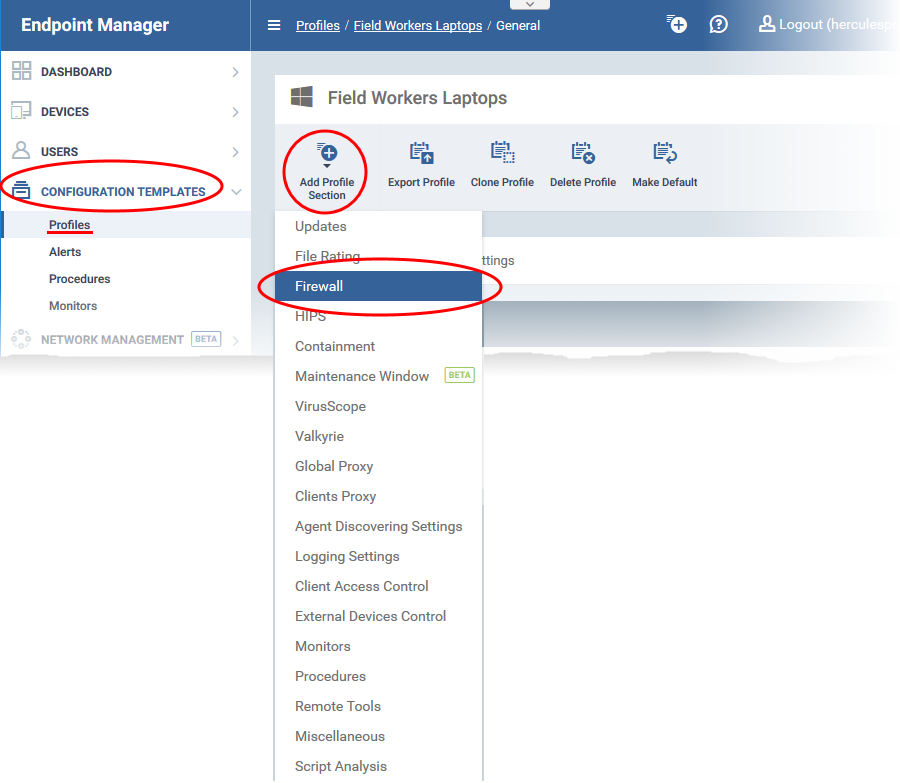
Click ‘Configuration Templates’ > ‘Profiles’ > click the name of a Windows profile > 'Add Profile Section' > 'Firewall'
- The 'Firewall' section of a Windows profile lets you create rules to manage internet access rights for Endpoint applications.
- You can create simple allow/block rules, or more complex rules based on traffic direction, traffic protocol, source/destination port, and more.
- This tutorial shows you how to create a file group of your target applications, then configure internet access rules for the group in a profile.
Click the links below to jump to the task you need help with:
Step 1 - Create a file group of the applications you want to manage
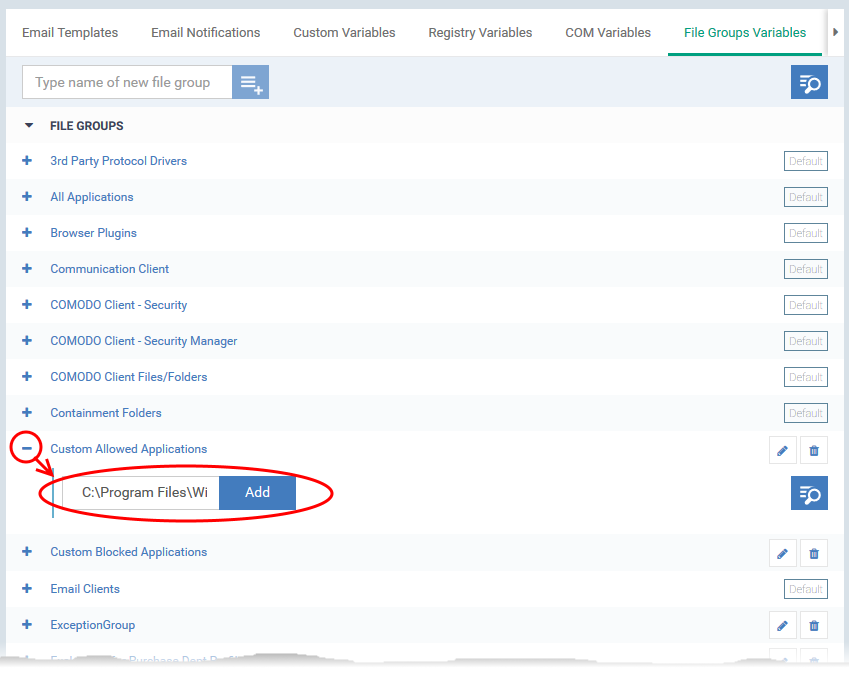
- File groups are collections of one or more files. You can select a file group as the target of firewall rules.
