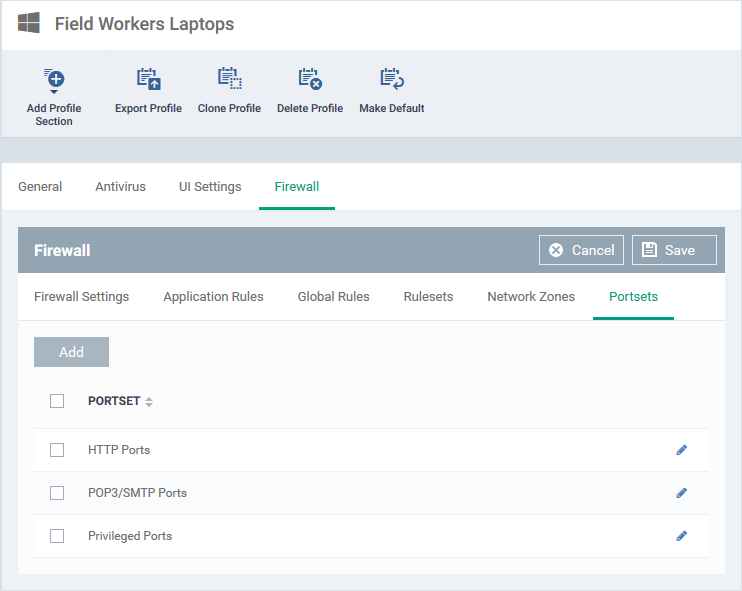
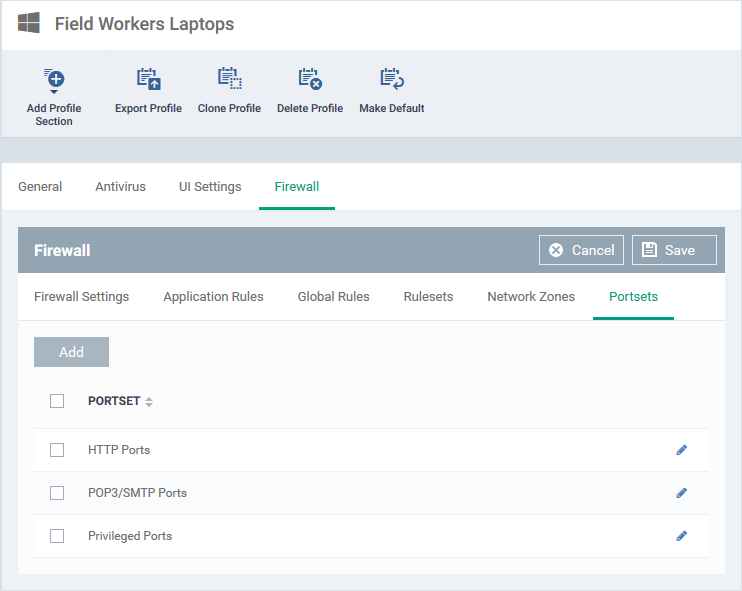
Click ‘Configuration Templates’ > ‘Profiles’ > click the name of a Windows profile > 'Add Profile Section' > 'Firewall' > 'Portsets'
-
A port set is a collection of one or more ports that you can reference in a firewall rule.
-
For example, you could create a group called ‘Outgoing Mail Ports’, which consists of port numbers 25, 465, 587, 2525 and 4065. You can then control traffic to all 5 ports by simply selecting the ‘Mail Ports’ group in a firewall rule.
-
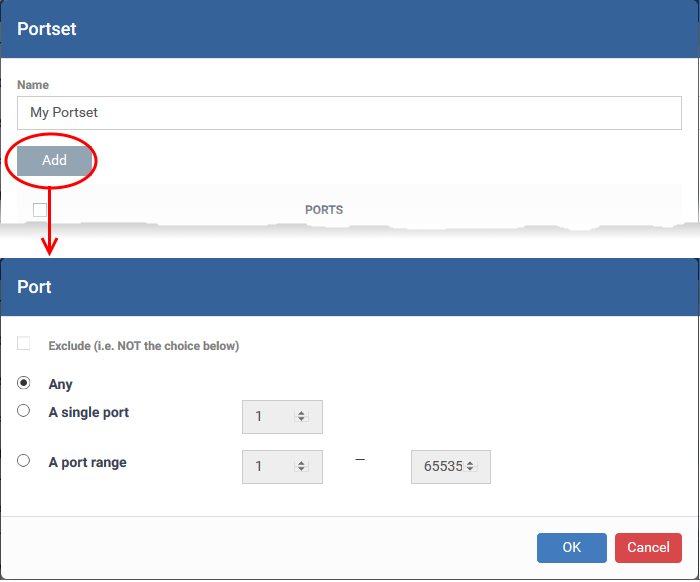
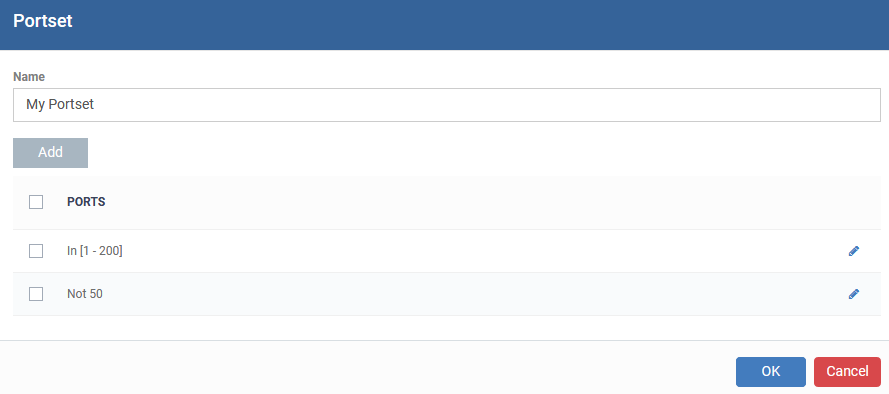
Portsets can be made up of individual port numbers or port ranges.
