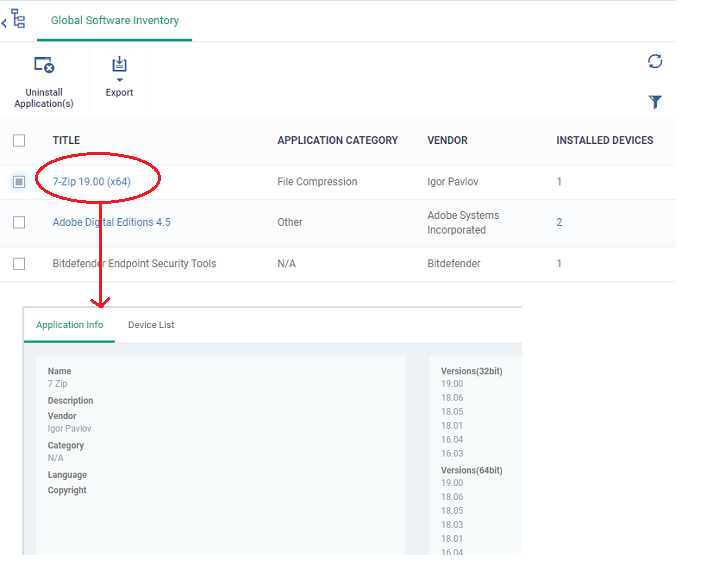
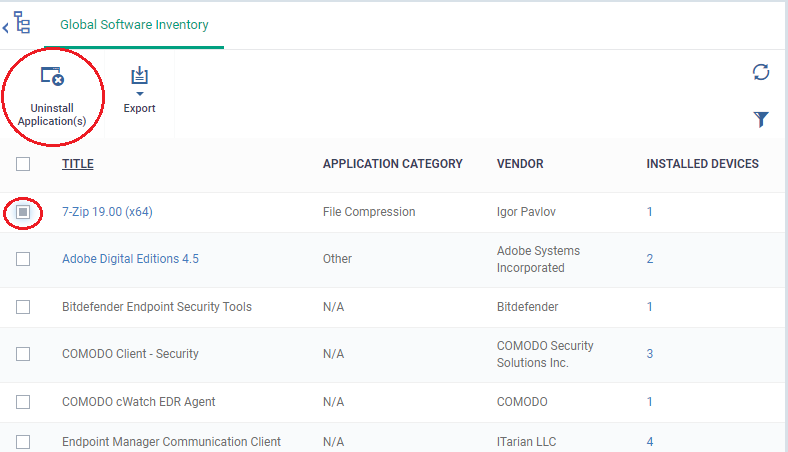
Click 'Applications' > 'Global Software Inventory'
- The communication client on each managed Windows device periodically scans the device for all installed applications. The checked locations include 'C:\Program Files\' and 'C:\Users\{user}\AppData\' folder to identify all applications installed on both default and other locations. The client and sends the details of the applications to Endpoint Manager.
- The global software inventory shows all applications installed on all Windows devices.
- The interface also shows details about each application. Details include the software vendor and the number of devices on which the app is installed.
- You can have the option to uninstall applications from selected Windows devices or all devices at-once
Use the links below to jump to the task you need help with:
The global software inventory interface
-
Log in to 'ITarian'
-
Click 'Applications' > 'Endpoint Manager'
-
Click 'Applications' on the left, then 'Global Software Inventory'

Title - Label of the application.
-
Click the name of an application to view its details and a list of endpoints on which it is installed.
-
The app details screens also lets you uninstall the application from devices.
-
See View details of an application for more details.
Application Category - The genre of the application. For example, 'Productivity', 'Security', 'Entertainment' etc.
Vendor - The publisher of the software/application
Installed Devices - The number of devices on which the app is installed currently.
View details of an application and devices installed with it
The 'Global Software Inventory' interface lets you view the information about an application and the list of devices on which it is found. You can also remove the application from selected devices on which it is not required.
Note: The application details is available only for applications supported by EM. See EM Supported 3rd Party Applications to view the list of supported applications.