- Endpoint Manager ships with predefined groups of popular file types. For example, there are groups for ‘Windows updater applications’, ‘Web browsers’, ‘Email clients’ and ‘Metro Apps’.
- If none of the predefined groups cover your needs, you can create a custom file group that contains specific applications. You can then apply firewall rules to the group to control their internet access rights.
Create a file group
- Login to ITarian
- Click 'Applications' > 'Endpoint Manager'
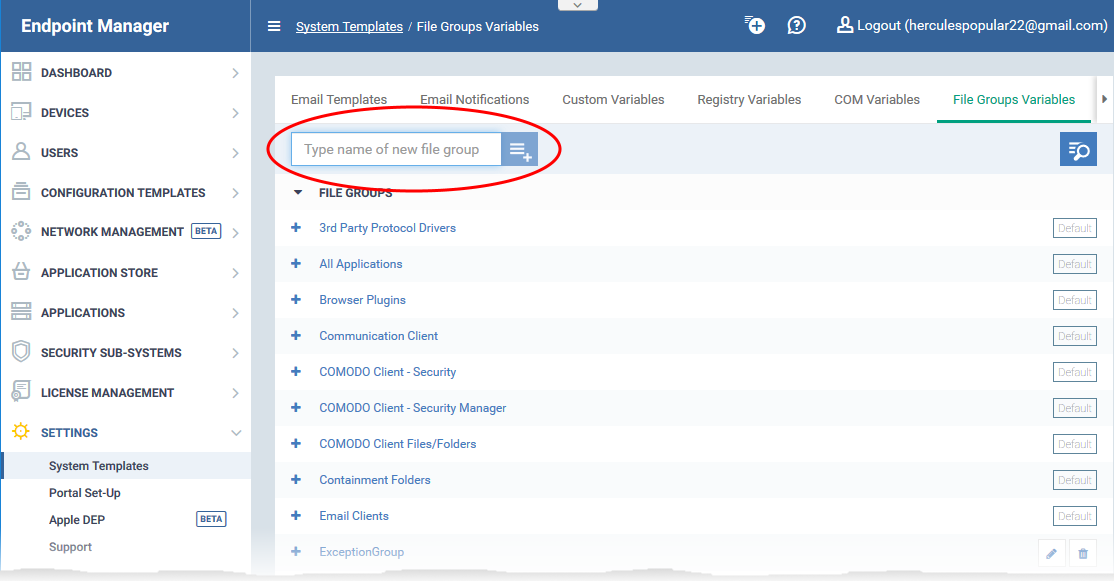
