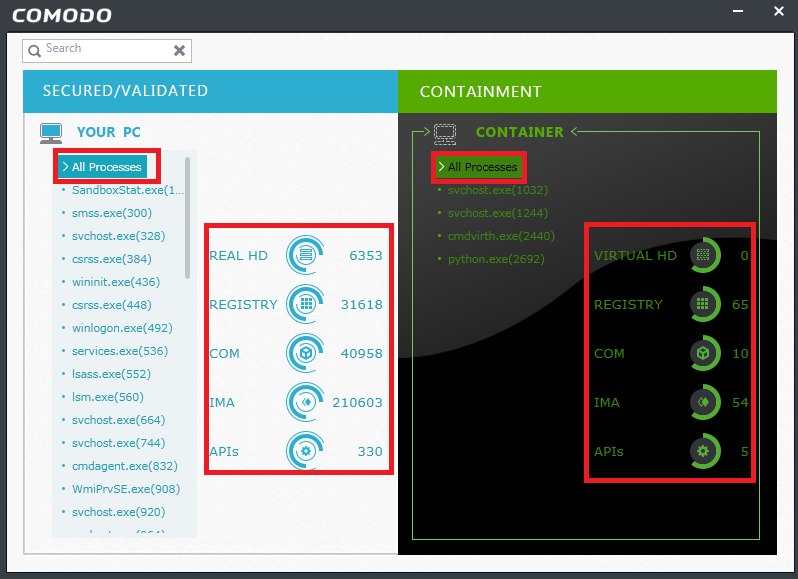
Step 3: The containment analysis windows consist of two major sections Secured/validated and Containment.
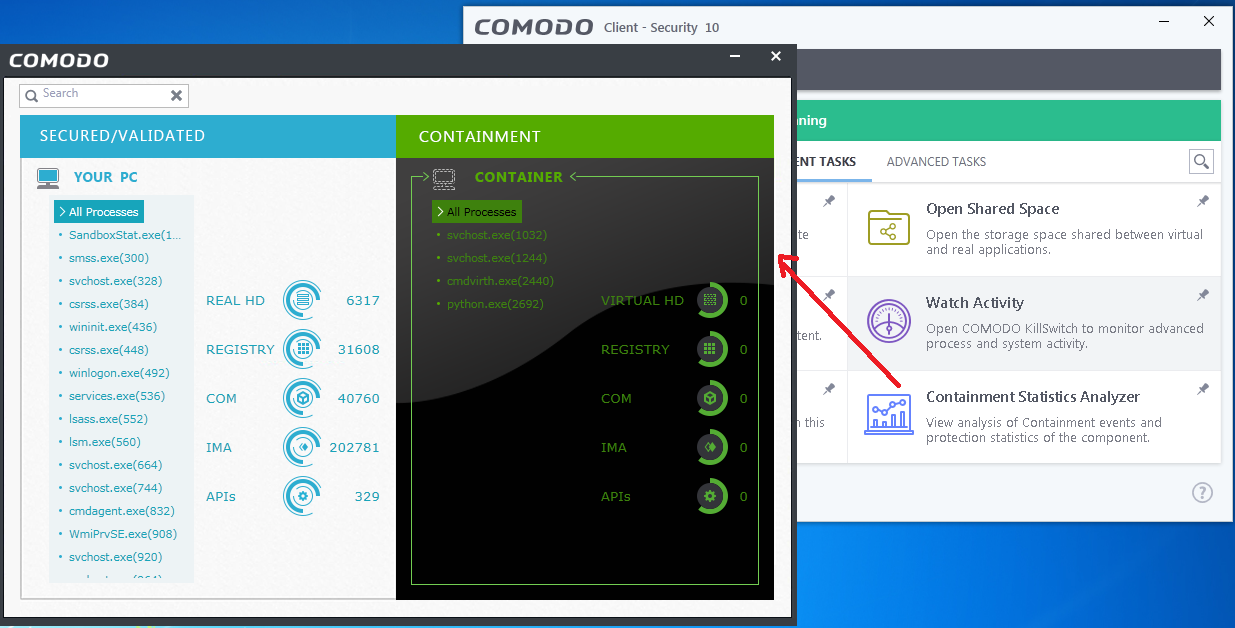
i)The process statistics details can be obtained together for all processes running in the system.
ii) If the statistics details are needed for any single process means it can also obtain by selecting that particular process from the list.
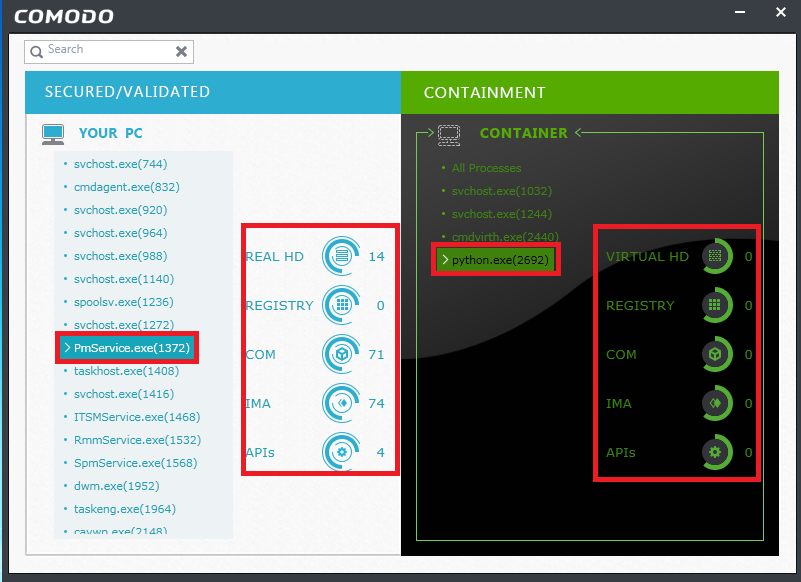
Secured/validated: This section displays the list of executables which are considered as trusted process/executables. These executables have full access permission to get executed in the PC.
The statistics available for this section are:
Real HD: Total memory space occupied by the process in the physical hard disk is shown.
Registry: Total number of modification made in the registry by the process are shown.
COM: Shows total number of services accessed which are provided by other processes.
IMA: Number of the directly accessed process are shown.
APIs: Number of sensitive Application programming interfaces(APIs) accessed by the process is shown.
Containment: This section displays the list of executables and process which are allowed to run in the separate virtual space (i.e.) container. These executables have limited access permission for execution
The statistics available for this section are:
Virtual HD: Total memory space occupied by the process in the shared space or virtual provided for containment
Registry: Total number of modification made in the registry by the contained process is shown
COM: Shows total number of services accessed which are provided by other processes
IMA: Number of the directly accessed process are shown.
APIs: Number of sensitive Application programming interfaces(APIs) accessed by the contained process are shown