View the details of an application
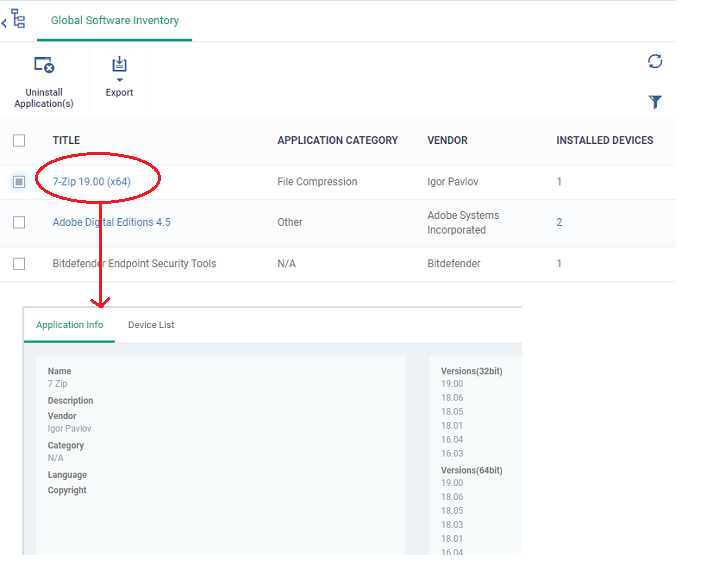
The application details interface contains two tabs:
-
Application Info - General information about the application. This includes a short description of the application, the vendor, category, the available versions and more.
-
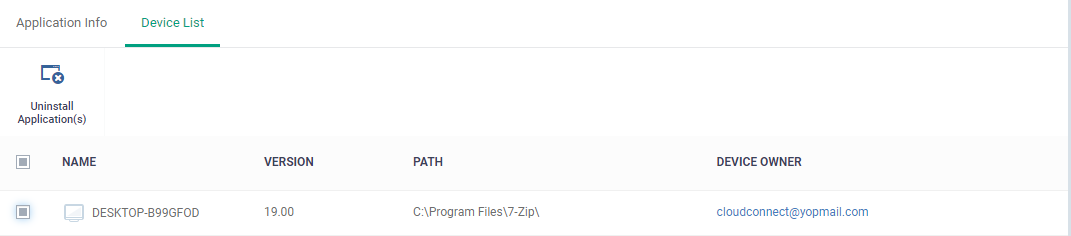
Device List - The devices on which the application was found installed. You can select the devices and uninstall the application from them.
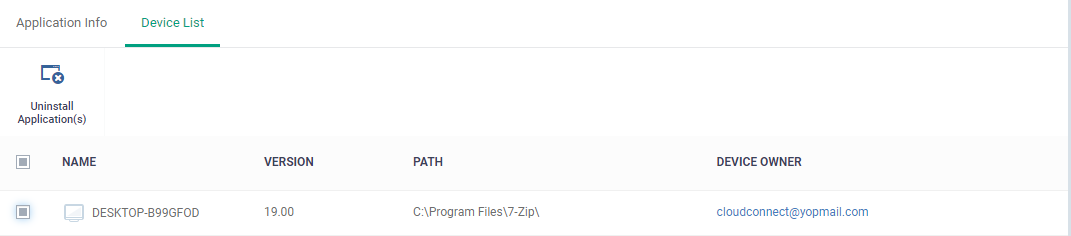
Name - The label of the Windows device.
Version - The version number of the application installed in the device
Path - The installation location of the application
Owner - The device user.
Uninstall an application from selected devices
Note: You can only remove applications that are supported by EM. See the list at EM Supported 3rd Party Applications.
-
Click 'Applications' > 'Global Software Inventory'
-
Click the name of an application to open its details interface
-
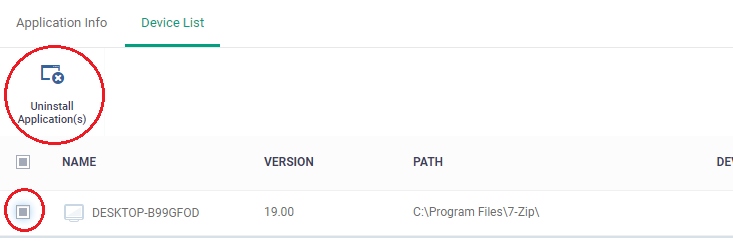
Click the 'Device List' tab
-
Select the devices and click the 'Uninstall' button at the top
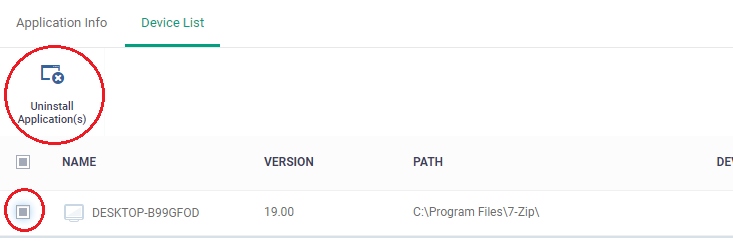
An uninstall command will be sent to the selected devices.