- Click 'Settings' > 'System Templates'
- Select the 'File Groups Variables' tab
- Create a name for the file group then click the
 button
button
Step 2 - Configure firewall rules for the group in a profile
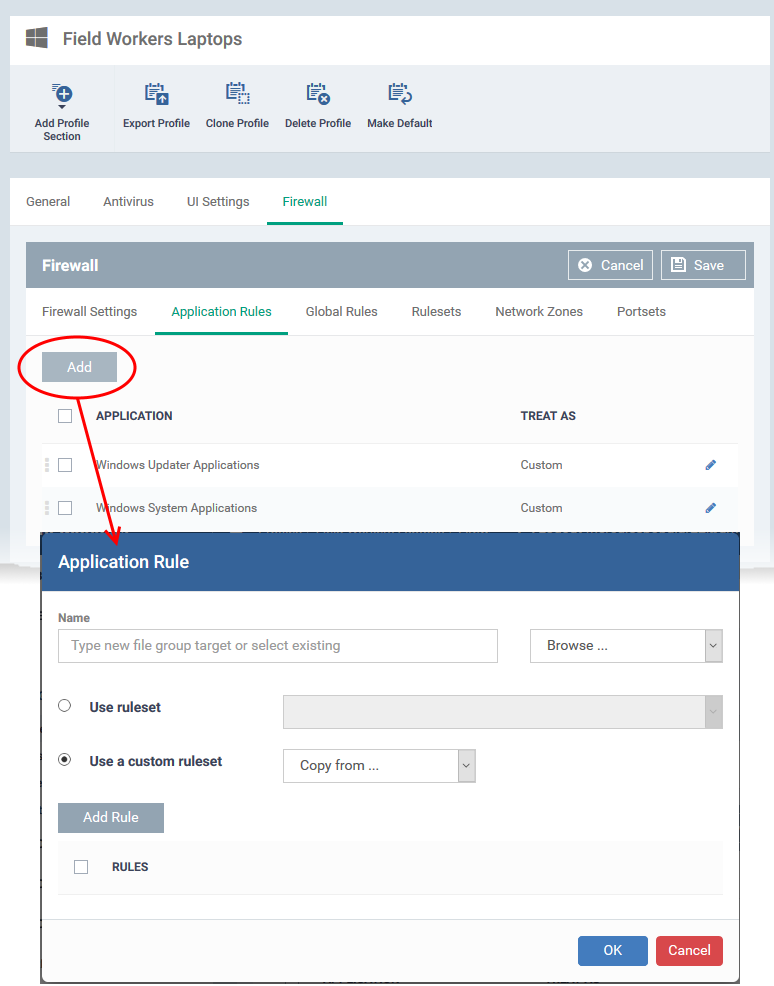
Use a pre-defined ruleset
- Pre-defined rulesets contain ‘already-configured’ rules that achieve specific aims, or are suited to specific application types. For example, there are rulesets for ‘Allowed applications’, ‘Blocked applications’, ‘Web browsers’ and ‘Email clients’.