Manage Portsets
-
Click ‘Configuration Templates’ > ‘Profiles’
-
Open the Windows profile applied to your target devices
-
Click the 'Portsets' tab:
-
Endpoint Manager ships with three default portsets:
-
HTTP Ports: 80, 443 and 8080. These are the ports typically used for http traffic. Internet browsers uses these ports to connect to the internet.
-
POP3/SMTP Ports: 110, 25, 143, 995, 465 and 587. These ports are typically used to send/receive email. For example, by mail clients like Outlook and Thunderbird.
-
Privileged Ports: 0-1023. Privileged ports are so called because it is usually desirable to prevent users from running services on these ports. Network admins usually reserve or prohibit the use of these ports.
-
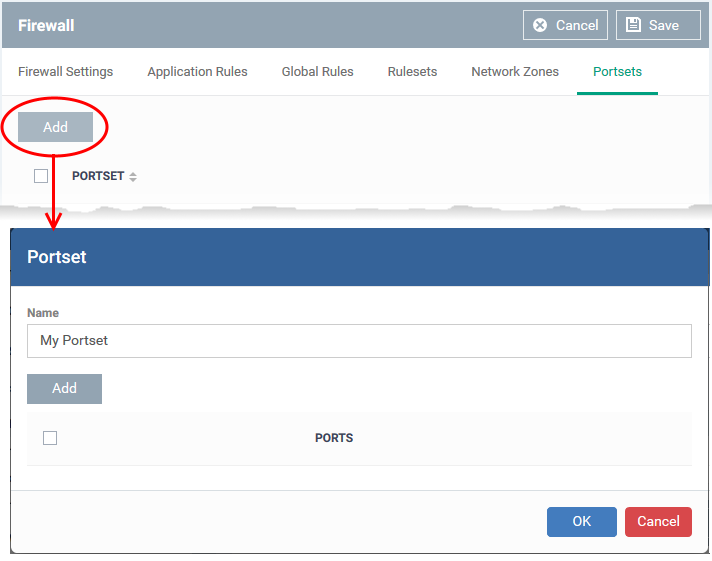
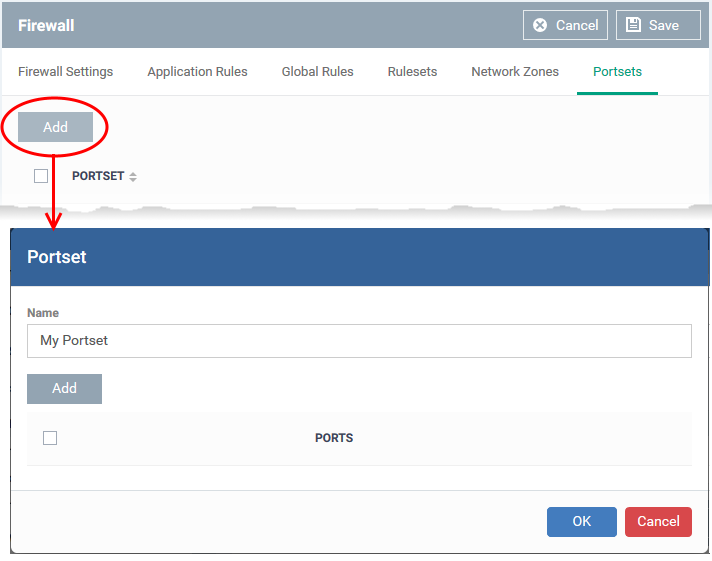
Click 'Add' to create a custom portset
-
Click 'Add' to specify the ports you want to include in the set:
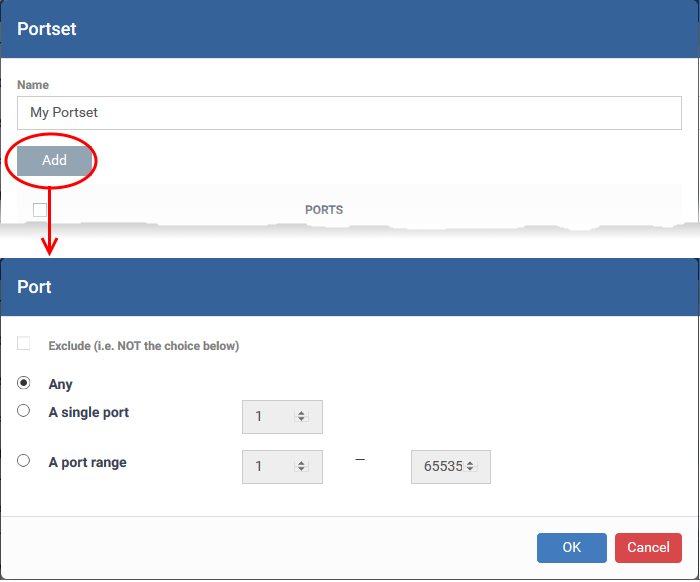
The portsets will be available for selection when you choose 'A set of ports' as source / destination port while creating or editing a firewall rule, to impose access restriction to the ports, on the devices applied with this profile.
Further Reading:
How to configure general firewall settings in a Windows profile
How to configure internet access rights for applications via Endpoint Manager
How to add global rules to firewall in a Windows profile
How to create a custom firewall rule set in a Windows profile
How to configure network zones in a Windows profile