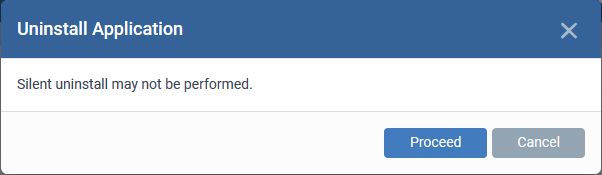
You will see the following message if the software cannot be uninstalled without notifying the device user:
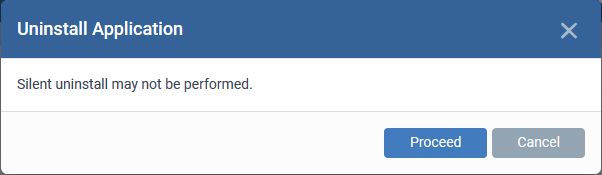
The application will be uninstalled from the selected devices.
Tip: You can remove apps from an individual device by using the device's details page. See this wiki page for help to do this.
Uninstall an application from all devices
Note: You can only remove applications that are supported by EM. See the list at EM Supported 3rd Party Applications.
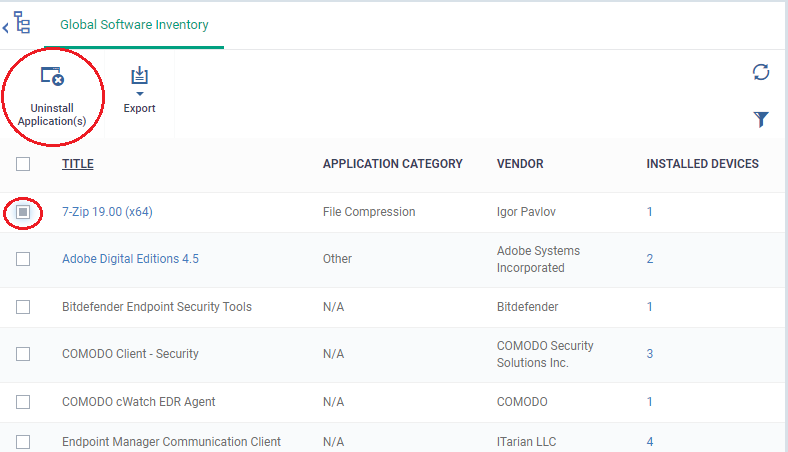
The uninstall command is sent to all devices which have the application installed.
You will see the following message if the software cannot be uninstalled without notifying the device user:
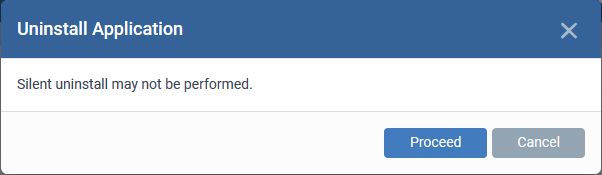
The application will be uninstalled from the selected devices.
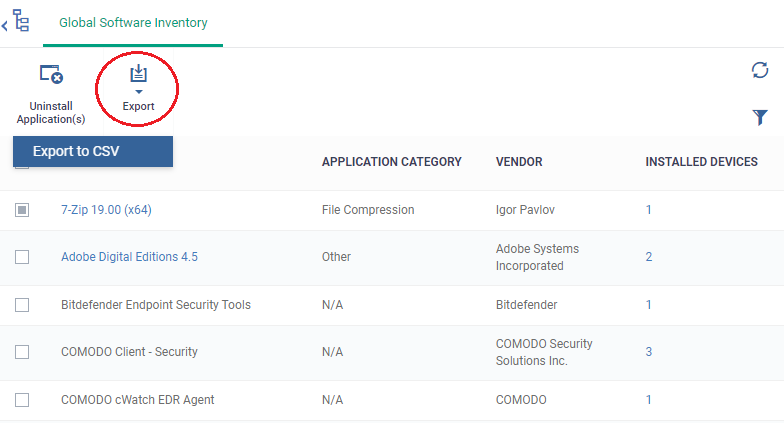
Export to CSV
- The Global Software Inventory can be exported to CSV
- The report will contain all the applications installed on managed Windows devices.