- Open the ‘Ruleset’ tab of a firewall profile to view/manage the rules in each set.
- You can use an existing ruleset on your target applications if it meets your needs.
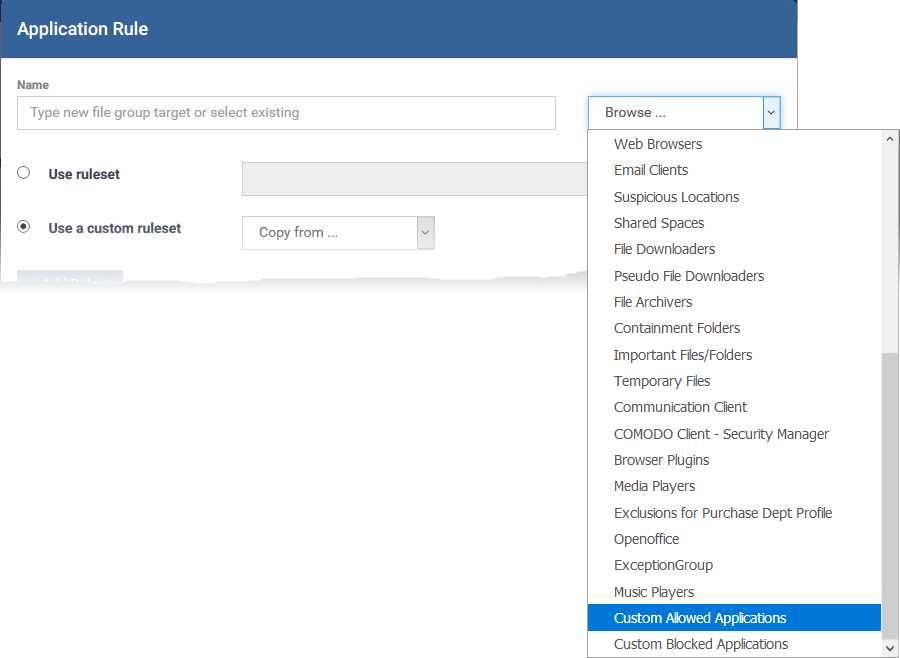
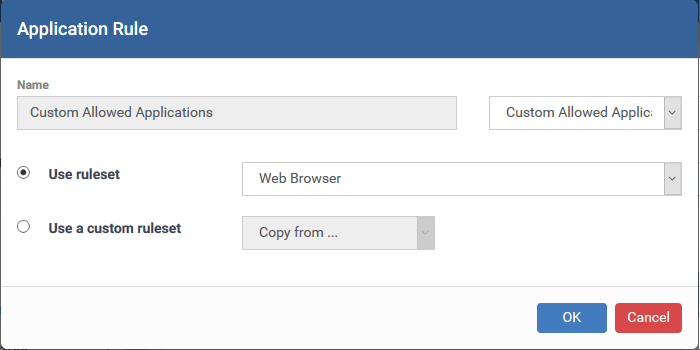
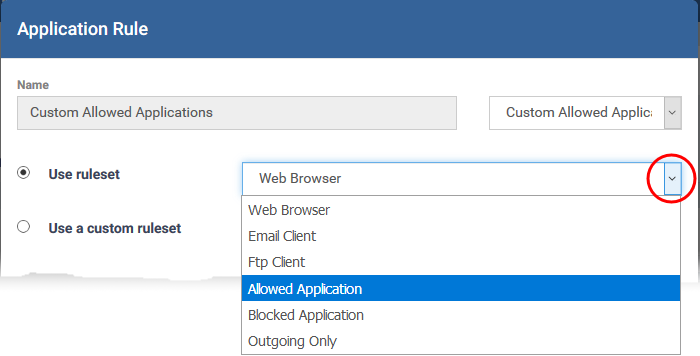
- Select 'Use ruleset':
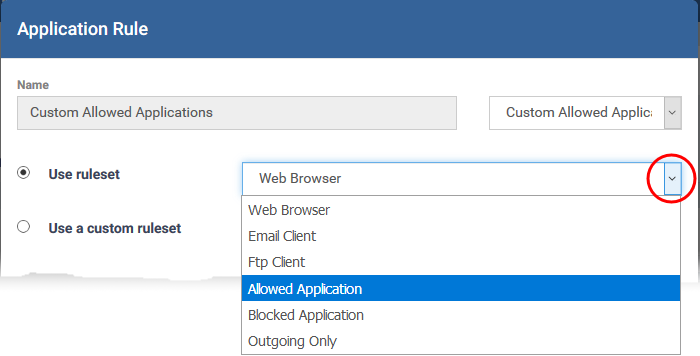
- Choose 'Allowed Application' or 'Blocked Application' as required. Or choose another ruleset if you want to implement more specific rules.