- Click 'Export’ > ‘Export to CSV’
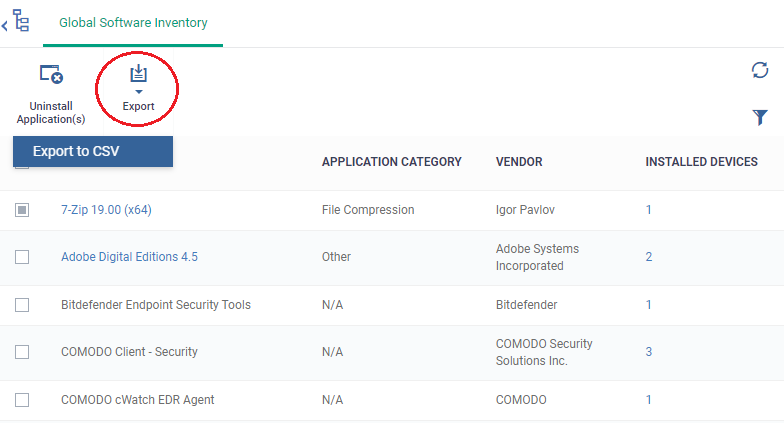
A confirmation message will be shown that report has been created.
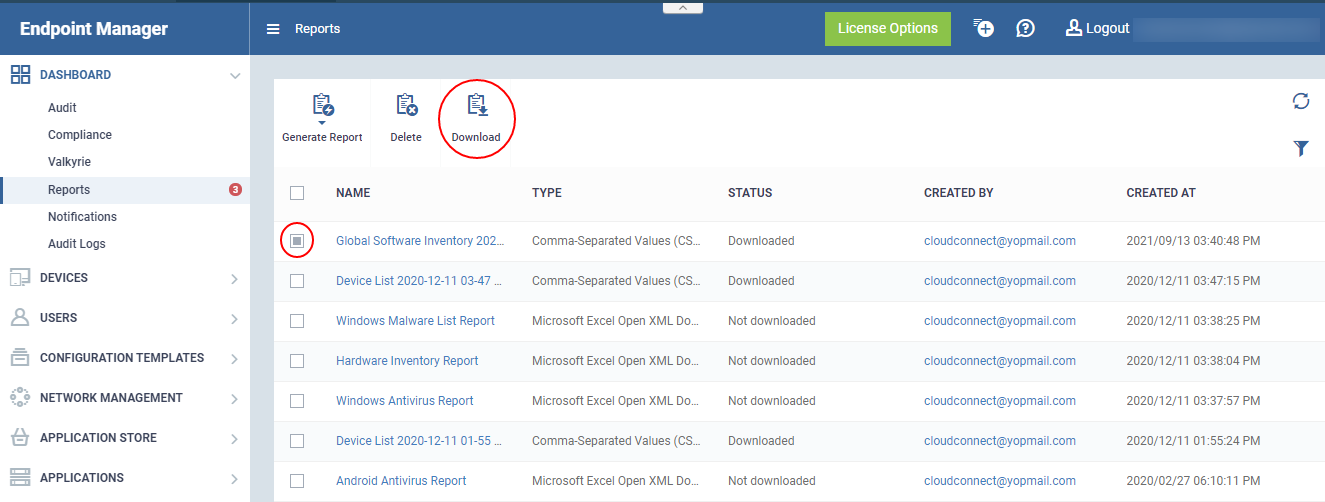
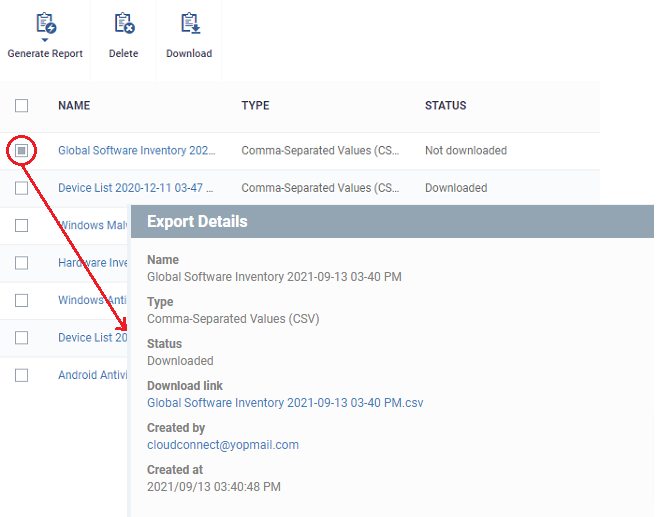
- To download the report click ‘Dashboard’ > ‘Reports’
- This page shows the list of all reports generated by the Endpoint Manager. To download a report, select it and click 'Download' at the top
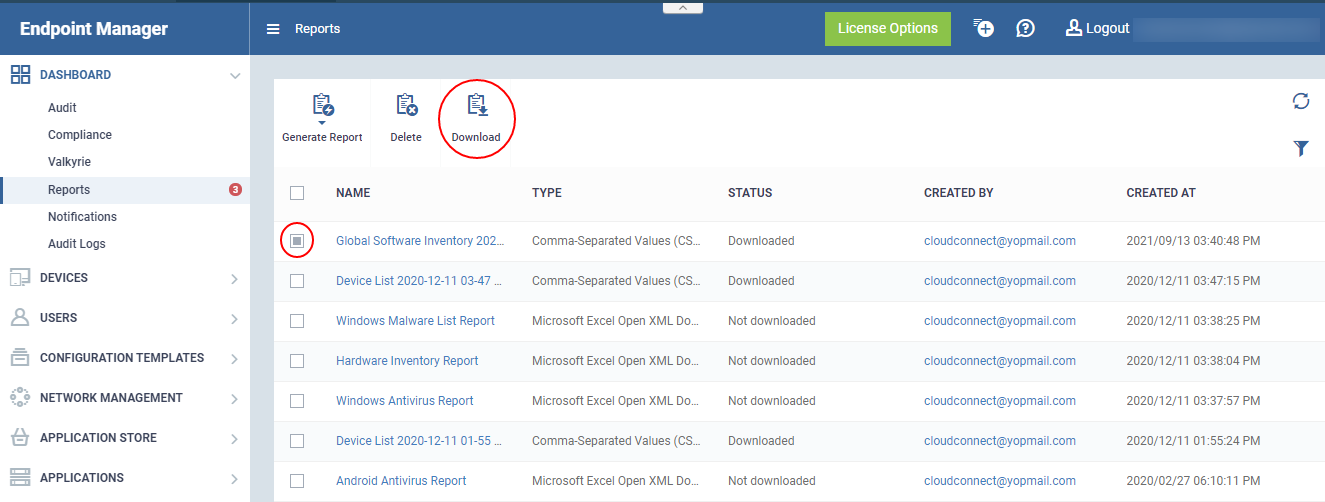
Or
- Click a report name to view details
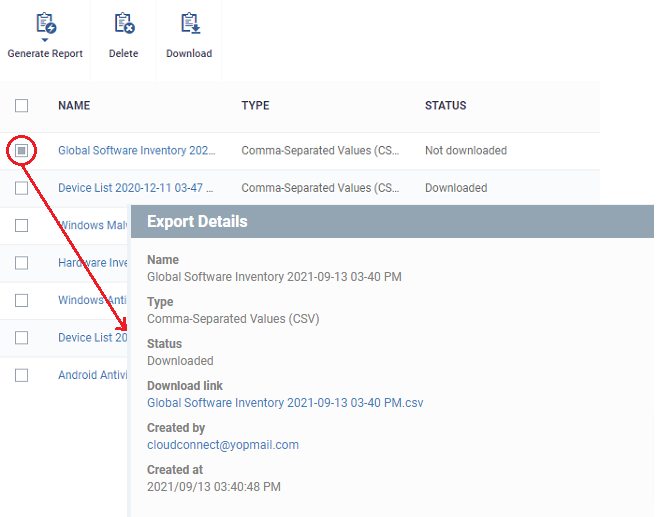
- Click the ‘Download link’ to download the report.
- To remove a report from the list, select it and click 'Delete'
- The report will be downloaded in the CSV format
Further reading:
How to push apps to Windows devices from the application store in Endpoint Manager
How to remotely uninstall third party applications from a Windows device