- Click 'OK'
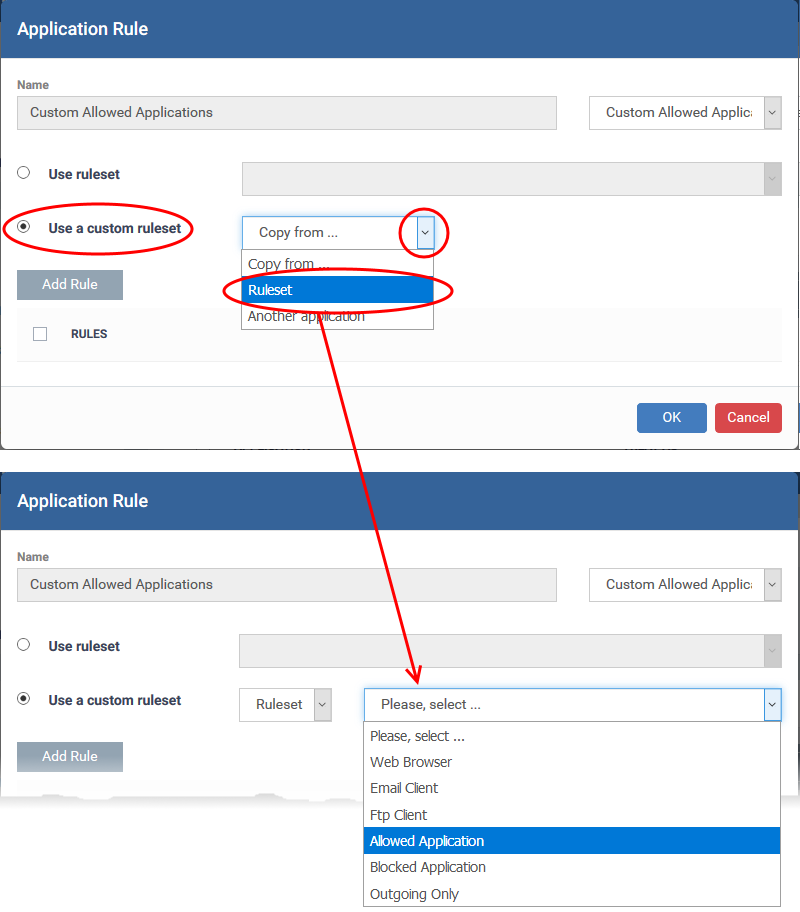
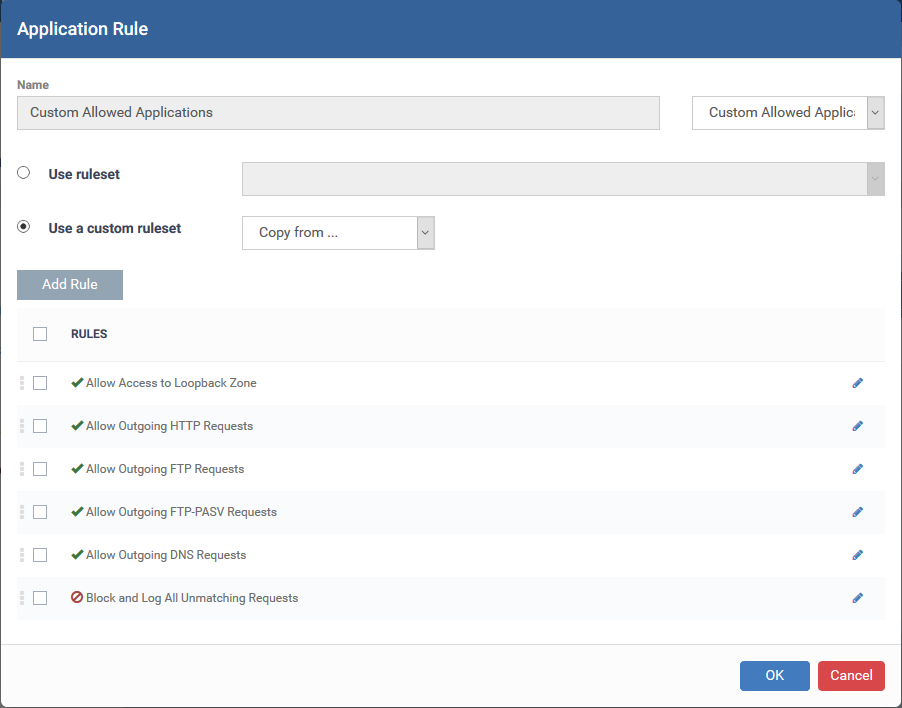
Use a custom ruleset
- Select 'Use a custom ruleset' in the rule dialog
- You can now manually create individual rules, or use the ‘Copy from...’ feature to import rules as a starting point.
- Click the pencil icon on the right to edit it as required
- Use the checkboxes on the left to enable or disable specific rules
- Click ‘OK’
- Click 'Save' in the firewall settings pane for your changes to take effect
Further reading:
How to configure general firewall settings in a Windows profile
How to add global rules to firewall in a Windows profile
How to create a custom firewall rule set in a Windows profile
How to configure network zones in a Windows profile
How to configure port sets in a Windows profile

 button
button